14 common network ports you should know

Opensource.com
The physical ports on your computer allow communicate with peripheral devices such as your keyboard and mouse and to connect with internet devices via Ethernet cables.
The Linux Terminal
- Top 7 terminal emulators for Linux
- 10 command-line tools for data analysis in Linux
- Download Now: SSH cheat sheet
- Advanced Linux commands cheat sheet
- Linux command line tutorials
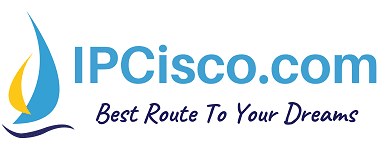
Witin computer networking, ports serve a similar purpose. When a computer system seeks to connect to another computer, the port serves as a communication endpoint. It is also possible for different services running on the same computer to expose various ports and communicate with one another using these ports. In simple terms, if a software application or service needs to communicate with others, it will expose a port. Ports are identified with positive 16-bit unsigned integers, ranging from 0 to 65535. Other services use this port number to communicate with the service or app. Port numbers are divided into three ranges: well-known ports, registered ports, and dynamic or private ports.
Well-known ports (also known as system ports ) are numbered from 0 through 1023. For example, to connect to the host example.com via SSH, I would use this command:
In this example, -v stands for verbose, and you should see output similar to this:
As shown, SSH is trying to connect to example.com using port number 22. You may use the -p option to specify another port number; otherwise, SSH will default to 22.
The Internet Assigned Numbers Authority (IANA) has assigned port numbers to commonly used services like SSH, FTP, HTTP, HTTPS, and others. Here are some of the most common ones:
In my work, I most commonly come across ports 80, 443, 20, 21, 22, 23, 25, and 53. Knowing these ports can help you work more efficiently.
What ports do you use the most, and why?

Learn more about Linux networking

How to configure networking in Linux
Connecting your Linux computer to a network is pretty straightforward, except when it is not. In this article I discuss the main network configuration files for Red Hat-based…

An introduction to Linux network routing
In June when I discussed basic network configuration, one thing I did not talk about then is routing. This article provides a very brief introduction to routing for Linux…
A Linux networking guide to CIDR notation and configuration
One of the key concepts in network routing that any Linux professional should be familiar with is network notation. This article was inspired by a request from a reader of my…

Related Content

Common Ports Cheat Sheet: The Ultimate List

Perhaps you’re angsty that you’ve forgotten what a certain port number meant. Rest assured, you don’t have to remember all 65,535 port numbers. With so much information to remember, it’s understandable if you forget a common port. That’s why we put together this cheat sheet of common network ports for you.
A crucial domain of expertise in IT-related certifications such as Cisco Certified Network Associate (CCNA) and those of CompTIA is port numbers and associated services , which this common ports and protocols cheat sheet covers. If you want to remember a port number or protocol, this cheat sheet will help everyone, from students to professionals.
Get a copy of this common ports cheat sheet here to keep on your desk. When you're ready, scroll below to find the port you’re looking for.
Common Ports Cheat Sheet Search
Search our Common Ports cheat sheet to find the right cheat for the term you're looking for. Simply enter the term in the search bar and you'll receive the matching cheats available.
Common Ports and Protocols Cheat Sheet
The following tables cover services (and malware) that use common TCP ports and some UDP or SCTP ports.
Well-known/System Ports: 0 – 1023

Registered Ports: 1024 – 49151

Dynamic/Private Ports: 49152 – 65535
You may use these ports for custom applications free from concerns that it may clash with existing processes.
The Most Common Ports for Exams
If you’re studying for IT certifications such as CCNA , focus on these ports:
We hope that you found this cheat sheet useful. Familiarity with ports and protocols is vital to building secure applications and troubleshooting problems on computer networks. Whether you're studying or working, this cheat sheet of common network ports will help you in academic and professional settings.
For further resources, or if you’re curious about how ports and protocols fit into cyber security, look into network security courses available with our StationX Accelerator Program .
Frequently Asked Questions
FTP: ports 20-21; SSH/SCP: port 22; HTTP: 80; HTTPS: 443; POP3: 110; POP3 over SSL: 995; IMAP: 143; IMAP over SSL: 993. We recommend you download the graphic in Well-known/System Ports .
It depends on whether you’re referring to system ports (1024) or want to include ports registered with apps (49152) because system ports range from 0 through 1023, and registered ports span 1024 – 49151.
FTP: ports 20-21; SSH/SCP: port 22; Telnet: 23; SMTP: 25; DNS: 53; HTTP: 80; POP3: 110; IMAP: 143; HTTPS: 443.
FTP: port 21; SSH/SCP: 22; Telnet: 23; SMTP: 25; DNS: 53; POP3: 110; IMAP: 145; HTTP: 80; HTTPS: 443; MySQL: 3306; RDP: 3389; VNC: 5900.
The following are the three types of ports with corresponding port number ranges: • Well-known/System ports: 0 – 1023 • Registered ports: 1024 – 49151 • Dynamic/Private ports: 49152 – 65535
Level Up in Cyber Security: Join Our Membership Today!

Nathan House is the founder and CEO of StationX. He has over 25 years of experience in cyber security, where he has advised some of the largest companies in the world. Nathan is the author of the popular "The Complete Cyber Security Course", which has been taken by over half a million students in 195 countries. He is the winner of the AI "Cyber Security Educator of the Year 2020" award and finalist for Influencer of the year 2022.
Related Articles

Nmap Cheat Sheet 2024: All the Commands & Flags
The one downside to a tool as robust and powerful […]
Read More »

Linux Command Line Cheat Sheet: All the Commands You Need
You may need to open a compressed file, but you've […]

Wireshark Cheat Sheet: All the Commands, Filters & Syntax
Wireshark is arguably the most popular and powerful tool you […]

The Only IPv4 Subnetting Cheat Sheet You’ll Ever Need
Our beginner networking students often describe IPv4 subnetting as the […]
Nathan, thank you for supplying this sheet. It comes in handy when you’re trying to remember what a particular port is used by.
Our pleasure.
Thank you, Nathan
This is a great single point to reference all default ports. Thank you!!!
Very good, it will be in front of me!
Ports on computers are required for networking, and without them, the computer would be completely isolated and it would be unable to communicate with other devices. So thank you for proving this list of the Common TCP and UDP Port numbers.
After resetting my router cause the password got changed and all the setting were changed to gain access to my computer. I spent about 20 minutes setting up the router. It appears the router never got set up from the cable company when it was installed. So if you have not done so lately check your router and settings.
Cool, Thanks for sharing!!
Sorry Nathan, i did not leave a comment for this “Common Ports” Chart last-week. I am glad i signed up to your news letter you are a good researcher. thank you for sharing with us all..
Nathan, I must thank you for these cheat sheets! They’ve been great on my learning and certification journey!
Thank you too!
Really really useful.Thanks a lot!!
Session expired
Please log in again. The login page will open in a new tab. After logging in you can close it and return to this page.

DEV Community
Posted on Oct 7, 2023
The Ultimate Common Ports Cheat Sheet in Computer Networking
If you’re a student studying networking or a budding IT courteous,, understanding common ports is essential. Ports serve as data gateways for data to enter and exit a computer, and understanding which services and applications use which ports is critical for network troubleshooting and security. We’ll provide you a complete list of the most often used ports and their associated services in this common ports cheat sheet, making it easier for you to traverse the world of networking.
What Are Ports in Networking and Types
What Are Ports?
Before we go into the list of common ports, let’s define ports and why they’re important in the networking world.
A port number is a 16-bit number with a 0 to 65535 decimal value range. There are three various types of port number spaces: well-known ports (0–1023), registered ports (1024–49151), and dynamic ports (49152-65535).
- Well-known or Reserved Ports: 0–1023
- Registered Ports: 1024–49,591
- Dynamic Ports: 49,592–65,535
These ports can be opened and utilised by operating system services and software programmes to send and receive data via LAN or WAN networks using certain protocols (such TCP, UDP, etc.).
For example, when you visit a website as a web blogger, your computer normally connects to the typical web on port 80 (HTTP) or a secure, virtual web connection to the web server on the port 443 (HTTPS). Goes for it. With whom he communicates. Identifying which port belongs to which service facilitates firewall conversion to network diversion, but results in insufficient defence against the problem.
What are well-known ports
Well-known ports have port numbers ranging from 0 to 1023. The Internet Corporation for Assigned Names and Numbers (ICANN) assigned these port numbers. These ports, often known as privileged ports, are reserved for common TCP/IP applications.
Each port has been given a specific application. Unencrypted online browsing is done via the Hypertext Transfer Protocol (HTTP) on port 80. POP3 (Post Office Protocol version 3) over port 110 is used to receive emails through a server.
What are registered ports
Registered ports have port numbers ranging from 1024 to 49,591. Although these port numbers are neither assigned or managed, they can be registered to minimise repetition. The Internet Assigned Numbers Authority (IANA) is the institution that can issue these ports; before, they were assigned by ICANN.
What are dynamic ports
Dynamic ports, also known as ephemeral ports, are ports that are only active for a short amount of time. They are temporary because they are “opened and closed” as a user is using an application.
Assume I wish to connect to the internet. The first step is, of course, opening a web browser. When you start a web browser and connect to the internet, you will be connected to port 80 (HTTP) or port 443 (HTTPS), depending on the encryption of that web page.
It will select a random open port, such as 49,695, to send that web page to you. When you finish looking at the web page and exit the browser you’re using, the port 49,695 on your end will be closed.
Common Ports Cheat Sheet
Now, let’s explore the most common ports with which you should acquaint yourself. We’ll categorize them for easier reference.
Well-Known Ports (0-1023)
These ports commonly associate with widely-used services and applications.
- Firstly, Port 21 – FTP (File Transfer Protocol) is used for transferring files over a network.
- Secondly, Port 22 – SSH (Secure Shell) provides secure remote access to systems and secure file transfers.
- Next, Port 23 – Telnet is a less secure remote access protocol used for managing network devices.
- Moving on, Port 25 – SMTP (Simple Mail Transfer Protocol) handles outgoing email communication.
- Additionally, Port 53 – DNS (Domain Name System) resolves domain names to IP addresses.
- Subsequently, Port 80 – HTTP (Hypertext Transfer Protocol) is used for unencrypted web traffic.
- Moreover, Port 443 – HTTPS (Hypertext Transfer Protocol Secure) provides secure, encrypted web communication.
- Furthermore, Port 110 – POP3 (Post Office Protocol version 3) retrieves email from a mail server.
- Similarly, Port 143 – IMAP (Internet Message Access Protocol) allows access to email on a remote mail server.
- Lastly, Port 3389 – RDP (Remote Desktop Protocol) enables remote desktop connections.
Registered Ports (1024-49151)
These ports are frequently linked with applications and services that are less well-known than those in the well-known range but are nevertheless required for certain purposes.
- Port 3306 – MySQL Serves as a popular database management system.
- Port 5432 – PostgreSQL Represents another widely-used open-source database management system.
- Port 8080 – HTTP Alternate (HTTP Proxy) Frequently used as a secondary HTTP port.
- Port 27017 – MongoDB Addresses high-volume data storage needs through a NoSQL database.
- Port 5060 – SIP (Session Initiation Protocol) Facilitates voice and video calls across IP networks.
- Port 6660-6669 – Internet Relay Chat (IRC) Enables real-time text communication.
- To begin with, Port 3306 – MySQL is a popular database management system.
- Next up, Port 5432 – PostgreSQL is another widely-used open-source database management system.
- If you need an alternate HTTP port, Port 8080 – HTTP Alternate (HTTP Proxy) is often used as a secondary HTTP port.
- For NoSQL database enthusiasts, Port 27017 – MongoDB is a go-to choice for high-volume data storage.
- In the realm of communication, Port 5060 – SIP (Session Initiation Protocol) facilitates voice and video calls over IP networks.
- If you’re a fan of real-time text communication, Port 6660-6669 – Internet Relay Chat (IRC) is the way to go.
- And for secure web communication through an alternate port, don’t forget Port 8443 – HTTPS Alternate (HTTPS Alt).
Dynamic and Private Ports (49152-65535)
These ports are often used for dynamic, private, or temporary purposes. They are not assigned to specific services but are available for use as needed.
- Additionally, Port 49152-65535 – Ephemeral Ports (also known as dynamic ports) are used by client applications for temporary purposes, such as establishing connections.
Additional Ports to Know
While the above ports cover the most common ones, it’s worth mentioning a few more ports that may be important in specific contexts.
Port 161/162 – SNMP (Simple Network Management Protocol) is used in network management to manage and monitor network devices. For simpler file transfers, Port 69 – TFTP (Trivial File Transfer Protocol) is a viable option.
Understanding common ports and their associated services is vital for anyone involved in networking or IT systems. This cheat sheet is a helpful resource for navigating the world of networking. Remember that, while these are the most frequent ports, there are many more, and new ones may emerge as technology improves. Maintain your interest and keep learning in order to keep your networking knowledge up to date. Whether you’re a student or an IT professional, this information will help you master the complexities of networking.
Top comments (0)
Templates let you quickly answer FAQs or store snippets for re-use.
Are you sure you want to hide this comment? It will become hidden in your post, but will still be visible via the comment's permalink .
Hide child comments as well
For further actions, you may consider blocking this person and/or reporting abuse

