
The Journal of Artificial Intelligence Research (JAIR) is dedicated to the rapid dissemination of important research results to the global artificial intelligence (AI) community. The journal’s scope encompasses all areas of AI, including agents and multi-agent systems, automated reasoning, constraint processing and search, knowledge representation, machine learning, natural language, planning and scheduling, robotics and vision, and uncertainty in AI.

Current Issue
Vol. 79 (2024)
Published: 2024-01-10
A Map of Diverse Synthetic Stable Matching Instances
Digcn: a dynamic interaction graph convolutional network based on learnable proposals for object detection, iterative train scheduling under disruption with maximum satisfiability, removing bias and incentivizing precision in peer-grading, cultural bias in explainable ai research: a systematic analysis, learning to resolve social dilemmas: a survey, a principled distributional approach to trajectory similarity measurement and its application to anomaly detection, multi-modal attentive prompt learning for few-shot emotion recognition in conversations, condense: conditional density estimation for time series anomaly detection, performative ethics from within the ivory tower: how cs practitioners uphold systems of oppression, learning logic specifications for policy guidance in pomdps: an inductive logic programming approach, multi-objective reinforcement learning based on decomposition: a taxonomy and framework, can fairness be automated guidelines and opportunities for fairness-aware automl, practical and parallelizable algorithms for non-monotone submodular maximization with size constraint, exploring the tradeoff between system profit and income equality among ride-hailing drivers, on mitigating the utility-loss in differentially private learning: a new perspective by a geometrically inspired kernel approach, an algorithm with improved complexity for pebble motion/multi-agent path finding on trees, weighted, circular and semi-algebraic proofs, reinforcement learning for generative ai: state of the art, opportunities and open research challenges, human-in-the-loop reinforcement learning: a survey and position on requirements, challenges, and opportunities, boolean observation games, detecting change intervals with isolation distributional kernel, query-driven qualitative constraint acquisition, visually grounded language learning: a review of language games, datasets, tasks, and models, right place, right time: proactive multi-robot task allocation under spatiotemporal uncertainty, principles and their computational consequences for argumentation frameworks with collective attacks, the ai race: why current neural network-based architectures are a poor basis for artificial general intelligence, undesirable biases in nlp: addressing challenges of measurement.
Advertisement
Artificial intelligence in cyber security: research advances, challenges, and opportunities
- Published: 13 March 2021
- Volume 55 , pages 1029–1053, ( 2022 )
Cite this article
- Zhimin Zhang ORCID: orcid.org/0000-0002-9065-8724 1 ,
- Huansheng Ning ORCID: orcid.org/0000-0001-6413-193X 1 , 2 ,
- Feifei Shi 1 ,
- Fadi Farha 1 ,
- Yang Xu 1 ,
- Jiabo Xu 3 ,
- Fan Zhang 1 &
- Kim-Kwang Raymond Choo ORCID: orcid.org/0000-0001-9208-5336 4
15k Accesses
73 Citations
24 Altmetric
Explore all metrics
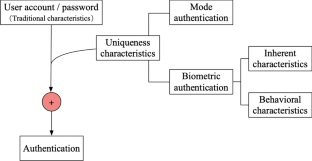
In recent times, there have been attempts to leverage artificial intelligence (AI) techniques in a broad range of cyber security applications. Therefore, this paper surveys the existing literature (comprising 54 papers mainly published between 2016 and 2020) on the applications of AI in user access authentication, network situation awareness, dangerous behavior monitoring, and abnormal traffic identification. This paper also identifies a number of limitations and challenges, and based on the findings, a conceptual human-in-the-loop intelligence cyber security model is presented.
This is a preview of subscription content, log in via an institution to check access.
Access this article
Price includes VAT (Russian Federation)
Instant access to the full article PDF.
Rent this article via DeepDyve
Institutional subscriptions
Similar content being viewed by others

Artificial Intelligence and Cybersecurity: Past, Presence, and Future
Artificial Intelligence for Cybersecurity: Recent Advancements, Challenges and Opportunities