Explore useEffect Alternatives: Beyond the Well-Trodden Paths
Herrington Darkholme - Mar 27

7 reasons people quit learning to code (& how to avoid them)
Hunter Johnson - Apr 26

Data Structures: A Comprehensive Introduction
mahdi - Apr 28

Please check my portfolio
Yakov Levin - Apr 27

We're a place where coders share, stay up-to-date and grow their careers.
- Editor's Choice: Tech Gifts for Mom
- New! iPad Air 6 Details
Computer Ports: Usage & Role in Networking
Discover the wide range of computer connections
- Massachusetts Institute of Technology
- University of Illinois
In This Article
Jump to a Section
Physical Ports
Ports in wireless networking, internet protocol ports, issues with ports in computer networking.
Computer ports are an essential feature of all computing devices. Ports provide the input and output interfaces the device needs to communicate with peripherals and computer networks .
The most important ports on computers are used for networking, for without them, the computer would be completely isolated and unable to communicate outside of itself.
A port can be either physical or virtual. Physical network ports allow you to connect cables to computers, routers , modems , and other peripheral devices. Ports are physically connected in one way or another to the motherboard .
Several types of physical ports available on computer network hardware include:
- Ethernet ports : Square-shaped connection points for Ethernet cables .
- USB ports : Rectangular-shaped connection points for USB cables.
- Serial ports : Round-shaped connection points for serial cables.
Networking aside, other ports that exist on a computer include ones for video (like HDMI or VGA ), mice and keyboards ( PS/2 ), FireWire , and eSATA , among others.
While wired computer networks rely on physical ports and cables, wireless networks don't need them. Wi-Fi networks, for example, use channel numbers representing radio signaling bands.
However, wired and wireless networking can blend via physical computer ports. For example, a network adapter plugged into a computer's USB port turns the wired computer into a wireless computer, thus bridging the gap between the two technologies using a port.
Virtual ports are an essential component of Internet Protocol (IP) networking. These ports allow software applications to share hardware resources without interfering with each other.
Computers and routers automatically manage network traffic traveling via their virtual ports. Network firewalls also provide some control over the flow of traffic on each virtual port for security purposes.
In IP networking, these virtual ports are structured via port numbers , from 0 through 65535. For example, port 80 lets you access websites through your web browser , and port 21 is associated with FTP.
Physical ports can stop functioning for several reasons. Causes of port failure include:
- Power surges (for devices physically connected to electric mains).
- Water damage.
- Internal failure.
- Damage caused by the cable pins (for example, inserting cables too forcefully or by attempting to plug the wrong type of cable into a port).
Except for damage to pins, a physical inspection of the port hardware won't find anything obviously wrong. A failure of one port on a multiport device (such as a network router) doesn't affect the functioning of the other ports.
The speed and specification level of a physical port can also not be determined by physical inspection. Some Ethernet devices, for example, operate at a maximum of 100 Mbps , while others support Gigabit Ethernet , but the physical connector is the same in both cases. Similarly, some USB connectors support version 3.0 while others only support USB 2.x or sometimes USB 1.x .
The most common challenge with virtual ports is network security. Internet attackers regularly probe the ports of websites, routers, and any other network gateways . A network firewall helps guard against these attacks by limiting access to ports based on their number.
To be most effective, a firewall tends to be overprotective and will sometimes block traffic that a person wanted to allow. Methods for configuring the rules that firewalls use to process traffic—such as port forwarding rules —can be complicated for non-professionals to manage.
Get the Latest Tech News Delivered Every Day
- Can Two Routers Be Used on the Same Home Network?
- The Best Long-Range Routers of 2024
- Port Numbers Used for Computer Networks
- What Does a Motherboard Do?
- What to Do When Windows 11 Can't Connect to a Network
- What Is a USB Port?
- What is a Wireless Network?
- Learn the Definition of a Network Firewall
- The Differences Between Routers, Switches, and Hubs
- What Is a Network?
- What Is the Effect of Using a Router?
- A Short Guide on Networking Fundamentals
- What Is Port 443?
- Types of Network Connections
- What Is Computer Networking?
- Functions and Features of Routers for Home Computer Networks
TCP/IP Ports and Sockets Explained
The IP address identifies the device e.g. computer.
However an IP address alone is not sufficient for running network applications, as a computer can run multiple applications and/or services .
Just as the IP address identifies the computer, The network port identifies the application or service running on the computer.
The use of ports allow computers/devices to run multiple services/applications .
The diagram below shows a computer to computer connection and identifies the IP addresses and ports.
If you use a house or apartment block analogy the IP address corresponds to the street address.
All of the apartments share the same street address.
However each apartment also has an apartment number which corresponds to the Port number.
Port Number Ranges and Well Known Ports
A port number uses 16 bits and so can therefore have a value from 0 to 65535 decimal
Port numbers are divided into ranges as follows:
Port numbers 0-1023 – Well known ports. These are allocated to server services by the Internet Assigned Numbers Authority (IANA). e.g Web servers normally use port 80 and SMTP servers use port 25 (see diagram above).
Ports 1024-49151- Registered Port -These can be registered for services with the IANA and should be treated as semi-reserved. User written programs should not use these ports.
Ports 49152-65535 – These are used by client programs and you are free to use these in client programs. When a Web browser connects to a web server the browser will allocate itself a port in this range. Also known as ephemeral ports .
TCP Sockets
A connection between two computers uses a socket.
A socket is the combination of IP address plus port
Imagine sitting on your PC at home, and you have two browser windows open.
One looking at the Google website, and the other at the Yahoo website.
The connection to Google would be:
Your PC – IP1 +port 60200 ——– Google IP2 +port 80 (standard port)
The combination IP1+60200 = the socket on the client computer and IP2 + port 80 = destination socket on the Google server.
The connection to Yahoo would be:
your PC – IP1 +port 60401 ——–Yahoo IP3 +port 80 (standard port)
The combination IP1+60401 = the socket on the client computer and IP3 + port 80 = destination socket on the Yahoo server.
Notes : IP1 is the IP address of your PC. Client port numbers are dynamically assigned, and can be reused once the session is closed.
TCP and UDP -The Transport Layer
Note : You may find reading the article on the TCP/IP protocol suite useful to understand the following
IP addresses are implemented at the networking layer which is the IP layer.
Ports are implemented at the transport layer as part of the TCP or UDP header as shown in the schematic below:
The TCP/IP protocol supports two types of port- TCP Port and UDP Port .
TCP – is for connection orientated applications. It has built in error checking and will re transmit missing packets.
UDP – is for connection less applications. It has no has built in error checking and will not re transmit missing packets.
Applications are designed to use either the UDP or TCP transport layer protocol depending on the type of connection they require.
For example a web server normally uses TCP port 80 .
It can use any port, but the web server application is designed to use a TCP connection. See TCP vs UDP
Here is a very good video that explains ports and sockets really well
Checking For Open Ports
Windows and Linux systems have a utility called netstat which will give you a list of open ports on your computer.
These articles show you how to use netstat on windows and on linux .
You can check the port status of remote machines using a port scanner line nmap .
You can install NMAP on windows,Linux and Apple. It can be used with a graphical user interface of as a command line tool.
Here is a useful article on using NMAP from the command line .
Here is a good video on using Nmap and also covers TCP/IP connection procedures which is useful for understanding ports.
References and resources:
TCP and UDP basics -Connecting to a website- This is for programmers but there is no coding just an explanation of ports and sockets.
Connection states – if you are wondering what established and listening and the other state descriptions mean. here is a good state diagram that it refers to.
Online port tester Collection of tools for port scanning and web server testing.
Related Articles:
- TCP/IP protocol suite explained
- Port Forwarding Explained
- IPv4 Basics
70 comments
I created an inbound UDP port (10512); but I am not able to see this port. I also tried creating other ports in the noted range with out any success. Registered Ports: 1024 through 49151 portqry —-> UDP port 10512 (unknown service): NOT LISTENING Thanks for any clarification
Have you tried writing a program to send/receive data on that port.What utility are you using to view the ports. Rgds
Sorry, no time to research and develop a program. it would nice. I am trying to use online tools. I think that I just learned that portqry works great for TCP. I am trying to use iperf3; however not enough hands on as of yet. I see that iperf3 created inbound rule TCP and UDP. I deleted the TCP. I need more flying hours. iperf3 -s -p 10512 ———————————————————– Server listening on 10512 ———————————————————– I am also trying to use netstat to see if the port is listening; however no progress on that end. netstat -ab
netsh firewall show state netsh will show UDP port on client computer with Win 11 PRO but not on the server 2019.
thanks for any input
client side >iperf3 -c 10.241.71.38 -u -p 10512 -b 10M
I’ve decided to try to mess around with port forwarding as a means to try to get me and my friend who live in the same town and use the same internet provider (Spectrum) to be able to connect to each other in games that do not have dedicated servers. Spectrum’s peer-to-peer is absolute trash, and we can never connect to each other playing games like Risk of Rain 2, Elden Ring, etc. I’m trying to find a port that would help us overcome the connection issues. Any advice?
I’m not a gamer and so I have never experienced these issues. However games have their own ports have you checked on the required ports for these games? Rgds Steve
Hi Steve, I have a requirement. We have a web application which is connected to a mobile/Android POS device. This web application connects via TCPIP. As of today, we have the connections that are initiated from the device. the URL and port # of the web server is configured in the device and the connection is initiated from the device. Web application will respond to a request from the device. We now want to initiate the request from the server. Can we add another port # for this new communication? Similarly, there is a 3rd communication that happens from the device on timed intervals. For this, we want to use a 3rd port. Is this a possible solution for this? Happy to discuss this separately too.
I assume that you are talking about a web server. A web server cannot start a connection. Rgds Steve
Respected Sir Thank you so much for this informative article. I am a first year IT student. Sir , if I visit any particular website for 15 minutes and visit various sections of this website (feedback/ contact us / about us etc) in such case, does my visit to various sections is considered as a single connection/ single session or they are considered as multiple connections / multiple sessions to this website? Also what is the role of session ID in TCP IP communication along with port and socket Thank you Sir Bhavesh
It is a single TCP/IP connection. If you close the tab and then revisit by typing in the url then you will get a new connection.
Just out of curiosity, if the user visits different pages on the website, won’t these be over a new TCP connection every time unless a long-lived HTTP is used?
No they will be a single connection just a different get command. HTTP now hold the connection open by default until you close the browser tab. Rgds Steve
Thanks Steve for making it vividly simple.
I have a problem with an application that uses fixed source ports in the communication with the server. If the communication ends for some reason the clients tries to put the communication up again using the same source port. The problem is that the server have not gotten a fin packet that takes down the communication and it still listens for the communication from the client in a ESTABLISHED status if you run netstat -a on the server. If the client had not used fixed ports I would think that the communication would reconnect with a new session because the client had used “+1” on its source port and the server would connect the communication with a new socket.
Is there a “best practice” rfc that explains why it is not a good idea to use fixed ports?
Not that I am aware.
Wonderful, I’ve sent it over email along with some info It runs on Ubuntu Thank you for your time on this and God bless Al
I have a software which creates 4 sockets with apparently random numbers (the person who developed left no documentation)
However, the client which connects to it only sends over port 9091
Is there a way to interconnect those random number sockets and port 9091 so the client is able to connect to the software?
Thanks in advance and God bless
Hi It sounds like the software is supposed to be a server which usually has fixed ports. What does the software do?
It receives video data, connects to a MariaDB server, and serves as an API to it, receiving calls from a mobile app and sending customer data back
I wonder if the reason why it opens 4 sockets is to receive and send video data and receive and send customer data
Either way, the problem is that it creates sockets of random numbers instead of a 9091 port which is what the android app uses
Below its log, hope that sheds some light and thanks
[0121/06/01 12:55:01][0000-00000001] SDSS int server v1.2.0 – b6 (01/03/2021) run up at Thu Jul 1 12:55:01 2021 [0121/06/01 12:55:01][0000-00000002] debug level set to 99 [0121/06/01 12:55:01][0000-00000003] args[ ./dvis -d99 ] [0121/06/01 12:55:01][0000-00000004] startup info follows: [0121/06/01 12:55:01][0000-00000005] stdin handle 0 [0121/06/01 12:55:01][0000-00000006] openSQL( 0x5f687580 ) [0121/06/01 12:55:01][0000-00000007] openSQL: Connection successful to ‘127.0.0.1’ as ‘sa’ [0121/06/01 12:55:01][0000-00000008] hostname being used is ‘stipra.com’ [0121/06/01 12:55:01][0000-00000009] get_ipaddress() [0121/06/01 12:55:01][0000-00000010] lo IP Address 127.0.0.1 [0121/06/01 12:55:01][0000-00000011] wlo1 IP Address 192.168.1.142 [0121/06/01 12:55:01][0000-00000012] lo IP Address ::1 [0121/06/01 12:55:01][0000-00000013] wlo1 IP Address fe80::d6a7:186d:aa86:5311 [0121/06/01 12:55:01][0000-00000014] get_ipaddress: returning an IP4 address of 192.168.1.142 [0121/06/01 12:55:01][0000-00000015] Running on server stipra.com IP address 192.168.1.142 [0121/06/01 12:55:01][0000-00000016] setsockopt returned 0, errno 11 [0121/06/01 12:55:01][0000-00000017] sockets created [0121/06/01 12:55:01][0000-00000018] 63420 [0121/06/01 12:55:01][0000-00000019] 29616 [0121/06/01 12:55:01][0000-00000020] 6052 [0121/06/01 12:55:01][0000-00000021] 43464 [0121/06/01 12:55:01][0000-00000022] wait_for_cmd(0x1) [0121/06/01 12:55:01][0000-00000023] stdin(0) [0121/06/01 12:55:01][0000-00000024] recv_d( 0, 0x7f90fdd4e010, 8 ) [0121/06/01 12:56:01][0000-00000025] recv_d: Select timeout, retrying [0121/06/01 12:57:01][0000-00000026] recv_d: Select timeout, retrying [0121/06/01 12:58:01][0000-00000027] recv_d: Select timeout, retrying [0121/06/01 12:59:01][0000-00000028] recv_d: Select timeout, retrying [0121/06/01 13:00:01][0000-00000029] recv_d: Select timeout, retrying [0121/06/01 13:01:01][0000-00000030] recv_d: Select timeout, retrying [0121/06/01 13:02:01][0000-00000031] recv_d: Select timeout, retrying [0121/06/01 13:03:01][0000-00000032] recv_d: Select timeout, retrying [0121/06/01 13:04:01][0000-00000033] recv_d: Select timeout, retrying [0121/06/01 13:05:01][0000-00000034] recv_d: Select timeout, retrying [0121/06/01 13:06:01][0000-00000035] recv_d: Select timeout, retrying [0121/06/01 13:07:01][0000-00000036] recv_d: Select timeout, retrying [0121/06/01 13:08:01][0000-00000037] recv_d: Select timeout, retrying [0121/06/01 13:09:01][0000-00000038] recv_d: Select timeout, retrying [0121/06/01 13:10:01][0000-00000039] recv_d: Select timeout, retrying [0121/06/01 13:10:01][0000-00000040] wait_for_cmd: Initial receive is not 8 bytes [0121/06/01 13:10:01][0000-00000041] pipe broken exiting
Sorry don’t know, It looks like it is creating client connections but not sure what to. When you say it receives video data I assume that that is coming in on a port. The database would need another. The mobile app is used to view the video I assume. Is any part of it working. Where is the mobile App located(internet or same network). Is this a standard kit or is it put together by yourself? Rgds Steve
The software creates 4 sockets with random port numbers but none of them are the port 9091 which the APP uses. The mobile App is on the internet.
The software connects to a tunnel connection 10.8.0.0, which leads me to believe it requires the creation of some kind of tunnel to capture anything received from the internet on port 9091 from 192.168.1.142 and forward it to those 4 sockets through some kind of dynamic port forwarding thing or something like that
I tried to use ssh -D 192.168.1.142:9091 -N -f [email protected] and I am able to telnet 192.168.1.142 and connect the app, but no data seems to go or come back 🙁
The software connects to the database, and that’s actually the only thing it is doing well
Does it have any setup instructions. Is it off the shelf software and does it have a website that I can take a look at. Rgds Steve
It is a bespoke software made by a person who left the company and never left any documentation. It is developed in C++ 32 bits I can send it to your email which I believe is [email protected] as it is rather small, along with how to run itm (the little I know at least)
That email will work is it for windows or linux?
Hi, I have a question, is it possible for me to run 2 applications and connect to different ip but using same port number (example 6000) ?
Yes you are doing that when you connect to two different websites as they both use port 80 rgds steve
So I have a question. Let’s say there is a webserver A which hosts a website and that server A has the port 443 open and let’s say I have written a code as part of a webpage on that website and that code connects to a remote server B to get some data. Can server A somehow restrict me and only allow connections to the port 443 on the remote server B and not allow me to connect me to any other port on remote server B? Have you seen such a restriction before and if yes then what would be the reason behind such a restriction? Thank you
Not quite sure exactly what restriction you mean but you can restrict on destination port and ip and source port and IP if that helps rgds steve
Hi Steve, So here is the scenario. The webserver A has the port 443 open for any incoming requests. The webserver A hosts a website and one of the pages of that website has C# code which makes API calls to a remote server B. I was told by the network admin of Webserver A that the C# API call should be made only to the port 443 of the remote server B. Currently the remote server B has port 7093 open and it’s listening to any API requests on that port. So my questions are:- 1. Is it possible for the network admin to disallow API calls to ports other than 443? 2. What could be the reason for such a restriction? After all, how can restricting a destination port give you any sort of advantage? Port is just a number on which the server listens. Please help. Thank you
Yes you can filter incoming traffic on port, ip address and protocol even on basic firewalls. Restricting ports is for security reasons Rgds Steve
Minor formatting issue: “{outline]Each end of the connection will have a socket.{/outline]”
Tks for pointing that out. Rgds Steve
Very well explained, thanks a lot!
Steve, this was very well explained, thank you.
Thank you very much! Realy clear explanation.
I want to read a data from a machine which supports open protocol if the machine is in network and if I know IP address and port number(socket) how can I read a data from it(I know it send and receive data in packet format )
Hi not sure what you mean by supports open protocol. Rgds Steve
Thank you, Steve! Is it possible with TCP/IP sockets to send requests to one IP:PORT and listen for responses on a different IP:PORT. E.g. we want to send to a load balancer IP but listen for response on localhost.
Hi Not quite sure of what you mean exactly but load balancing is quite common. This might help https://www.citrix.com/glossary/load-balancing.html
Question: When a program on your computer sends or receives data over the Internet it sends that data to an ip address and a specific port on the remote computer. How does my computer know what port a specific application is working on another computer to populate the TCP Header?
When Machine A connects to machine B. The source ip and port are contained in the connection packet as well as the destination port and IP address. The IP packet contains the ip addresses and the tcp layer contains the port numbers see https://en.wikipedia.org/wiki/IPv4 https://en.wikipedia.org/wiki/Transmission_Control_Protocol
Hi Steve, Thanks for the tutorial can you please help me with the following issue I have multiple devices connected to the same network and I want to transfer data across them, how can I transmit the data the IP of some devices changes after a particular time I can keep the port number constant but the devices don’t know each others IP address and also I don’t want to use UDP because it is not reliable
Hi You need to use DNS.Because the IP changes you need dynamic DNS. Most devices have MDNS enabled. See this article on my other site https://stevessmarthomeguide.com/name-resolution-and-dns-on-home-networks/ To seen if mdns is working try ping computer_name.local However the easiest solution is to give them static IP addresses. Rgds Steve
Great site. I have a quick question. If I receive a UDP datagram using recvmsg(), will the msghdr structure be filled out with the sender’s IP and port (in the msg_name field, which is a sockaddr struct)?
Many thanks.
Hi Haven’t programmed c with UDP but according to IBM then yes for ip address but doesn’t mention the port. https://www.ibm.com/support/knowledgecenter/en/SSLTBW_2.1.0/com.ibm.zos.v2r1.hala001/rcvm.htm rgds steve
hi ,I have some questions When using TCP protocol, the client must use in its message the IP address and Port number of the server. And it must also include its own IP address and port number. why?
4- When using UDP protocol, the client is required to use in its message the IP address and Port number of the server. But it is not required to include its own IP address and port number.why?
TCP is a connection orientated protocol and so the destination device needs to know who to send a reply to. UDP is connectionless and so doesn’t require a response and hence the source IP address is optional. Rgds Steve
really very useful..thanks for your explanation
Can Server and client share the port number, eg : Server is listening at port num : 51001 and client also listens on the same port num : 510001 .
Can you pls explain this
Yes providing they are on different hardware. A port is simply a door into the machine the numbers themselves aren’t really important except for the conventions already adopted and standardised. Machines use 16bits for the port numbers hence the limitation of 64,000.
16 bits = 1+2+4+8+16+32+64+128+256+512+1024+2048+4096+8192+16384+32768 = 65535
Good job Steve. I have a question, and it goes like this: if i have 2 browsers from my PC connecting to the same service, for example both browsers are connecting to google.com, does that mean that the two browsers from my computer are connecting to the same socket in the google server? Meaning can more than one socket connect to a socket at the same time?
Yes they use the same IP and port on the Google server but different ports on the client. rgds steve
Hi, Thanks for this information sharing. It is very well explained. I have following doubt, What I understand is TCP protocol takes care of data transmission error that duplication of packets or packet in true form delivered to other end. This is not done in UDP protocol. But when I see the Schematic of TCP, UDP & IP in your article I do not find any block for error checking in TCP where as UDP has checksum. Could you please clear my doubt.
The TCP packet also has a checksum which isn’t shown in my schematic you can see the full structure on wiki https://en.wikipedia.org/wiki/Transmission_Control_Protocol However it is the ack and nack messages that are responsible or making sure all of the data is received. Rgds Steve
In above example, google application/service and yahoo application/service both uses same port number i.e:80. Then there should be ambiguity that is to which application/service it should refer to either google or yahoo ;How it knows that it is google or yahoo as both has same port number? Answer will help me alot.
Google and Yaoo have different IP addresses. When you connect to google you use Google_IP +port 80. When you connect to Yahoo you connect to Yahoo_IP + port 80. Does that make sense? rgds steve
The IP is the who and the Port is part of the how.
The IP address of google and yahoo is different. say for google 172.13.73.130 and for yahoo 172.23.73.128 so even accessing the same port the two sockets will be totally different and hence different connections.
using the real world analogy two rooms of two different apartments may have the same room number and hence two server system may have same port number as well.
The port number 80 is the open port of server.here Google server had an open port (80) also Yahoo had an open port (80).
Both Google and Yahoo had different IP addresses.
If I want to connect Google server,I will open a new port,for example I will open port 5000, at the same time I will open another port 5002 to connect with Yahoo server.
My IP + 5000 — connects — Google IP + 80
My IP + 5002 — connects — Yahoo IP + 80
Great work!
Good Job!! Well Explained
Hi! keep up the good work. I have few doubts though, hope you can clear them: 1. Can you tell if a server uses a single port 80 on all of its connections to clients? Or is it used only by the Welcoming socket? Can port 80 handle multiple connections simultaneously?
A port (e.g port 80) can handle multiple connections each connection is a socket and will have a different source IP address and port number.
No… a session needs to be established at said layer. A is lessening on port 443 (SSL) for incoming packets and firewall infront is in addition to alllowing 443 to A also policing 25, 80 etc Whatever….
Excellent explanation. Thankyou!
very good information
The way you explain ed it, now it’s very easy understand the whole thing thanks alot sir .
Complete details about the TCP / IP ports and the sockets. in this article .The infographic is so good that anybody can understand at a glance. I request the author to post more articles on networking.
Leave a Reply Cancel reply
Your email address will not be published. Required fields are marked *