A Comprehensive Review on Various Artificial Intelligence Based Techniques and Approaches for Cyber Security
Cloud adoption risk report 2019 (pdf). https://mscdss.ds.unipi.gr/wp-content/uploads/2018/10/Cloud-Adoption-Risk-Report-2019.pdf (2019).
What’s the difference between network security & cyber security? https://www.ecpi.edu/blog/whats-difference-between-network-security-cyber-security (2020).
Ai in cybersecurity-capgemini worldwide. https://www.capgemini.com/news/ai-in-cybersecurity/ (2020).
Ai index 2019 report (pdf). https://hai.stanford.edu/sites/g/files/sbiybj10986/f/ai_index_2019_report.pdf (2020).
Enterprise immune system-darktrace. https://www.darktrace.com/en/products/enterprise/ (2019).
Invincea launches x-as-a-service managed security. https://www.eweek.com/security/invincea-launches-x-as-a-service-managed-security (2020).
Congnigo-infosecurity magazine. https://www.infosecurity-magazine.com/directory/cognigo/ (2019).
Speech emotion recognition using semi-supervised learning with ladder networks. In: 2018 First Asian Conference on Affective Computing and Intelligent Interaction (ACII Asia), pp. 1–5 (2018).
Knowledge-directed artificial intelligence reasoning over schemas (kairos). https://www.darpa.mil/program/knowledge-directed-artificial-intelligence-reasoning-over-schemas (2020).
Darpa robotics challenge (DRC) using human-machine teamwork to perform disasterresponse with a humanoid robot. https://apps.dtic.mil/docs/citations/AD1027886 (2020).
Training ai to win a dogfight. https://www.darpa.mil/news-events/2019-05-08 (2020).
Cyborg super soldiers: Us army report reveals vision for deadly ‘machine humans’ with infrared sight, boosted strength and mind-controlled weapons by 2050. https://www.dailymail.co.uk/sciencetech/article-7738669/US-Military-scientists-create-plan-cyborg-super-soldier-future.html (2019).
Adekunle YA, Okolie SO, Adebayo AO, Ebiesuwa S, Ehiwe DD (2019) Holistic exploration of gaps vis-à-vis artificial intelligence in automated teller machine and internet banking. In: International journal of applied information systems (IJAIS), vol 12
Abdallah AE (2016) Detection and prediction of insider threats to cyber security: a systematic literature review and meta-analysis. Big Data Anal 1(1):6
Article Google Scholar
Ahmed M, Mahmood AN, Hu J (2015) A survey of network anomaly detection techniques. J. Netw. Comput. Appl. 60:19–31
Aljamal I, Tekeoğlu A, Bekiroglu K, Sengupta S (2019) Hybrid intrusion detection system using machine learning techniques in cloud computing environments. In: 2019 IEEE 17th international conference on software engineering research, management and applications (SERA), pp 84–89
Aljurayban NS, Emam A (2015) Framework for cloud intrusion detection system service. In: 2015 2nd world symposium on web applications and networking (WSWAN), pp 1–5
Amberkar A, Awasarmol P, Deshmukh G, Dave P (2018) Speech recognition using recurrent neural networks. In: 2018 international conference on current trends towards converging technologies (ICCTCT), pp 1–4
Bakhshi B, Veisi H (2019) End to end fingerprint verification based on convolutional neural network. In: 2019 27th Iranian conference on electrical engineering (ICEE), pp 1994–1998
Bao H, He H, Liu Z, Liu Z (2019) Research on information security situation awareness system based on big data and artificial intelligence technology. In: 2019 international conference on robots intelligent system (ICRIS), pp 318–322
Benias N, Markopoulos AP (2017) A review on the readiness level and cyber-security challenges in industry 4.0. In: 2017 south eastern European design automation, computer engineering, computer networks and social media conference (SEEDA-CECNSM), pp 1–5
Chang C, Eude T, Obando Carbajal LE (2016) Biometric authentication by keystroke dynamics for remote evaluation with one-class classification. In: Khoury R, Drummond C (eds) Advances in artificial intelligence. Springer, Cham, pp 21–32
Chapter Google Scholar
Deng M, Yang H, Cao J, Feng X (2019) View-invariant gait recognition based on deterministic learning and knowledge fusion. In: 2019 international joint conference on neural networks (IJCNN), pp 1–8
Ding C, Tao D (2018) Trunk-branch ensemble convolutional neural networks for video-based face recognition. IEEE Trans Pattern Anal Mach Intell 40(4):1002–1014
Dongmei Z, Jinxing L (2018) Study on network security situation awareness based on particle swarm optimization algorithm. Comput Ind Eng 125:764–775. https://doi.org/10.1016/j.cie.2018.01.006
Fairuz S, Habaebi MH, Elsheikh EMA (2018) Finger vein identification based on transfer learning of alexnet. In: 2018 7th international conference on computer and communication engineering (ICCCE), pp 465–469
Fernández Maimó L, Perales Gómez AL, García Clemente FJ, Gil Pérez M, Martínez Pérez G (2018) A self-adaptive deep learning-based system for anomaly detection in 5g networks. IEEE Access 6:7700–7712
Gangwar A, Joshi A (2016) Deepirisnet: deep iris representation with applications in iris recognition and cross-sensor iris recognition. In: 2016 IEEE international conference on image processing (ICIP), pp 2301–2305
Gu T, Dolan-Gavitt B, Garg S (2017) BadNets: identifying vulnerabilities in the machine learning model supply chain. ArXiv e-prints arXiv:1708.06733