- Selected Reading
- UPSC IAS Exams Notes
- Developer's Best Practices
- Questions and Answers
- Effective Resume Writing
- HR Interview Questions
- Computer Glossary
50 Common Ports You Should Know
Introduction.
In the world of computer networking, ports play a crucial role in facilitating communication between different devices. A port can be defined as a logical channel through which information streams between two devices. Each port has a unique number assigned to it, known as a port number. Understanding port numbers and their comparing administrations is fundamental for anybody who works with computer systems.
In this article, we'll examine 50 of the most common ports that you should know. These ports are assembled into different types based on their characteristics and utilization. We'll investigate their highlights, significance, and centrality in computer organizing.
Discuss About 50 Common Ports You Should Know?
These ports are used to facilitate communication between devices on the network and are essential for network administrators and IT professionals to understand.
Every port in computer networking is associated with a specific protocol or service, and each protocol or service is assigned a standard port number by the Internet Assigned Numbers Authority (IANA). These would be organized into three ranges - well-known ports (0 to 1023), registered ports (1024 to 49151), and dynamic/private ports (49152 to 65535).
The article gives a comprehensive list of the 50 most commonly utilized ports, their related conventions, and the sorts of administrations that ordinarily utilize them. It too incorporates a brief clarification of how to utilize harbor filtering instruments to identify open ports and vulnerabilities.
Well-Known Ports
Well-known ports are those ports whose numbers range from 0 to 1023. They are assigned to specific services and protocols, and their numbers are standardized by the Internet Assigned Numbers Authority (IANA). Some common well-known ports include −
Port 80: HTTP (HyperText Transfer Protocol)
Port 21: FTP (File Transfer Protocol)
Port 25: SMTP (Simple Mail Transfer Protocol)
Port 22: SSH (Secure Shell)
Port 443: HTTPS (HyperText Transfer Protocol Secure)
Port 53: DNS (Domain Name System)
Registered Ports
Registered ports are those ports whose numbers range from 1024 to 49151. They are assigned to user processes or applications by the IANA upon request. Some commonly registered ports include −
Port 3306: MySQL Database
Port 5432: PostgreSQL Database
Port 3389: Remote Desktop Protocol (RDP)
Port 27017: MongoDB Database
Port 1521: Oracle Database
Dynamic or Private Ports
These ports whose numbers range from 49152 to 65535. They are used by client applications to initiate communication with servers. Some common dynamic or private ports include −
Port 49152: Windows RPC (Remote Procedure Call)
Port 5353: mDNS (Multicast Domain Name System)
Port 5672: AMQP (Advanced Message Queuing Protocol)
Port 5355: LLMNR (Link-Local Multicast Name Resolution)
Port 49153: Windows RPC (Remote Procedure Call)
Impact of ports on Computer Networks
Port numbers play a vital role in the security of computer networks.
Misconfigured ports can lead to security breaches and data leaks.
Understanding port numbers and their corresponding services can help in the identification and prevention of cyber-attacks.
Significance of ports
Ports are the backbone of computer organizing and empowering communication between different devices and applications.
Ports encourage the exchange of information between different protocols and administrations.
The standardization of well-known ports by the IANA guarantees that different devices can communicate with each other consistently.
Some other common ports are
Telnet (23) - Telnet protocol to ensure effective communication along with the remote server.
POP3 (110) - Post Office Protocol version 3 for email retrieval.
IMAP (143) - Internet Message Access Protocol for email retrieval.
DHCP (67/68) - Dynamic Host Configuration Protocol for IP address allocation.
NTP (123) - Network Time Protocol for time synchronization.
SNMP (161/162) - Simple Network Management Protocol to verify the functionality of the network and management of network.
SMB (445) - Server Message Block protocol for file sharing and printer sharing.
AFP (548) - Apple Filing Protocol for file sharing between Macs.
NetBIOS (137-139) - NetBIOS protocol for network communication between Windows devices.
HTTP Proxy (8080) - HTTP proxy server.
SOCKS (1080) - SOCKS proxy server.
MySQL (3306) - MySQL database server.
MSSQL (1433) - Microsoft SQL Server database server.
Oracle (1521) - Oracle database server.
LDAP (389/636) - Lightweight Directory Access Protocol for directory services.
SMB2 (5722) - SMB version 2 protocol.
IKE (500) - Internet Key Exchange protocol for VPN connections.
L2TP (1701) - Layer 2 Tunneling Protocol for VPN connections.
PPTP (1723) - Point-to-Point Tunneling Protocol for VPN connections.
SIP (5060/5061) - Session Initiation Protocol for VoIP communication.
RTP (16384-32767) - Real-time Transport Protocol for audio and video transmission.
RTCP (16384-32767) - Real-time Control Protocol for audio and video transmission.
HTTPS Proxy (3128) - HTTPS proxy server.
Squid (3128) - Squid proxy server.
VNC (5900) - Virtual Network Computing for remote access.
IRC (6667/6697) - Internet Relay Chat for real-time communication.
Bonjour (5353) - Bonjour protocol for network discovery and communication.
NFS (2049) - Network File System for file sharing.
Redis (6379) - Redis key-value store.
Memcached (11211) - Memcached distributed memory caching system.
Rsync (873) - Remote synchronization for file transfers.
Zeroconf (5353) - Zero Configuration Networking for automatic network configuration.
XMPP (5222/5223) - Extensible Messaging and Presence Protocol for instant messaging.
VMware vSphere Client (443) - VMware vSphere Client for virtualization.
In conclusion, understanding the common ports used in computer networking is essential for IT professionals and network administrators. Being aware of these ports can help them troubleshoot network issues and ensure smooth communication between devices on the network.