Guan Y, Ge X (2018) Distributed attack detection and secure estimation of networked cyber-physical systems against false data injection attacks and jamming attacks. IEEE Trans Signal Inf Process Netw 4(1):48–59
MathSciNet Google Scholar
Han Z, Wang J (2019) Speech emotion recognition based on deep learning and kernel nonlinear PSVM. In: 2019 Chinese control and decision conference (CCDC), pp. 1426–1430
Hariyanto, Sudiro SA, Lukman S (2015) Minutiae matching algorithm using artificial neural network for fingerprint recognition. In: 2015 3rd international conference on artificial intelligence, modelling and simulation (AIMS), pp 37–41
Holzinger A, Plass M, Holzinger K, Crişan GC, Pintea CM, Palade V (2016) Towards interactive machine learning (IML): applying ant colony algorithms to solve the traveling salesman problem with the human-in-the-loop approach. In: Buccafurri F, Holzinger A, Kieseberg P, Tjoa AM, Weippl E (eds) Availability, reliability, and security in information systems. Springer, Cham, pp 81–95
Hong H, Lee M, Park K (2017) Convolutional neural network-based finger-vein recognition using nir image sensors. Sensors (Switzerland) 17:1297. https://doi.org/10.3390/s17061297
Hsieh C, Chan T (2016) Detection ddos attacks based on neural-network using apache spark. In: 2016 international conference on applied system innovation (ICASI), pp 1–4
Hu W, Tan Y (2017) Generating adversarial malware examples for black-box attacks based on gan. CoRR. http://arxiv.org/abs/1702.05983
Jenab K, Moslehpour S (2016) Cyber security management: a review. Soc. Bus. Manag. Dyn. 5(11):16–39
Google Scholar
Ji Y, Bowman B, Huang HH (2019) Securing malware cognitive systems against adversarial attacks. In: 2019 IEEE international conference on cognitive computing (ICCC), pp 1–9
Jyothi V, Wang X, Addepalli SK, Karri R (2016) Brain: behavior based adaptive intrusion detection in networks: Using hardware performance counters to detect ddos attacks. In: 2016 29th international conference on VLSI design and 2016 15th international conference on embedded systems (VLSID), pp 587–588
Sugandhi K, Raju G (2019) An efficient hog-centroid descriptor for human gait recognition. In: 2019 amity international conference on artificial intelligence (AICAI), pp 355–360
Kanimozhi, V, Jacob TP (2019) Artificial intelligence based network intrusion detection with hyper-parameter optimization tuning on the realistic cyber dataset cse-cic-ids2018 using cloud computing. In: 2019 international conference on communication and signal processing (ICCSP), pp 0033–0036
Kolosnjaji B, Demontis A, Biggio B, Maiorca D, Giacinto G, Eckert C, Roli F (2018) Adversarial malware binaries: evading deep learning for malware detection in executables. In: 2018 26th European signal processing conference (EUSIPCO), pp 533–537
Kong L, Huang G, Wu K (2017) Identification of abnormal network traffic using support vector machine. In: 2017 18th international conference on parallel and distributed computing, applications and technologies (PDCAT), pp 288–292
Kong L, Huang G, Wu K, Tang Q, Ye S (2018) Comparison of internet traffic identification on machine learning methods. In: 2018 international conference on big data and artificial intelligence (BDAI), pp 38–41
Kong L, Huang G, Zhou Y, Ye J (2018) Fast abnormal identification for large scale internet traffic. In: Proceedings of the 8th international conference on communication and network security, ICCNS 2018. Association for Computing Machinery, New York, pp 117–120 (2018). https://doi.org/10.1145/3290480.3290498
Korkmaz Y (2016) Developing password security system by using artificial neural networks in user log in systems. In: 2016 electric electronics, computer science, biomedical engineerings’ meeting (EBBT), pp 1–4
Kowert W (2017) The foreseeability of human-artificial intelligence interactions. Texas Law Rev 96:181–204
Kruse C, Frederick B, Jacobson T, Monticone D (2016) Cybersecurity in healthcare: a systematic review of modern threats and trends. Technol Health Care 25:1–10. https://doi.org/10.3233/THC-161263
Li C, Li XM (2017) Cyber performance situation awareness on fuzzy correlation analysis. In: 2017 3rd IEEE international conference on computer and communications (ICCC), pp 424–428
Li X, Zhang X, Wang D (2018) Spatiotemporal cyberspace situation awareness mechanism for backbone networks. In: 2018 4th international conference on big data computing and communications (BIGCOM), pp 168–173
Liu W, Li W, Sun L, Zhang L, Chen P (2017) Finger vein recognition based on deep learning. In: 2017 12th IEEE conference on industrial electronics and applications (ICIEA), pp 205–210
Lu X, Xiao L, Xu T, Zhao Y, Tang Y, Zhuang W (2020) Reinforcement learning based PHY authentication for Vanets. IEEE Trans Veh Technol 69(3):3068–3079
Lu Y, Xu LD (2019) Internet of things (IoT) cybersecurity research: a review of current research topics. IEEE Internet Things J 6(2):2103–2115
Mahmood T, Afzal U (2013) Security analytics: big data analytics for cybersecurity: a review of trends, techniques and tools. In: 2013 2nd national conference on information assurance (NCIA), pp 129–134
Marir N, Wang H, Feng G, Li B, Jia M (2018) Distributed abnormal behavior detection approach based on deep belief network and ensemble SVM using spark. IEEE Access 6:59657–59671
McIntire JP, McIntire LK, Havig PR (2009) A variety of automated turing tests for network security: Using ai-hard problems in perception and cognition to ensure secure collaborations. In: 2009 international symposium on collaborative technologies and systems, pp 155–162
Naderpour M, Lu J, Zhang G (2014) An intelligent situation awareness support system for safety-critical environments. Decis Support Syst 59:325–340. https://doi.org/10.1016/j.dss.2014.01.004
Nithyakani P, Shanthini A, Ponsam G (2019) Human gait recognition using deep convolutional neural network. In: 2019 3rd international conference on computing and communications technologies (ICCCT), pp 208–211
Nunes DS, Zhang P, Sá Silva J (2015) A survey on human-in-the-loop applications towards an internet of all. IEEE Commun Surv Tutor 17(2):944–965
Ozsen S, Gunes S, Kara S, Latifoglu F (2009) Use of kernel functions in artificial immune systems for the nonlinear classification problems. IEEE Trans Inf Technol Biomed 13(4):621–628
Pandeeswari N, Kumar G (2016) Anomaly detection system in cloud environment using fuzzy clustering based ANN. Mob Netw Appl 21(3):494–505
Parthasarathy S, Busso C (2019) Semi-supervised speech emotion recognition with ladder networks. IEEE/ACM Trans Audio, Speech, Lang Process 28:2697–2709
Păvăloi L, Niţă CD (2018) Iris recognition using sift descriptors with different distance measures. In: 2018 10th international conference on electronics, computers and artificial intelligence (ECAI), pp 1–4
Qiu M (2017) Keystroke biometric systems for user authentication. J Signal Process Syst 86(2–3):175–190
Saeed F, Hussain M, Aboalsamh HA (2018) Classification of live scanned fingerprints using histogram of gradient descriptor. In: 2018 21st Saudi computer society national computer conference (NCC), pp 1–5
Salyut J, Kurnaz C (2018) Profile face recognition using local binary patterns with artificial neural network. In: 2018 international conference on artificial intelligence and data processing (IDAP), pp 1–4
Santhanam GR, Holland B, Kothari S, Ranade N (2017) Human-on-the-loop automation for detecting software side-channel vulnerabilities. In: Shyamasundar RK, Singh V, Vaidya J (eds) Information systems security. Springer, Cham, pp 209–230
Schlegel U, Arnout H, El-Assady M, Oelke D, Keim DA (2019) Towards a rigorous evaluation of xai methods on time series. In: 2019 IEEE/CVF international conference on computer vision workshop (ICCVW), pp 4197–4201
Shelton J, Jenkins J, Roy K (2016) Micro-dimensional feature extraction for multispectral iris recognition. SoutheastCon 2016:1–5
Shi Y, Li T, Renfa L, Peng X, Tang P (2017) An immunity-based iot environment security situation awareness model. J Comput Commun 5:182–197. https://doi.org/10.4236/jcc.2017.57016
Shoufan A (2017) Continuous authentication of uav flight command data using behaviometrics. In: 2017 IFIP/IEEE international conference on very large scale integration (VLSI-SoC), pp 1–6
Singh K, Kumar J, Tripathi G, Chullai GA (2017) Sparse proximity based robust fingerprint recognition. In: 2017 international conference on computing, communication and automation (ICCCA), pp 1025–1028
Sliti M, Abdallah W, Boudriga N (2018) Jamming attack detection in optical uav networks. In: 2018 20th international conference on transparent optical networks (ICTON), pp 1–5
Su J, Vargas DV, Sakurai K (2019) One pixel attack for fooling deep neural networks. IEEE Trans Evolut Comput 23(5):828–841
Taylor PJ, Dargahi T, Dehghantanha A, Parizi RM, Choo KKR (2019) A systematic literature review of blockchain cyber security. Digit Commun Netw 6(2):147–156
Thongsook A, Nunthawarasilp T, Kraypet P, Lim J, Ruangpayoongsak N (2019) C4.5 decision tree against neural network on gait phase recognition for lower limp exoskeleton. In: 2019 1st international symposium on instrumentation, control, artificial intelligence, and robotics (ICA-SYMP), pp 69–72
Tyworth M, Giacobe NA, Mancuso VF, McNeese MD, Hall DL (2013) A human-in-the-loop approach to understanding situation awareness in cyber defence analysis. EAI End Trans Secur Saf. https://doi.org/10.4108/trans.sesa.01-06.2013.e6
Uddin MZ, Khaksar W, Torresen J (2017) A robust gait recognition system using spatiotemporal features and deep learning. In: 2017 IEEE international conference on multisensor fusion and integration for intelligent systems (MFI), pp 156–161
Veeramachaneni K, Arnaldo I, Korrapati V, Bassias C, Li K (2016) Ai \(\hat{2}\) : Training a big data machine to defend. In: 2016 IEEE 2nd international conference on big data security on cloud (BigDataSecurity), IEEE international conference on high performance and smart computing (HPSC), and IEEE international conference on intelligent data and security (IDS), pp 49–54
Verma M, Vipparthi SK, Singh G (2019) Hinet: hybrid inherited feature learning network for facial expression recognition. IEEE Lett Comput Soc 2(4):36–39
Wang Z, Fang B (2019) Application of combined kernel function artificial intelligence algorithm in mobile communication network security authentication mechanism. J Supercomput 75(9):5946–5964