Related Articles
- Productivity Tools You Should Know
- Finance Management: What You Should Know
- Everything You Should Know About Cloud Mining
- What you should know about VPN passwords?
- Client-Server Architecture - Everything You Should Know
- Things You Should Know Before You Start Working in Germany
- Know Cloud Ports and Protocols Infra Perspective!
- 4 IoT Architecture Layer That You Should Know
- Top 5 HTML Tricks That You Should Know
- 10 Python File System Methods You Should Know
- 10 Python In-Built Functions You Should Know
- Top 20 Essential Docker Commands You Should Know in 2023
- Learn English Easy in 2020: Everything You Should Know About Learning English
- What are all the common undefined behaviours that a C++ programmer should know about?
- CRM Terms Everyone Should Know
Kickstart Your Career
Get certified by completing the course
To Continue Learning Please Login
- Tutorials & Tech Support Guides
- Internet Tutorials
TCP and UDP Ports Explained
- Lawrence Abrams
- March 24, 2004
- Read 1,480,497 times
Introduction
In this tutorial we will discuss the concept of Ports and how they work with IP addresses. If you have not read our article on IP addresses and need a brush up, you can find the article here . If you understand the concepts of IP addresses, then lets move on to TCP and UDP ports and how they work.
The devices and comptuers connected to the Internet use a protocol called TCP/IP to communicate with each other. When a computer in New York wants to send a piece of data to a computer in England, it must know the destination IP address that it woud like to send the information to. That information is sent most often via two methods, UDP and TCP.
The two Internet workhorses: UDP and TCP
UDP? TCP? I know you are getting confused, but I promise I will explain this in very basic terms so that you can understand this concept.
TCP stands for Transmission Control Protocol. Using this method, the computer sending the data connects directly to the computer it is sending the data it to, and stays connected for the duration of the transfer. With this method, the two computers can guarantee that the data has arrived safely and correctly, and then they disconnect the connection. This method of transferring data tends to be quicker and more reliable, but puts a higher load on the computer as it has to monitor the connection and the data going across it. A real life comparison to this method would be to pick up the phone and call a friend. You have a conversation and when it is over, you both hang up, releasing the connection.
UDP stands for User Datagram Protocol. Using this method, the computer sending the data packages the information into a nice little package and releases it into the network with the hopes that it will get to the right place. What this means is that UDP does not connect directly to the receiving computer like TCP does, but rather sends the data out and relies on the devices in between the sending computer and the receiving computer to get the data where it is supposed to go properly. This method of transmission does not provide any guarantee that the data you send will ever reach its destination. On the other hand, this method of transmission has a very low overhead and is therefore very popular to use for services that are not that important to work on the first try. A comparison you can use for this method is the plain old US Postal Service. You place your mail in the mailbox and hope the Postal Service will get it to the proper location. Most of the time they do, but sometimes it gets lost along the way.
Now that you understand what TCP and UDP are, we can start discussing TCP and UDP ports in detail. Lets move on to the next section where we can describe the concept of ports better.
TCP and UDP Ports
As you know every computer or device on the Internet must have a unique number assigned to it called the IP address. This IP address is used to recognize your particular computer out of the millions of other computers connected to the Internet. When information is sent over the Internet to your computer how does your computer accept that information? It accepts that information by using TCP or UDP ports.
An easy way to understand ports is to imagine your IP address is a cable box and the ports are the different channels on that cable box. The cable company knows how to send cable to your cable box based upon a unique serial number associated with that box (IP Address), and then you receive the individual shows on different channels (Ports).
Ports work the same way. You have an IP address, and then many ports on that IP address. When I say many, I mean many. You can have a total of 65,535 TCP Ports and another 65,535 UDP ports. When a program on your computer sends or receives data over the Internet it sends that data to an ip address and a specific port on the remote computer, and receives the data on a usually random port on its own computer. If it uses the TCP protocol to send and receive the data then it will connect and bind itself to a TCP port. If it uses the UDP protocol to send and receive data, it will use a UDP port. Figure 1, below, is a represenation of an IP address split into its many TCP and UDP ports. Note that once an application binds itself to a particular port, that port can not be used by any other application. It is first come, first served.
<-------------------- 192.168.1.10 -------------------->
This all probably still feels confusing to you, and there is nothing wrong with that, as this is a complicated concept to grasp. Therefore, I will give you an example of how this works in real life so you can have a better understanding. We will use web servers in our example as you all know that a web server is a computer running an application that allows other computers to connect to it and retrieve the web pages stored there.
In order for a web server to accept connections from remote computers, such as yourself, it must bind the web server application to a local port. It will then use this port to listen for and accept connections from remote computers. Web servers typically bind to the TCP port 80, which is what the http protocol uses by default, and then will wait and listen for connections from remote devices. Once a device is connected, it will send the requested web pages to the remote device, and when done disconnect the connection.
On the other hand, if you are the remote user connecting to a web server it would work in reverse. Your web browser would pick a random TCP port from a certain range of port numbers, and attempt to connect to port 80 on the IP address of the web server. When the connection is established, the web browser will send the request for a particular web page and receive it from the web server. Then both computers will disconnect the connection.
Now, what if you wanted to run an FTP server, which is a server that allows you to transfer and receive files from remote computers, on the same web server. FTP servers use TCP ports 20 and 21 to send and receive information, so you won't have any conflicts with the web server running on TCP port 80. Therefore, the FTP server application when it starts will bind itself to TCP ports 20 and 21, and wait for connections in order to send and receive data.
Most major applications have a specific port that they listen on and they register this information with an organization called IANA. You can see a list of applications and the ports they use at the IANA Registry . With developers registering the ports their applications use with IANA, the chances of two programs attempting to use the same port, and therefore causing a conflict, will be diminished.
Users who read this also read:

IP Addresses Explained
Every machine on the the Internet has a unique number assigned to it, called an IP address. Without a unique IP address on your machine, you will not be able to communicate with other devices, users, and computers on the Internet. You can look at your IP address as if it were a telephone number, each one being unique and used to identify a way to reach you and only you.

Tracing a hacker
Have you ever been connected to your computer when something strange happens? A CD drive opens on its own, your mouse moves by itself, programs close without any errors, or your printer starts printing out of nowhere? When this happens, one of the first thoughts that may pop into your head is that someone has hacked your computer and is playing around with you. Then you start feeling anger tinged ...

Understanding and Using Firewalls
The Internet is a scary place. Criminals on the Internet have the ability to hide behind their computers, or even other peoples computers, while they attempt to break into your computer to steal personal information or to use it for their own purposes. To make matters worse, there always seems to be a security hole in your software or operating system that is not fixed fast enough that could ...

All about Networks
With so much of Computer use these days revolving around the Internet and communicating with others, its important that you understand what exactly a network is. Without networks, all communication between your computer and other computers whether it be instant messaging, email, web browsing, or downloading music could not be achieved. This tutorial will strive to teach you about networks and ...


The Hosts File and what it can do for you
When using the Internet most people connect to web sites, ftp servers or other Internet servers by connecting to a domain name, as in www.bleepingcomputer.com. Internet applications, though, do not communicate via domain names, but rather using IP addresses, such as 192.168.1.1. Therefore when you type a domain name in your program that you wish to connect to, your application must first convert ...

- Tutorials Home
- New Tutorials
- Popular Tutorials

How to enable Kernel-mode Hardware-enforced Stack Protection in Windows 11

How to use the Windows Registry Editor

How to backup and restore the Windows Registry
How to open a Windows 11 Command Prompt as Administrator

How to make the Start menu full screen in Windows 10
Not a member yet? Register Now
- Help center
- Chinese (traditional)
Learn more
- Case Study
- Knowledge Center
- Glossary
Getting Started (119)
Product Updates (117)
News & Announcements (40)
Self Service (10)
Troubleshooting Guide (6)
Client Reviews (5)
Configuration Guide (5)
Product Testing (4)
Installation Guide (3)
Hear It from Experts (1)
Optics and Transceivers (97)
Switches (97)
Networking Devices (62)
Network Cabling and Wiring (59)
Optical Networking (18)
Networking (84)
Fiber Optic Communication (53)
Data Center (30)
General (26)
Wireless and Mobility (8)
Business Type (6)
Routing and Switching (5)
United Kingdom (1)
- Product Updates
- Networking Devices
- Case Study
- Knowledge Center

Server Ports Basics You Must Know

In network technology, server ports are categorized into physical ports and logical ports, also known as virtual ports. Physical ports, like Ethernet, LAN, and USB ports, serve as connectors for various network devices such as ADSL modems, hubs, switches, and routers. On the other hand, logical ports primarily pertain to TCP/IP protocol ports, distinguished by port numbers ranging from 0 to 65535. Examples include port 80 for web browsing services and port 21 for FTP services. Let's delve into the definition, classification, and methods to identify the open logical ports on a server.
''Also Check- Network Servers
What Are Server Physical Ports?
Server physical ports, integral components among server ports, encompass visual interfaces and input/output connectors essential for establishing communication between a server and other devices or computer networks. Various types of physical ports found on servers include VGA ports, IPMI ports, Ethernet ports, USB ports, and serial ports.
VGA Ports: Serving as a graphics card interface, the VGA port facilitates the transmission of video signals, significantly contributing to visual display capabilities. Simultaneously, the IPMI port, also known as the Intelligent Platform Management Interface port, plays a crucial role in server management.
Ethernet Ports: Essential for networking, Ethernet ports establish connections between servers and computer network equipment. The server LAN port, commonly linked to a router, plays a pivotal role in creating wired network connections across local area networks, metropolitan area networks, and wide area networks.
USB (Universal Serial Bus) Ports: Found on servers, USB ports provide connectivity for devices like mice, 4U chassis, and keyboards. With plug-and-play and hot-swappable functionality, server USB ports enhance convenience for tasks such as file copying and plug-in installations.
Server Serial Ports: Including COM ports, these ports function as standard cable interfaces. Enabling data transmission between serial ports and network devices like switches and microcomputers, the serial port empowers users to access, manage, and configure remote devices over the network using their computers.

What Are Server Logical Ports?
In response to the evolving demands of communication networks, the traditional physical ports of server ports are facing limitations. To address this, logical ports, commonly referred to as TCP/IP protocol ports, have emerged as a contemporary solution. These logical ports are categorized based on their distinct properties and services, each catering to specific needs and functionalities within the network.
Server Ports by Properties
With the development of communication networks, the physical ports of server ports can no longer meet network requirements, giving rise to logical ports. Logical ports, also known as TCP/IP protocol ports, are classified into various types based on their properties and services. Each of them provides different services.
Well-known Ports: Ranging from 0 to 1023, well-known ports are dedicated to specific services, adhering to predefined service protocols on servers.
Registered Ports: Falling between 1024 and 49151, registered ports are also associated with server services. However, these ports lack clearly defined service objects, allowing different applications to redefine them based on their requirements.
Dynamic / Private ports: Spanning from 49152 to 65535, dynamic or private ports are typically not allocated for common services. These ports are considered vulnerable to Trojan horse attacks, and caution is advised in their use.
Server Ports by Services
If categorized based on the different service modes, ports can be further divided into two types: "TCP protocol ports" and "UDP protocol ports." This is because computers typically communicate with each other using the TCP and UDP communication protocols. You can click here to view the list of server TCP ports and UDP ports.
TCP Protocol
Transmission Control Protocol (TCP) stands as a foundational connection-oriented communication protocol. This protocol plays a pivotal role in enabling computing devices and applications to transmit data across networks while ensuring its delivery. TCP is integral to the seamless functioning of the global internet. The common ports used with the TCP protocol include the following:
FTP (File Transfer Protocol): Operating on the seventh layer of the OSI model and the fourth layer of the TCP model (application layer), FTP is a set of standard protocols for network file transfer. Users can communicate with another host using file operations through the FTP protocol.
Telnet: This port serves remote login purposes, allowing users to connect to a computer remotely using their own identity through servers. Telnet provides a communication service based on DOS mode.
SMTP: Ensuring high-reliability email transmission, SMTP operates as a mail transfer service built on the FTP file transfer service. Primarily used for transferring mail information between systems, SMTP notifies users about incoming letters, hence its association with mail servers.
POP3: Used for receiving mail and corresponding to SMTP, POP3 operates on port 110. When servers have the appropriate POP3 protocol program, users can receive mail through their mail program.
UDP Protocol
The UDP protocol within server ports operates as a connectionless transmission control protocal situated in the OSI reference model. Primarily utilized in data services where packet transmission order is not critical, UDP is applicable to multiple applications concurrently running on a server. Noteworthy UDP port numbers encompass 53 (DNS), 69 (TFTP), and 161 (SNMP). Prominent applications utilizing UDP protocols include TFTP, SNMP, NFS, DNS, and BOOTP.

Difference Between TCP and UDP
The TCP and UDP protocol ports on the server ports provide different services for a wide variety of devices connected to the server, which allows them to coexist under the same IP address . So what is the difference between the TCP protocol port and the UDP protocol port? Here is the answer.

TCP ports provide a more reliable service link because they must establish endpoints between sending and receiving locations. These ports keep track of data, ensuring that packets are delivered to recipients in a safe and orderly manner.
UDP ports boast faster connection speeds but with relatively lower reliability. These ports permit data to be sent out of order and lack the tracking and inspection capabilities found in TCP ports. They are primarily employed for speed-critical operations, including online gaming or video conferencing.
Checking Open Logical Ports on the Server
To retrieve information about your server ports, you can utilize the Netstat command on your computer. Netstat is commonly employed to present statistical data concerning IP, TCP, UDP, and ICMP protocols, offering insights into the network connections associated with each server port on the machine. Functioning as a program accessing network and kernel-related information, Netstat delivers comprehensive reports on TCP connections, TCP and UDP monitoring, and process memory management.
Understanding your server port information is crucial for maintaining control over your applications. Since different applications rely on specific server ports, monitoring them becomes essential for ensuring system stability. In cases where certain ports are inactive or unusable, prompt attention and troubleshooting are necessary. Additionally, opening a port through router configurations can be a solution for directing traffic to specific devices or applications. It's important to highlight that manipulating certain ports may be required to navigate firewalls and prevent hindrances to their functionality.
- # Networking Devices
You might be interested in

Email Address
Please enter your email address.
Please make sure you agree to our Privacy Policy and Terms of Use.

Cloud-based Networks Grow with Your Business

Anchor Your Hybrid Cloud Networking Strategy
- Network Cabling and Wiring
- Buying Guide
- Fiber Optic Communication
- Optics and Transceivers
- Data Center
- Ethernet Patch Cords
- Business Type
- Routing and Switching
- Optical Networking
- Best Practices
- 10G Network
- Home Networking