Wang ZJ, Turko R, Shaikh O, Park H, Das N, Hohman F, Kahng M, Chau DH (2020) CNN explainer: learning convolutional neural networks with interactive visualization. IEEE Trans Vis Comput Gr. https://doi.org/10.1109/TVCG.2020.3030418
Xiao R, Zhu H, Song C, Liu X, Dong J, Li H (2018) Attacking network isolation in software-defined networks: New attacks and countermeasures. In: 2018 27th international conference on computer communication and networks (ICCCN), pp 1–9
Yang H, Jia Y, Han WH, Nie YP, Li SD, Zhao XJ (2019) Calculation of network security index based on convolution neural networks, pp 530–540. https://doi.org/10.1007/978-3-030-24271-8_47
Yang W, Wang S, Hu J, Zheng G, Yang J, Valli C (2019) Securing deep learning based edge finger vein biometrics with binary decision diagram. IEEE Trans Ind Inform 15(7):4244–4253
Yavanoglu O, Aydos M (2017) A review on cyber security datasets for machine learning algorithms. In: 2017 IEEE international conference on big data (big data), pp 2186–2193
Young Park C, Blackmond Laskey K, Costa PCG, Matsumoto S (2016) A process for human-aided multi-entity bayesian networks learning in predictive situation awareness. In: 2016 19th international conference on information fusion (FUSION), pp 2116–2124
Yuan X, Li C, Li X (2017) Deepdefense: identifying ddos attack via deep learning. In: 2017 IEEE international conference on smart computing (SMARTCOMP), pp 1–8
Yunhu Jin, Shen Y, Zhang G, Hua Zhi (2016) The model of network security situation assessment based on random forest. In: 2016 7th IEEE international conference on software engineering and service science (ICSESS), pp 977–980
Zeng J, Wang F, Deng J, Qin C, Zhai Y, Gan J, Piuri V (2020) Finger vein verification algorithm based on fully convolutional neural network and conditional random field. IEEE Access 8:65402–65419
Zeng Y, Qi Z, Chen W, Huang Y, Zheng X, Qiu H (2019) Test: an end-to-end network traffic examination and identification framework based on spatio-temporal features extraction. CoRR. http://arxiv.org/abs/1908.10271
Zhang W, Lu X, Gu Y, Liu Y, Meng X, Li J (2019) A robust iris segmentation scheme based on improved u-net. IEEE Access 7:85082–85089
Zhang Y, Chen X, Guo D, Song M, Teng Y, Wang X (2019) PCCN: Parallel cross convolutional neural network for abnormal network traffic flows detection in multi-class imbalanced network traffic flows. IEEE Access 7:119904–119916
Zhang Y, Li W, Zhang L, Ning X, Sun L, Lu Y (2019) Adaptive learning Gabor filter for finger-vein recognition. IEEE Access 7:159821–159830
Zhang Z, Shi F, Wan Y, Xu Y, Zhang F, Ning H (2020) Application progress of artificial intelligence in military confrontation. Chin J Eng 42(9):1106–1118. https://doi.org/10.13374/j.issn2095-9389.2019.11.19.001
Download references
Acknowledgements
This work was funded by the National Natural Science Foundation of China (Grant No. 61872038). This work of K.-K. R. Choo was supported only by the Cloud Technology Endowed Professorship.
Author information
Authors and affiliations.
School of Computer and Communication Engineering, University of Science and Technology Beijing, Beijing, 100083, China
Zhimin Zhang, Huansheng Ning, Feifei Shi, Fadi Farha, Yang Xu & Fan Zhang
Beijing Engineering Research Center for Cyberspace Data Analysis and Applications, Beijing, 100083, China
Huansheng Ning
School of Information Engineering, Xinjiang Institute of Engineering, Xinjiang, China
Department of Information Systems and Cyber Security, University of Texas at San Antonio, San Antonio, TX, 78249-0631, USA
Kim-Kwang Raymond Choo
You can also search for this author in PubMed Google Scholar
Corresponding author
Correspondence to Huansheng Ning .
Additional information
Publisher's note.
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Reprints and permissions
About this article
Zhang, Z., Ning, H., Shi, F. et al. Artificial intelligence in cyber security: research advances, challenges, and opportunities. Artif Intell Rev 55 , 1029–1053 (2022). https://doi.org/10.1007/s10462-021-09976-0
Download citation
Published : 13 March 2021
Issue Date : February 2022
DOI : https://doi.org/10.1007/s10462-021-09976-0
Share this article
Anyone you share the following link with will be able to read this content:
Sorry, a shareable link is not currently available for this article.
Provided by the Springer Nature SharedIt content-sharing initiative
- Cyber Security
- Artificial Intelligence
- Security Methods
- Human-in-the-Loop
- Find a journal
- Publish with us
- Track your research
AI Index Report
The AI Index Report tracks, collates, distills, and visualizes data related to artificial intelligence. Our mission is to provide unbiased, rigorously vetted, broadly sourced data in order for policymakers, researchers, executives, journalists, and the general public to develop a more thorough and nuanced understanding of the complex field of AI. The report aims to be the world’s most credible and authoritative source for data and insights about AI.
Read the 2023 AI Index Report
Coming Soon: 2024 AI Index Report!
The 2024 AI Index Report will be out April 15! Sign up for our mailing list to receive it in your inbox.
Steering Committee Co-Directors

Ray Perrault
Steering committee members.

Erik Brynjolfsson

John Etchemendy

Katrina Ligett

Terah Lyons

James Manyika


Juan Carlos Niebles

Vanessa Parli

Yoav Shoham

Russell Wald
Staff members.

Loredana Fattorini

Nestor Maslej
Letter from the co-directors.
AI has moved into its era of deployment; throughout 2022 and the beginning of 2023, new large-scale AI models have been released every month. These models, such as ChatGPT, Stable Diffusion, Whisper, and DALL-E 2, are capable of an increasingly broad range of tasks, from text manipulation and analysis, to image generation, to unprecedentedly good speech recognition. These systems demonstrate capabilities in question answering, and the generation of text, image, and code unimagined a decade ago, and they outperform the state of the art on many benchmarks, old and new. However, they are prone to hallucination, routinely biased, and can be tricked into serving nefarious aims, highlighting the complicated ethical challenges associated with their deployment.
Although 2022 was the first year in a decade where private AI investment decreased, AI is still a topic of great interest to policymakers, industry leaders, researchers, and the public. Policymakers are talking about AI more than ever before. Industry leaders that have integrated AI into their businesses are seeing tangible cost and revenue benefits. The number of AI publications and collaborations continues to increase. And the public is forming sharper opinions about AI and which elements they like or dislike.
AI will continue to improve and, as such, become a greater part of all our lives. Given the increased presence of this technology and its potential for massive disruption, we should all begin thinking more critically about how exactly we want AI to be developed and deployed. We should also ask questions about who is deploying it—as our analysis shows, AI is increasingly defined by the actions of a small set of private sector actors, rather than a broader range of societal actors. This year’s AI Index paints a picture of where we are so far with AI, in order to highlight what might await us in the future.
- Jack Clark and Ray Perrault
Our Supporting Partners
Analytics & Research Partners

Stay up to date on the AI Index by subscribing to the Stanford HAI newsletter.
Help | Advanced Search
Computer Science > Computation and Language
Title: artificial intelligence and the spatial documentation of languages.
Abstract: The advancement in technology has made interdisciplinary research more accessible. Particularly the breakthrough in Artificial Intelligence AI has given huge advantages to researchers working in interdisciplinary and multidisciplinary fields. This study investigates the ability of AI models, particularly GPT4 and GPT Data Analyst in creating language maps for language documentation. The study Integrates documentary linguistics linguistic geography and AI by showcasing how AI models facilitate the spatial documentation of languages through the creation of language maps with minimal cartographic expertise. The study is conducted using a CSV file and a GeoJSON file both obtained from HDX and from the researchers fieldwork. The study data is then applied in realtime conversations with the AI models in order to generate the language distribution maps. The study highlights the two AI models capabilities in generating highquality static and interactive web maps and streamlining the mapmaking process, despite facing challenges like inconsistencies and difficulties in adding legends. The findings suggest a promising future for AI in generating language maps and enhancing the work of documentary linguists as they collect their data in the field pointing towards the need for further development to fully harness AI potential in this field.
Submission history
Access paper:.
- Other Formats
References & Citations
- Google Scholar
- Semantic Scholar
BibTeX formatted citation
Bibliographic and Citation Tools
Code, data and media associated with this article, recommenders and search tools.
- Institution
arXivLabs: experimental projects with community collaborators
arXivLabs is a framework that allows collaborators to develop and share new arXiv features directly on our website.
Both individuals and organizations that work with arXivLabs have embraced and accepted our values of openness, community, excellence, and user data privacy. arXiv is committed to these values and only works with partners that adhere to them.
Have an idea for a project that will add value for arXiv's community? Learn more about arXivLabs .
- Support Our Work
- Carr Center Advisory Board
- Technology & Human Rights
- Racial Justice
- Transitional Justice
- Reimagining Rights & Responsibilities
- Human Rights Defenders
- In Conversation
- Justice Matters Podcast
- News and Announcements
- Student Opportunities
- Fellowship Opportunities

Carr Center for Human Rights Policy
The Carr Center for Human Rights Policy serves as the hub of the Harvard Kennedy School’s research, teaching, and training in the human rights domain. The center embraces a dual mission: to educate students and the next generation of leaders from around the world in human rights policy and practice; and to convene and provide policy-relevant knowledge to international organizations, governments, policymakers, and businesses.
About the Carr Center
Since its founding in 1999, the Carr Center has dedicated the last quarter-century to human rights policy.