Fiber Optic Cable Types: Single Mode vs Multimode Fiber Cable
May 10, 2022

Layer 2 vs Layer 3 Switch: Which One Do You Need?
Oct 6, 2021

Multimode Fiber Types: OM1 vs OM2 vs OM3 vs OM4 vs OM5
Sep 22, 2021

Running 10GBASE-T Over Cat6 vs Cat6a vs Cat7 Cabling?
Mar 18, 2024

PoE vs PoE+ vs PoE++ Switch: How to Choose?
Mar 16, 2023
- CCNA 200-301
- CCNA 200-301 Labs
- CCNP 350-401 ENCOR
- CCNP 350-401 ENCOR Labs
- CCNP 300-410 ENARSI
- CCIE Enterprise Infrastructure
- Cisco Packet Tracer Lab Course
- NRS II IRP Course
- NRS II MPLS Course
- NRS II Service Architecture
- Nokia Configuration Course
- Nokia SRC Program
- JNCIA Junos
- HCIA (HCNA)
- HCIA Configuration Course
- What is Huawei R&S Certification?
- Huawei ICT Certifications
- Python Course
- IPv6 Course
- IP Multicast Course
- NRS I Configuration Course
- Cisco Packet Tracer How To Guide
- Online Courses
- Udemy Courses
- CCNA Flashcard Questions
- Protocol Cheat Sheets
- Subnetting Cheat Sheet
- Linux Cheat Sheet
- Python Cheat Sheet
- CLI Commands Cheat Sheets
- Miscellaneous Cheat Sheets
- Cisco Packet Tracer Labs
- Cisco GNS3 Labs
- Huawei eNSP Labs
- Nokia GNS3 Labs
- Short Config Videos
- Network Tools
- IPCisco on Social Media
- Network Engineer Interview Questions
- Personality Interview Training
- Sign In/Up | Members
- Lost password
- Sign In/Sign Up
- ENROLL HERE
- Network Ports
In computer networking, there are network port numbers used for various applications. The range of these network ports are from 0 to 65535 . There are three different port types used networking. These network port types are given below:
- Well-known Ports (0 – 1023)
- Registered Ports (1024 – 49151)
- Dynamic Ports (Private Ports) (49152 – 65565)
Some of these port numbers are well-known ports. These well-known ports are the reserved ports between 0 and 1023 . The full list of these network port numbers are given in RFC 1700. IANA (Internet Assigned Numbers Authority) assigns these well-known ports.
The other network ports are registered ports between 1024 and 49151 . These ports are assigned by IANA for specific services.
The last part of ports in networking are dynamic ports. Daynamic ports are the ports from 49152 to 65565 . These ports in networking are not registered with IANA.
TCP (Transmission Control Protocol) and UDP (User Datagram Protocol) uses these well-known ports. Only one port is required for full-duplex, bidirectional traffic. Beside SCTP (Stream Control Transmission Protocol) and DCCP (Datagram Congestion Control Protocol) use these ports.
You can download the Cheat Sheet about Well-known network ports.
Table of Contents
Well Known Ports in Networking
Well-known network ports are from 0 to 1024 . These port numbers are given by IANA (Internet Assigned Numbers Authority) . And the full list of these port numbers are in RFC 1700.
Some of these well-known ports are used by TCP and some of them are used UDP. These TCP and UDP ports are also asked in many network engineering technical interviews as interview questions . So, what are these ports in networking?
Well-known TCP ports are the network ports used by the applications that works with TCP as transport protocol. So, what are these applications that uses well-known TCP ports ?
For example, FTP (File Transport Protocol) is one of the applications that uses TCP ports. The FTP ports are TCP port 20 and TCP port 21 . The other applcation that uses TCP as transport protocol is Telnet. Telnet uses TCP port 23 .
Well-known UDP ports are the network ports used by the applications that works with UDP as transport protocol. So, what are these applications that uses well-known UDP ports ?
For example TFTP (Trivial File Transport Protocol) is one of the applciations that uses UDP ports. UDP port 69 is used by TFTP. Another example that uses UDP as transport protocol is SNMP. SNMP uses UDP port 161 for SNMP and UDP port 162 for SNMP trap messages.
Below, you can find all the wellknown ports used by the applications that uses TCP & UDP network ports .
Registered Network Ports
Registered networking ports start from port 1024 to 49151. IANA (Internet Assigned Numbers Authority) assigns these registerd network ports. Below, you can find these registered networking ports
Dynamic Networking Ports
Registered networking ports are the ports from 49152 to 65565. These ports can be used locally or dynamically by the applications. They are not assigned by IANA.
Network Ports Practice
Quesitons for networking ports, question 1: which network port range is reserved as well-known ports.
a) 0 – 1024
b) 1024 – 49151
c) 49152 – 65565
Question 2: Which network port range is reserved as Registered Ports ?
Question 3: which network port range is reserved as dynamic ports , question 4: network port numbers are assigned by …., question 5: which ones are the default network ports for ftp .
a) UDP 20, 21
b) TCP 20, 21
c) UDP 22,23
d) TCP 22,23
Question 6: Which ones are the default SNMP Ports?
a) UDP 157, 158
b) TCP 157, 158
c) UDP 161, 162
d) TCP 161, 162
Question 7: What is the default Telnet port?
Question 8: which ones are the default tftp port, question 9: tcp port 25 is the default network port of …., question 10: udp port 123 is the default network port of …..
Answers: 1) a 2) b 3) c 4) b 5) b 6) c 7) d 8) a 9) d 10) c
Leave a Reply Cancel reply
Your email address will not be published. Required fields are marked *
CCNP Enterprise 350-401 ENCOR
- IPv4 Subnetting
- Private IPv4 Address Ranges
- APIPA Addresses
- IPv4 Addressing
- IPv6 Addressing
- IPv6 Link Local Addresses
- IPv6 Neighbour Discovery Protocol
- IPv6 Floating Static Routing
- IPv6 Address Types
- IPv6 Configuration Example on Packet Tracer
- IPv6 and Subnetting
ICMP and ARP
- Ping Command
- Gratuitous ARP
- ICMP (Internet Control Message Protocol)
- Address Resolution Protocol (ARP)
Routing Fundamentals
- IPv6 Static Route Configuration on Cisco IOS
- Policy Based Routing (PBR)
- Static Route Configuration on Cisco Routers
- IPv6 Routing Protocols
- Dynamic Routing Protocols
- IP and Layer 3 Overview
- RIPng Configuration Example on Cisco IOS
- RIP Configuration With Packet Tracer
- RIPng (RIP Next Generation)
- Routing Information Protocol (RIP)
- EIGRP (Enhanced Interior Gateway Routing Protocol)
- EIGRP Tables
- EIGRP Packet Types and Neighbourship
- Key Configurations on EIGRP
- EIGRP Configuration With Packet Tracer
- EIGRP for IPv6
- EIGRP For IPv6 Configuration On Cisco IOS
- OSPF Virtual-Link Configuration On Packet Tracer
- OSPF Passive Interface
- LSDB (Link State Database)
- OSPF Area Border Router (ABR) and ASBR
- OSPF Cost and Shortest Path First
- OSPF NSSA and Totally NSSA on Cisco Packet Tracer
- OSPF Stub Area and Totally-Stub Area on Cisco Packet Tracer
- OSPF External Routes on Cisco Packet Tracer
- OSPF Standard Area and Backbone Area on Cisco Packet Tracer
- OSPFv3 Configuration Example on Cisco IOS
- OSPFv3 (Open Shortest Path First Version 3)
- Cisco Single Area OSPF Configuration
- Other OSPF Key Points
- OSPF Network Types
- OSPF Area Types
- OSPF LSA Types
- OSPF Packet Types
- OSPF Adjacency
- OSPF(Open Shortest Path First) Overview
- BGP Next Hop Self Command
- BGP Multi Hop Command
- BGP Neighbor Update-Source
- Cisco eBGP Configuration on GNS3
- BGP Route Reflector
- Cisco BGP Route Reflector Configuration on GNS3
- BGP Path Attributes - MED
- BGP Path Attributes - Origin
- BGP Path Attributes - AS Path
- BGP Path Attributes - Local Preference
- BGP Path Attributes - Weight
- BGP Configuration Example on Packet Tracer
- BGP AD and BGP Path Attributes
- IBGP and EBGP
- BGP Peers, BGP Sessions, BGP Messages
- BGP (Border Gateway Protocol)
Layer 2 Technologies
- PPPoE Configuration With Packet Tracer
- Metro Ethernet Overview
- Frame-Relay Configuration with both Inverse-ARP and Frame-Relay Map
- Frame Relay Point-to-Point Configuration
- Multipoint Frame Relay Configuration
- Point-to-Point Protocol over Ethernet (PPPoE)
- HDLC and PPP
- PPP Configuration on Cisco
VPN Technologies
- VPN Types and Protocols of VPN
DHCP and DNS
- Cisco DHCP Relay Agent Configuration with GNS3
- Stateless Address Auto Configuration
- DHCPv6 Overview
EtherChannels
- Etherchannel Cisco PAgP Configuration on GNS3
- PAgP Configuration Example
- LACP Configuration on Cisco IOS
- Link Aggregation Control Protocol
- PAT Configuration with Packet Tracer
- NAT (Network Address Translation)
- Static NAT Configuration with Packet Tracer
- Dynamic NAT Configuration with Packet Tracer
Access Lists
- Extended ACL Cisco Configuration
- Access Control Lists for Traffic Control
- Standard ACL Configuration With Packet Tracer
- DHCP Snooping Configuration on Packet Tracer
- REST API Security
- Cisco 802.1x Configuration
- WebAuth (Web Authentication)
- What is DHCP Snooping?
- Access Control Lists
- Control Plane Policing (CoPP)
- Basic Cisco Router Security Configuration
- SNMP Configuration On Cisco IOS
- SNMP – Overview
Spanning Tree
- PVST+ and Rapid PVST+Configuration on Packet Tracer
- PVST+ and Rapid PVST+
- MST Configuration on Cisco
- MST (Multiple Spanning Tree)
- STP Operation
- Spanning Tree Protocol
- Rapid Spanning Tree Protocol
- STP Portfast Configuration on Cisco Packet Tracer
- RSTP Configuration on Cisco Packet Tracer
- STP Configuration on Cisco Packet Tracer
- Inter VLAN Routing Configuration on GNS3
- Inter VLAN Routing Configuration Example
- VTP Configuration with Packet Tracer
- DTP and VLAN Frame Tagging Protocols
- Inter VLAN Routing with Router on Stick Topology
- VLANs (Virtual Local Area Networks)
- VLAN Port Assignment and VLAN Port Types
- VLAN Configuration on Cisco Packet Tracer
First Hop Redundancy
- HSRP Configuration on GNS3
- Cisco Stateful Switchover (SSO)
- GLBP Configuration on Cisco
- GLBP (Gateway Load Balancing Protocol)
- VRRP Configuration on Cisco
- VRRP (Virtual Router Redundancy Protocol)
- First Hop Redundancy Protocols
- QoS Policing and Shaping
- QoS Classification and Marking
Port Monitor
- ERSPAN Configuration on Packet Tracer
- Remote SPAN Configuration on Packet Tracer
- Local SPAN Configuration on Packet Tracer
- Cisco SPAN Overview
Path Virtualization
- IPSec Tunneling
- Cisco IPSec VPN Configuration
- Cisco Virtual Routing and Forwarding (VRF)
- GRE Tunnel Overview
- GRE Tunnel Configuration with Cisco Packet Tracer
Device Access Control
- Cisco SSH Configuration With GNS3
- Authentication, Authorization, Accounting
- AAA Protocols
Multicast Protocols
- Bidirectional PIM (BIDIR-PIM)
- Multicast Routing
- PIM-SM (PIM Sparse Mode)
- PIM-SSM (Source Specific Multicast)
- PIM-DM (PIM Dense Mode)
- PIM (Protocol Independent Multicast)
- IGMP Snooping
- IGMP Configuration
Cisco SD-WAN
- Cisco SD-WAN Verification
- Cisco vSmart Controller Configuration
- Cisco vBond Initial Configuration
- Cisco SD-WAN Components
- SD-WAN Architecture
Wireless Security
- EAPoL (Extensible Authentication Protocol over LAN)
- Pre-Shared Key (PSK)
Network Security Design
- 802.1x (Port Based Network Access Control)
- Network Security: Cisco Threat Defense
- MACsec (Media Access Control Security)
- Cisco TrustSec
- MAC Authentication Bypass (MAB)
IP Services
- Cisco NTP Configuration
- uRPF (Unicast Reverse Path Forwarding)
- Precision Time Protocol (PTP)
- NTP (Network Time Protocol)
Network Assurance
- Cisco Syslog Server Configuration with GNS3
- Conditional debugging
- Cisco Terminal Monitor and Cisco Logging Monitor
- Cisco Debug Command
- Cisco IP SLA and Configuration
- Flexible Netflow Configuration
- Flexible Netflow
- Netflow and Netflow Configuration
- Chef Overview
- Ansible vs Puppet vs Chef
- Ansible Overview
- Puppet Overview
- Data Serialization Languages: JSON, YAML, XML
- Network Automation Tools
- Cisco SD-Access Overview
- Traditional Network Management versus Cisco DNA Center
- Cisco DNA Center
- Cisco DNA and Intent-Based Networking (IBN)
- How Network Automation Impacts Network Management
- REST APIs Overview
Network Virtualization
- Cisco LISP (Locator ID Separation Protocol)
- Virtual Switching and Virtual Switch (vSwitch)
- Container vs Virtual Machine
- Virtual Extensible LAN (VXLAN)
- CAPWAP versus LWAPP
- Wireless Roaming: Layer 2 and Layer 3 Roaming
- LWAPP Protocol
- CAPWAP Protocol
- Access Point Discovery and Join Process
Other Lessons
Latest lessons.
- Coaxial Cable Details Part of: CCNA 200-301
- IPv4 vs IPv6 Comparison Part of: CCNA 200-301
- IGMPv3 Overview Part of: IP Multicast Course
- IGMPv3 Overview Part of: CCIE Enterprise Infrastructure
- Subnetting IPv6 Part of: CCIE Enterprise Infrastructure
- IPv6 and Subnetting Part of: CCNP Enterprise 350-401 ENCOR
- IPv6 Link Local Address Type Part of: CCIE Enterprise Infrastructure
- Cisco Switch Configuration on Cisco Packet Tracer Part of: CCNA 200-301
- Switch Configuration on Cisco Packet Tracer Part of: Cisco Packet Tracer Lab Course
- REST API Security Part of: CCNP Enterprise 350-401 ENCOR
- More Lessons
Latest Blog Posts

WHAT YOU WILL FIND?
- 250.000+ Students All Over The World
- 8.000+ Questions & Answers
- 100+ Lab Files & Cheat Sheets
- 30+ IT/Network Courses
- A Real Desire To Help You
- Daily Social Media Shares
- %100 Satisfaction
- CISCO Courses
- NOKIA Courses
- HUAWEI Courses
- JUNIPER Courses
- PYTHON Course
- KEY Courses
- VIDEO Courses
- UDEMY Courses
- Cheat Sheets
- Configuration Files
- Interview Questions
- IPCisco On Social Media
- Pärnu mnt. 139c – 14, 11317, Tallinn, Estonia
- [email protected]
Subscribe Now
* You will receive the latest news and updates on your favorite celebrities!
Trending News

40 Network Protocols with Port Numbers, Transport Protocols and Meanings
40 Network Protocol Names And Port Numbers With Their Transport Protocols And Meanings tabulated by Precious Ocansey (HND, Network Engineer).
Before going straight to the table.
Firstly, what are Network Protocols?
Network protocols are the languages and rules used during communication in a computer network. There are two major transport protocols namely;
TCP and UDP
TCP which stands for “Transmission Control Protocol”, is a suite of communication protocols used to interconnect network devices on a local network or a public network like the internet. TCP is known as “connection-oriented” protocols as it ensures each data packet is delivered as requested. Therefore, TCP is used for transferring most types of data such as webpages and files over the Internet.
UDP which stands for “User Datagram Protocol” is part of the TCP/IP suite of protocols used for data transferring. UDP is a known as a “connectionless-oriented” protocol, meaning it doesn’t acknowledge that the packets being sent have been received. For this reason, the UDP protocol is typically used for streaming media. While you might see skips in video or hear some fuzz in audio clips, UDP transmission prevents the playback from stopping completely.
Furthermore, TCP also includes built-in error checking means TCP has more overhead and is therefore slower than UDP, it ensures accurate delivery of data between systems. Therefore TCP is used for transferring most types of data such as webpages and files over the local network or Internet. UDP is ideal for media streaming which does not require all packets to be delivered.
Port Numbers: They are the unique identifiers given to all protocol numbers so they can be accessed easily.
Below is as written by Precious Ocansey. The 40 Network Protocols, their port numbers and their transport protocols
FREE Coupon: Complete Certificate Authority (ADCS) Server 2016 Course
How to blend ghanaian flag with an image - photoshop cs6.
Related posts
Configuring cep/ces, online responders, ndes and ca security on server 2016 (part 2) , 5 – private and public ipv4 address , free coupon: complete certificate authority (adcs) server 2016 course , configure fsrm’s storage report (windows server 2012 r2) , configuring file screening (windows server 2012 r2) , 4 – classes of ipv4 address .
Good job.interesting more grace sir
Iṣẹ rere, diẹ ẹ sii oore ọfẹ
ICMP does not use any port, 1 is its protocol number.
Updated. Thank you
IGMP does not use a transport layer protocol such as TCP or UD
Leave a Reply Cancel reply
Save my name, email, and website in this browser for the next time I comment.
Notify me of follow-up comments by email.
Notify me of new posts by email.
This site uses Akismet to reduce spam. Learn how your comment data is processed .
Today's pick
How to set up a virtual machine , recon for pentesting using python (email grabbing) , fix: outdated npm packages (deprecated) in node js project , svn fix trac error: no node at revision wp plugin , deploy react app on google cloud with cloud run 2022 , how to set up a virtual machine , svn fix trac error: no node at revision wp plugin , fixed xcodebuild: failed to load code for plug-in – repeatedly being asked to install command line tools , subscribe for newsletter.
* You will receive the latest news and updates on your favorite topics!