March 25, 2024 Making a Movement: Gaurab Basu on How Climate Change Threatens Our Human Rights
February 22, 2024 How Feminist Foreign Policies Work to Enhance Gender Justice Kathryn Sikkink , Helen Clapp
March 18, 2024 Making a Movement: Yanilda María González on Police Violence Against Racialized Communities
March 08, 2024 Women's History Month: The Justice Matters Podcast
February 16, 2024 Game Over Albert Fox Cahn, Evan Enzer
February 27, 2024 Rights, Systematicity, and Misinformation
January 30, 2024 Does AI Understand Arabic?
December 10, 2023 Making a Movement Linda Bilmes , Soroush Saghafian , Iris Bohnet , John Donahue , Jay Rosengard , John Haigh , Jason Furman , Jeffrey Frankel , Mark Fagan , Archon Fung , Sheila Jasanoff , Henry Lee , Jane Nelson , Mathias Risse
A Human Rights-Based Approach to Mental Health
Bevin Croft and Ebony Flint from the Human Services Research Institute discuss mental health and human rights in the wake of new guidance issued in 2023 by the WHO.
Human Rights and Indigenous Rights in New Zealand
Claire Charters discusses the status of Māori representation in New Zealand's government, the right-wing pushback against indigenous rights, and more.
See All Justice Matters Episodes
View and listen to all of the Justice Matters podcast episodes in one place.
The Human Rights Violations of Abortion Bans
A discussion of the human rights violations caused by the reversal of Roe v. Wade and the move to ban abortion in the United States.
The UN Business & Human Rights Forum
A deep dive into the United Nations Forum on Business and Human Rights, which wrapped up its 12th iteration at the end of 2023.
A New Civil Rights Movement
Jill Collen Jefferson, a civil and human rights lawyer and founder of Julian, discusses drawing on international human rights movements to build a civil rights strategy in the United States.
Just Hierarchy
Daniel A. Bell, Chair of Political Theory with the Faculty of Law at the University of Hong Kong, discusses academic freedoms in mainland China vs. Hong Kong, China and the U.S. as global superpowers, and censorship in China.
The Age of Surveillance Capitalism
Shoshana Zuboff, author of the acclaimed book The Age of Surveillance Capitalism, delves into the theory of surveillance capitalism, the harm of disinformation, and the future of democracy in the digital era.
“The Carr Center is building a bridge between ideas on human rights and the practice on the ground—and right now we're at a critical juncture around the world.”
Mathias risse, faculty director.

IMAGES
VIDEO
COMMENTS
Artificial intelligence (AI) is probably the defining technology of the last decade, and perhaps also the next. The aim of this study is to support meaningful reflection and productive debate about AI by providing accessible information about the full rang e of current and speculative techniques and their associated impacts, and setting out
These include the expansive National Artificial Intelligence Initiative Act of 2020 ... AEA Papers and Proceedings, vol. 108 (May 1, 2018), ... The term artificial intelligence was coined at the Dartmouth Summer Research Project on Artificial Intelligence, a conference proposed in 1955 and held the following year.6 Since that
at our disposal, AI is going to add a new level of ef ficiency and. sophistication to future technologies. One of the primary goals of AI field is to produce fully au-. tonomous intelligent ...
ABSTRACT. Artificial intelligence may greatly increase the efficiency of the existing economy. But it may have an even larger impact by serving as a new general-purpose "method of invention" that can reshape the nature of the innovation process and the organization of R&D.
The paper investigates the wide range of implications of artificial intelligence (AI), and delves deeper into both positive and negative impacts on governments, communities, companies, and individuals. ... McCarthy, John, Minsky ML, Rochester N, Shannon CE (2006) "A proposal for the Dartmouth summer research project on artificial intelligence ...
The aim of this research question is to identify the number of academic studies involving Artificial Intelligence and Machine Learning in the field of Information Systems, specifically those between the years 2005 and 2020 (see Fig. 4.).
Cognitive intelligence is a higher-level ability of induction, reasoning and acquisition of knowledge. It is inspired by cognitive science, brain science, and brain-like intelligence to endow machines with thinking logic and cognitive ability similar to human beings. Once a machine has the abilities of perception and cognition, it is often ...
The 2020 edition of UN Activities on Artificial Intelligence (AI) takes a deep dive into the technologies behind the more than 260 projects that are being developed by UN agencies to address some of the greatest global challenges in the history of the United Nations, including the COVID-19 pandemic.
Documented evidence of the potential of AI acting as (a) an enabler or (b) an inhibitor on each of the SDGs.The numbers inside the colored squares represent each of the SDGs (see the Supplementary ...
Artificial Intelligence Volume 7 Aims and Scope of the Series Artificial Intelligence (AI) is a rapidly developing multidisciplinary research area that aims to solve increasingly complex problems. In today's highly integrated world, AI promises to become a robust and powerful means for obtaining solutions to previously unsolvable problems.
The combination of expanding ICT-driven capabilities and capacities identifiable across our socio-economic systems along with growing consumer expectations vis-a-vis technology and its value-added for our societies, requires multidisciplinary research and research agenda on AI and ML (Lytras et al. 2021; Visvizi et al. 2020; Chui et al. 2020 ...
Human-Centered Artificial Intelligence is AI that seeks to augment the abilities of, address the societal needs of, and draw inspiration from human beings. It researches and builds effective partners and tools for people, such as a robot helper and companion for the elderly. Text by Professor Christopher Manning, September 2020
"Best Paper Award Second Prize" ICGECD 2020 -2nd International Conference on General Education and Contemporary Development, October 23-24, 2020 with our research paper Artificial intelligence ...
Mar 2024. Mohamed Louadi. This paper explores the complex relationship between demographics and artificial intelligence (AI) advances in Europe and Africa, projecting into the year 2050. The ...
This paper is structured as follows. Section 2 presents the application of AI technologies. Section 3 presents the threats and opportunities of AI. Section 4 presents the rise of AI, overall future outlooks, and new risks. The conclusion of the paper is presented in section 5. 2. Applications of Artificial Intelligence Technologies 2.1.
In December 2020, the National Artificial Intelligence Act of 2020, enacted as part of the William M. (Mac) Thornberry National Defense Authorization Act (NDAA) for Fiscal Year 2021 (P.L. 116-283), included the following definition: The term "artificial intelligence" means a machine-based system that can, for a given set
Artificial Intelligence (AI) is increasingly adopted by organizations to innovate, and this is ever more reflected in scholarly work. To illustrate, assess and map research at the intersection of AI and innovation, we performed a Systematic Literature Review (SLR) of published work indexed in the Clarivate Web of Science (WOS) and Elsevier Scopus databases (the final sample includes 1448 ...
View PDF HTML (experimental) Abstract: Robotic technologies have been an indispensable part for improving human productivity since they have been helping humans in completing diverse, complex, and intensive tasks in a fast yet accurate and efficient way. Therefore, robotic technologies have been deployed in a wide range of applications, ranging from personal to industrial use-cases.
The Journal of Artificial Intelligence Research (JAIR) is dedicated to the rapid dissemination of important research results to the global artificial intelligence (AI) community. The journal's scope encompasses all areas of AI, including agents and multi-agent systems, automated reasoning, constraint processing and search, knowledge ...
In recent times, there have been attempts to leverage artificial intelligence (AI) techniques in a broad range of cyber security applications. Therefore, this paper surveys the existing literature (comprising 54 papers mainly published between 2016 and 2020) on the applications of AI in user access authentication, network situation awareness, dangerous behavior monitoring, and abnormal traffic ...
The paper investigates the wide range of implications of artificial intelligence (AI), and delves deeper into both positive and negative impacts on governments, communities, companies, and ...
Literature review. Artificial Intelligence (AI) has dramatically altered the landscape of academic research, acting as a catalyst for both methodological innovation and broader shifts in scholarly paradigms (Pal, Citation 2023).Its transformative power is evident across multiple disciplines, enabling researchers to engage with complex datasets and questions at a scale previously unimaginable ...
AI Index Report. The AI Index Report tracks, collates, distills, and visualizes data related to artificial intelligence. Our mission is to provide unbiased, rigorously vetted, broadly sourced data in order for policymakers, researchers, executives, journalists, and the general public to develop a more thorough and nuanced understanding of the ...
The advancement in technology has made interdisciplinary research more accessible. Particularly the breakthrough in Artificial Intelligence AI has given huge advantages to researchers working in interdisciplinary and multidisciplinary fields. This study investigates the ability of AI models, particularly GPT4 and GPT Data Analyst in creating language maps for language documentation. The study ...
2.1 Prolific countries. Artificial intelligence in education (AIEd) research has been conducted in many countries around the world. The 40 articles reported AIEd research studies in 16 countries (See Table 1).USA was so far the most prolific, with nine articles meeting all criteria applied in this study, and noticeably seven of them were conducted in K-12.
1* [email protected]. Abstract — Artificial intelligence (AI) technology adoption. in the Philippines can be seen widely in many s ectors such as. industry, agriculture, and services ...
Open PDF in Browser. Share: Permalink. ... Centre for Digital Ethics (CEDE) Research Paper Series. Subscribe to this free journal for more curated articles on this topic FOLLOWERS. 653. PAPERS. 282. This Journal is curated by: ... Artificial Intelligence - Law, Policy, & Ethics eJournal.
The Carr Center for Human Rights Policy serves as the hub of the Harvard Kennedy School's research, teaching, and training in the human rights domain. The center embraces a dual mission: to educate students and the next generation of leaders from around the world in human rights policy and practice; and to convene and provide policy-relevant ...
AI for sustainability research strongly focuses on ML models and algorithms to show how machines can analyze and learn from data. ML learning techniques include reinforcement, transduction, multitasking, and supervised, unsupervised, and semi-supervised learning (Garcöa, Valdez, Döaz, Bustelo, & Lovelle, 2019).Supervised learning is divided into regression and classification for numerical ...
ARTIFICIAL INTELLIGENCE IN. EDUCATION. Jagadeesh Kengam. Science and Technology Department. Bournemouth University. Bournemouth, United Kingdom. [email protected]. Abstract -- This work ...