How to Downgrade Flutter Version – FIXED
Learn how to downgrade your flutter version to a lower version, in this article we will reduce the flutter version…

Generate Resources for Android Playstore & iOS Apple Store Flutter
In this post, we’ll generate resources for the flutter app we created in the previous post. we’ll be learning how…

Build a Quiz App using Flutter for Android and iOS
In this post we’ll be working with Flutter, a fast-rising Developer tool built by Google to develop an Android App,…
Setup Flutter on Kali, Ubuntu, and any other Linux Distro
In this post, we’ll be learning how to set up your Flutter on Linux for development. Flutter is a fast-rising…

FIXED xcodebuild: Failed to load code for plug-in – Repeatedly Being Asked to Install Command Line Tools
Hey there, updating your MacOS Montery Xcode can be a pin in the a$$ especially when you got Xcode working…
Username or Email Address
Remember Me
Registration is closed.
- Engineering Mathematics
- Discrete Mathematics
- Operating System
- Computer Networks
- Digital Logic and Design
- C Programming
- Data Structures
- Theory of Computation
- Compiler Design
- Computer Org and Architecture
- How to Find Your IP Address?
- How to Find Your Mac Address?
- How To Set Up a Router?
- How to Find Your MAC Address in Windows 11?
- How To Find Your Router's IP through the Control Panel?
- How Many Ways to Find Your IP Address?
- How to Get Open Port Banner in Python
- How to Change FTP Port in Linux?
- How To Check IMEI Number
- How to Open a URL?
- 50 Common Ports You Should Know
- What is Ports in Networking?
- How to Find Your Computer’s Serial Number?
- How to Map Ports in Docker?
- How to Find Your IP Address on Windows?
- Node.js URL.port API
- How to bind to port number less than 1024 with non root access?
- Program to check for a Valid IMEI Number
- Major World Seaport and their Location
How To Find Your Port Number ?
Answer: we can find port number using command line tool, and using resource monitor., methods for find the port numbers on your device, 1. using command line tool like netstat.
‘Netstat’ stands for Network Statistics and displays our computer’s current network connection and port activation. Below are the steps:
- Open Command Prompt: On a Windows machine, open Command Prompt by searching for it in the Start menu or by pressing `Windows + R`, typing `cmd`, and pressing Enter. Similarly, we can open Terminal on macOS and Linux.
- Use Command ‘netstat-n’: For Windows we use the command ‘netstat -n’ to list all active connections and listening ports. For example, you can run ‘netstat -n’ to list all listening TCP ports, and ‘netstat -a’ will show you which ports are open and what services are using them. Whereas for macOS/Linux we can use the command ‘netstat -tuln’. Then the list of all the port numbers will be displayed.
2. Using Resource Monitor
- Press ‘Ctrl + Shift + Esc’ to open the Task Manager.
- Then, Click on the “Performance “Tab.
- Click on the Open Resource Monitor at the bottom or top-right corner.
- In the resource Monitor window, go to the “Network” tab and then you will see a list of processes and their associated port .
Conclusion:
By utilizing the tools like ‘ Netstat’ we can troubleshoot and monitor our system and network, and also gain the insights into network security, and identify any processes using specific ports. It will help us in managing and securing our system efficiently.
Please Login to comment...
Similar reads.
- Computer-Networks-MAQ
Improve your Coding Skills with Practice
What kind of Experience do you want to share?

IMAGES
VIDEO
COMMENTS
Learn the meaning and usage of some of the most often-encountered network ports and their associated services, such as SSH, FTP, HTTP, and DNS. Find out how to connect to different services using port numbers and what they mean.
50 Common Ports You Should Know. Port number is a 16-bit numerical value that ranges from 0 to 65535. Well-known port (0-1023), registered port (1024-49151), and dynamic port is three types of port number space. (49152-65535). These ports can be opened and used by software applications and operating system services to send and receive data over ...
A crucial domain of expertise in IT-related certifications such as Cisco Certified Network Associate (CCNA) and those of CompTIA is port numbers and associated services, which this common ports and protocols cheat sheet covers. If you want to remember a port number or protocol, this cheat sheet will help everyone, from students to professionals.
To stop these attacks, a firewall may block port 3389 by default. Since this port is only used for remote desktop connections, such a rule has little impact on day-to-day business operations unless employees need to work remotely. What are the different port numbers? There are 65,535 possible port numbers, although not all are in common use.
well-known port numbers: The well-known port numbers are the port number s that are reserved for assignment by the Internet Corporation for Assigned Names and Numbers ( ICANN ) for use by the application end points that communicate using the Internet's Transmission Control Protocol ( TCP ) or the User Datagram Protocol ( UDP ). Each kind of ...
143 (TCP, UDP) - IMAP. 161, 162 (UDP) - SNMP. 443 (TCP) - HTTPS. 587 (TCP) - SMTP. 993 (TCP) - IMAPS. Conclusion. As a server administrator, it's essential to understand the functions of common services and their respective port numbers. Similar to how an IP address determines the computer's identity, the network port is key in ...
A port in networking is a virtual checkpoint that directs incoming and outgoing data traffic to the correct program or service on a device. In the most basic sense, a port is a start and endpoint of communication. A port, also known as a network connection, serves as a channel through which different computer devices and applications communicate.
A port number is a 16-bit number with a 0 to 65535 decimal value range. There are three various types of port number spaces: well-known ports (0-1023), registered ports (1024-49151), and dynamic ports (49152-65535). Well-known or Reserved Ports: 0-1023; Registered Ports: 1024-49,591; Dynamic Ports: 49,592-65,535
Port number. For TCP and UDP, a port number is a 16-bit unsigned integer, thus ranging from 0 to 65535. For TCP, port number 0 is reserved and cannot be used, while for UDP, the source port is optional and a value of zero means no port.A process associates its input or output channels via an internet socket, which is a type of file descriptor, associated with a transport protocol, a network ...
In both TCP and UDP, port numbers start at 0 and go up to 65535. The lower ranges are dedicated to common internet protocols such as port 25 for SMTP and port 21 for FTP. To find the specific values used by certain applications, view a list of the most popular TCP and UDP port numbers. For Apple software, view the TCP and UDP ports used by ...
Computers and routers automatically manage network traffic traveling via their virtual ports. Network firewalls also provide some control over the flow of traffic on each virtual port for security purposes. In IP networking, these virtual ports are structured via port numbers, from 0 through 65535. For example, port 80 lets you access websites ...
This is a list of TCP and UDP port numbers used by protocols for operation of network applications. The Transmission Control Protocol (TCP) and the User Datagram Protocol (UDP) only need one port for duplex, bidirectional traffic.They usually use port numbers that match the services of the corresponding TCP or UDP implementation, if they exist. The Internet Assigned Numbers Authority (IANA) is ...
The port number 80 is the open port of server.here Google server had an open port (80) also Yahoo had an open port (80). Both Google and Yahoo had different IP addresses. If I want to connect Google server,I will open a new port,for example I will open port 5000, at the same time I will open another port 5002 to connect with Yahoo server. Example :
Ports explained. A port is a 16-bit number used to identify specific applications and services. TCP and UDP specify the source and destination port numbers in their packet headers and that information, along with the source and destination IP addresses and the transport protocol (TCP or UDP), enables applications running on hosts on a TCP/IP ...
Every port in computer networking is associated with a specific protocol or service, and each protocol or service is assigned a standard port number by the Internet Assigned Numbers Authority (IANA). These would be organized into three ranges - well-known ports (0 to 1023), registered ports (1024 to 49151), and dynamic/private ports (49152 to ...
COMMON PORTS packetlife.net TCP/UDP Port Numbers 7 Echo 19 Chargen 20-21 FTP 22 SSH/SCP 23 Telnet 25 SMTP 42 WINS Replication 43 WHOIS 49 TACACS 53 DNS 67-68 DHCP/BOOTP 69 TFTP 70 Gopher 79 Finger 80 HTTP 88 Kerberos 102 MS Exchange 110 POP3 113 Ident 119 NNTP (Usenet) 123 NTP 135 Microsoft RPC 137-139 NetBIOS 143 IMAP4 161-162 SNMP 177 XDMCP 179 BGP 201 AppleTalk 264 BGMP 318 TSP 381-383 HP ...
If it uses the TCP protocol to send and receive the data then it will connect and bind itself to a TCP port. If it uses the UDP protocol to send and receive data, it will use a UDP port. Figure 1 ...
These port numbers are divided into 3 ranges as per use case: Well-known ports (0-1023): These ports are also known as system ports, which are assigned to specific services by IANA (Internet Assigned Numbers Authority). ... Network Basic Input/Output System (NetBIOS) is a network service that enables applications of various computers to ...
Physical ports, like Ethernet, LAN, and USB ports, serve as connectors for various network devices such as ADSL modems, hubs, switches, and routers. On the other hand, logical ports primarily pertain to TCP/IP protocol ports, distinguished by port numbers ranging from 0 to 65535. Examples include port 80 for web browsing services and port 21 ...
One of the many fundamental things to know as a network engineer is the function and port number used by a number of common services as well as many that are typically implemented during the course of a network engineer's career. This article takes a look at these protocols, provides a basic description of their function and lists the port numbers that they are commonly associated with.
The network layer has to do nothing with ports, their protocols only care about IP Addresses. Ports are assigned by computer i.e. operating system to different applications. Ports help computer to differentiate between incoming and outgoing traffic. Since the port is a 16-bit unsigned number it ranges from 0 to 65535.
There are three different port types used networking. These network port types are given below: Well-known Ports (0 - 1023) Registered Ports (1024 - 49151) Dynamic Ports (Private Ports) (49152 - 65565) Some of these port numbers are well-known ports. These well-known ports are the reserved ports between 0 and 1023.
The 40 Network Protocols, their port numbers and their transport protocols. 1. File Transfer Protocol (FTP) It is a protocol that carries data guarantees that data will be delivered properly. 2. Secure Shell (SSH) It is a cryptographic network protocol used to secure data communication. 3.
Answer: We can find port number using command line Tool, and using resource monitor. Methods For Find the Port Numbers On Your Device 1. Using Command Line Tool like Netstat 'Netstat' stands for Network Statistics and displays our computer's current network connection and port activation. Below are the steps: