APNIC IPv6 Allocations
Allocations of IPv6 address space are made to regional Internet registries according to their needs, based on allocation rates they publish. Specifically, RIRs are eligible for further allocations if their available space of existing allocations is less than 50% of a /12 address block, or less than their necessary space for the following 9 months.

Current Space and Eligibility
24-month forecast.
The chart below uses APNIC's current average allocation rate to forecast their available IPv6 space over the next 24 months. This can be used to estimate if APNIC will become eligible to apply for additional IPv6 space in the near future.
Allocations by Status
Status of IPv6 addresses IANA has allocated to APNIC.
Allocations by Country
Total number of IPv6 addresses allocated to network operators by APNIC, grouped by country
Allocations for the Last Six Months
Number of IPv6 addresses allocated by APNIC to their network operators in the last six months.
Fragmented Allocations by Prefix Length
IPv6 address blocks smaller than /32 are considered "fragmented". The chart below shows the number of fragmented blocks held by APNIC.
IPv6 Capable Rate by country (%)
30 day average (19/04/2024 - 18/05/2024)
Date: Window (Days)
Map Options
IP Address by Country 2024
Every computer or other internet-enabled device (smart TV, cell phone, web server, etc.) on a network must have a unique identifier. Most devices and networks communicate using the TCP/IP protocol, in which each device is identified via a numerical label known as an Internet Protocol address, commonly referred to as an IP address. IP addresses can be either static, meaning a device has the same IP address at all times; or dynamic, meaning the IP address may change from time to time, such as when a device is powered down and restarted. IP addresses are also reusable, meaning if a device no longer requires access to the network, its IP address can be reallocated to a different device.
Top 10 Countries with the most IP (IPv4) Addresses:*
Types of ip address: ipv4 and ipv6 defined and differentiated.
Current IP addresses each follow one of two standards: IP Version 4 (IPv4) or IP Version 6 (IPv6). IPv4, the internet's original IP protocol, uses 32 binary bits to create a single unique address that is expressed by four numbers, each ranging from 0 to 255 and separated by decimals. For example: 104.221.95.92.
By comparison, the newer and more complex IPv6 standard uses 128 binary bits to create a single unique address that is expressed by eight groups of hexadecimal numbers (which include not only the numbers 0-9 but the letters A-F), each ranging from 0 to FFFF and separated by colons. For example: 2001:23F5:B415:2F61:02A2:8C4B:A375:8149.
Why are there two types of IP address?
IP addresses are unique and have a fixed length. Because of these constraints, the number of possible IP addresses that can exist is finite. There are 4,294,967,296 (Nearly 4.3 billion) IPv4 addresses, 600 million of which are reserved and cannot be used for public routing. This limitation caused little concern in the early days of the internet, because of the vast number of IPv4 addresses available. However, the growth of the internet and the proliferation of internet-enabled devices over the following decades made clear that eventually even four billion IP addresses would be too few.
Several new technologies were formulated to stave off the looming shortage of IPv4 addresses, including network address translation (NAT) and Classless Inter-Domain Routing (CIDR). The ultimate solution arrived with the launch of IPv6. While IPv4 was a 32-bit protocol limited to just under 4.3 billion addresses (2 to the power of 32), IPv6 is a 128-bit protocol with nearly 340 undecillion possible addresses (2 to the power of 128), a functionally infinite supply.
IPv4 and IPv6 networks are incompatible with one another. This means, for example, that a cell phone with an IPv4 address could not access a website stored on a web server that used only IPv6. However, the vast majority of modern devices and operating systems are capable of connecting to the internet via either protocol. At present, IPv4 is still the dominant protocol, thanks to this ongoing device-level support and the presence of more than 4 billion already-allocated IPv4 addresses. However, IPv6 is expected to overtake it at some point in the future.
Per-country allocations of IP addresses around the world
The Internet Assigned Numbers Authority (IANA) is the organization charged with distributing all non-reserved IP addresses to the world. This process is executed using a nested system in which increasingly smaller satellite agencies allocate the IPs to increasingly smaller territories. The IANA performs the first allocation, distributing IP addresses to Regional Internet Registries (RIRs) in five broad regions (which roughly correspond to the continents.
Regional Internet Registries perform the second round of allocations, doling out the IPs to each individual country's National Internet Registry (NIR). The NIRs then allocate the IPs to smaller Local Internet Registries (LIRs), which allocate them to Internet Service Providers (ISPs), which allocate them to individual users and devices. In-use IPs are classified as utilized . In countries that lack local registries, the national registries allocate directly to the ISPs.
Global ISP Allocation Regions (all data IANA 2022/09):
The number of addresses allocated to a given country does not necessarily correlate with that country's population numbers. Rather, it is more closely tied to each country's need for IP addresses. As a rule, countries that have high incomes , are more developed , or show a high level of innovation and technological advancement have more robust internet infrastructure and a larger number of smart devices, websites, and other internet-based businesses—which translates to greater need for IP addresses—than do low-income and middle-income countries that are still developing .
Countries with the largest (and smallest) allocations of IPv4 addresses
Of the more than 4 billion IPv4 addresses in existence, 1,541,605,760 (about 35.9% of the total number) are allocated to the United States . This is far and away the highest number allocated to any country. Using population metrics from 2012 (the year after the IANA allocated the final IPv4 addresses to various regional registries), this corresponds to roughly 4,911 IP addresses per 1,000 people.
China has the second-highest number of IPv4 addresses at 330,321,408, about 7.7% of the total number in existence. China is followed by Japan with 202,183,168 and the United Kingdom with 123,500,144. Germany has the fifth-highest number of IPv4 addresses with 118,132,104.
Vatican City , which has the smallest population of any sovereign state, has 17,920 IPv4 addresses. This equates to 21,435 IP addresses per 1,000 people (because Vatican City has fewer than 1,000 citizens).
What are bogons?
Factored into the 4.294 million existing IPv4 addresses are millions on bogon (short for "bogus logons") addresses, which are IP addresses that are either inaccurate or which have not yet been assigned by an ISP. Most Internet service providers and firewalls filter out bogons, which are typically created either on accident by misconfigured networks or deliberately by would-be hackers.
Finally, IP addresses are not to be confused with domain names , a similar-but-different identifier that can help pinpoint the country of origin of a website.
- IPv4 allocation totals are final, as all possible IPv4 addresses have been assigned to various national NIRs. Although existing IPv4 addresses may be recycled on a local or national level, they will not be reallocated to other countries.
- The % column indicates the percentage of the total global number of IPv4 addresses each country has been allocated.
- IPv6 addresses are allocated in ""/32"" blocks which can include thousands, millions, or billions of individual addresses depending upon how they are implemented. As such, the totals shown indicate blocks allocated, not individual addresses.
- IPv6 numbers shown are total allocations from all regions combined. For example, Albania has received 606 IPv6 allocations from RIPE NCC, but also 1 from APNIC, for a total of 607 allocations.
- IPv6 address totals shown include only those blocks that had been assigned to individual countries' NIRs as of August 2022. For full IPv6 allocations per region, see the table in the body text.
Download Table Data
Enter your email below, and you'll receive this table's data in your inbox momentarily.
How can I tell what country an IP address is from?
Frequently asked questions.
- Internet IP Address 2024 Report - IP2Locations
- RIPE NCC IPv6 Allocations - IANA
- LACNIC IPv6 Allocations - IANA
- ARIN IPv6 Allocations - IANA
- APNIC IPv6 Allocations - IANA
- AFRINIC IPv6 Allocations - IANA
- Number Resources - Internet Assigned Numbers Authority
- IPv6 and IPv6 Addresses - IPCisco
- List of countries by IPv4 Address Allocation - Wiki
- Global Policy for Post Exhaustion IPv4 Allocation Mechanisms by the IANA | (Ratified 6 May 2012) - ICANN
- IPv4 Address Exhaustion - Wiki
- IPv6 deployment - Wiki
- What Is an IP Address? - Avast
- IPv4 and IPv6 address formats - IBM
- Bogon - CyberHoot
- Bogon Filtering - Wiki

IP Address Ranges by Country
This page displays the complete IPv4 address ranges organized by country. There are 249 countries listed below, and each link will bring you to a new page containing the respective IP address ranges.
If you are interested to learn more about the ranking of IP addresses allocated for each country, please visit IP Address Reports for details.
Afghanistan
Aland Islands
American Samoa
Antigua and Barbuda
Bolivia (Plurinational State of)
Bonaire, Sint Eustatius and Saba
Bosnia and Herzegovina
Bouvet Island
British Indian Ocean Territory
Brunei Darussalam
Burkina Faso
Cayman Islands
Central African Republic
Congo (Democratic Republic of the)
Cook Islands
Cote d'Ivoire
Dominican Republic
El Salvador
Equatorial Guinea
Falkland Islands (Malvinas)
Faroe Islands
French Guiana
French Polynesia
Guinea-Bissau
Iran (Islamic Republic of)
Isle of Man
Korea (Democratic People's Republic of)
Korea (Republic of)
Lao People's Democratic Republic
Liechtenstein
North Macedonia
Marshall Islands
Micronesia (Federated States of)
Moldova (Republic of)
Netherlands
New Caledonia
New Zealand
Norfolk Island
Northern Mariana Islands
Palestine, State of
Papua New Guinea
Philippines
Puerto Rico
Russian Federation
Saint Barthelemy
Saint Helena, Ascension and Tristan da Cunha
Saint Kitts and Nevis
Saint Lucia
Saint Martin (French Part)
Saint Pierre and Miquelon
Saint Vincent and the Grenadines
Sao Tome and Principe
Saudi Arabia
Sierra Leone
Sint Maarten (Dutch Part)
Solomon Islands
South Africa
South Georgia and the South Sandwich Islands
South Sudan
Svalbard and Jan Mayen
Switzerland
Syrian Arab Republic
Taiwan (Province of China)
Tanzania, United Republic of
Timor-Leste
Trinidad and Tobago
Turkmenistan
Turks and Caicos Islands
United Arab Emirates
United Kingdom of Great Britain and Northern Ireland
United States of America
United States Minor Outlying Islands
Venezuela (Bolivarian Republic of)
Virgin Islands (British)
Virgin Islands (U.S.)
Wallis and Futuna
Ready to Get Started?
Sign up now and you will be able to access ALL IP databases for FREE!
No hidden costs. No credit card required.

Geolocate Your Visitors Location
Enhance your applications with essential geolocation data by using our FREE databases.
IP Address Allocation by Country
This document was generated automatically on Sun May 19 03:30:46 UTC 2024.
For information on the sources behind the data, please see the project repository on github .
Network block overlap: ARIN allocated 192.175.48.0/24 and IANA reserved 192.175.48.0/24. Resolved. Removed reserved block from ARIN.
Network block overlap: APNIC reserved 198.51.100.0/24 and IANA reserved 198.51.100.0/24. Resolved. Removed reserved block from APNIC.
Network block overlap: APNIC reserved 203.0.113.0/24 and IANA reserved 203.0.113.0/24. Resolved. Removed reserved block from APNIC.
Timestamps of resources:
- Skip to primary navigation
- Skip to main content
- Skip to primary sidebar
- Skip to custom navigation
- Infoblox Threat Intel
- BloxOne® Applications
Infoblox Community
- Partner Portal

Why Infoblox
Market Leadership

Networking Products Core network services including DNS, DHCP and IPAM (DDI)
Security Products Foundational security for anywhere protection
Automation Products Tools to streamline modern networking and security
BloxOne ® DDI Simplify networking with automated, cloud-managed DNS, DHCP and IPAM
Data Center | Cloud
NIOS DDI Unify DNS, DHCP and IPAM for complex, on-premise networking

BloxOne ® Threat Defense Quickly deploy hybrid DNS-layer security everywhere
Threat Intelligence Leverage better DNS and multi-sourced threat intel to improve your total security stack
Advanced DNS Protection Protect enterprise DNS infrastructure to ensure maximum uptime
Cybersecurity Ecosystem Automate SecOps response and efficiency with advanced integrations
Cloud Network Automation Centrally manage core network services and security
Unified Network View Enhance security and efficiency with Network Insight
Global Load Balancing Optimize application performance
Reporting and Analytics Easily analyze your network and automate compliance
IP Address Management for Microsoft Plug the gaps and extend your investment in Microsoft IPAM
Network Automation and Compliance Simplify and streamline multi-vendor network management with NetMRI
Initiative Solutions for key challenges
Technology Key tools and integrations
Industry Vertical market solutions
Job Function Solutions overview by role
Multi-Cloud Networking Transform hybrid, multi-cloud management of critical network services such as DNS and IPAM
SaaS-Enabled Enterprise Secure cloud-managed, cloud-native network services for distributed enterprises
On-Premises + Cloud-Managed Networking Uniting enterprise grade and cloud native core networking services for the hybrid enterprise
Hybrid Workplace Speed your transition to a secure, multi-cloud organization to support your hybrid workforce
Cybersecurity Frameworks Satisfy requirements for leading security best practices
Secure Edge Services Deliver new cloud-managed networking and security services anywhere
IT Compliance Simplify management of regulatory compliance requirements

Technology Optimization
Accelerate Office 365 performance Ensure fast, reliable user experiences
Secure IoT Protect devices across IoT environments
Deploy IPv6 Set your network foundation up for success
Optimize SD-WAN Use cloud-managed DNS, DHCP and IPAM for better ROI
Support Encrypted DNS Offer DoT/DoH services while maintaining security and performance
Key Integrations
Networking Easily integrate, orchestrate and automate with top networking providers and tools
Security Make your entire security stack more effective with rich APIs and integrations
Healthcare Simplify, control and secure vital healthcare services
Higher Education Improve network performance while reducing costs
Public Sector Scale and secure distributed networking for all
- Public Health & Human Services
- State & Local
Service Providers Deliver modern core network services and security
- Mobile Providers
- Cable and Broadband
- Managed Service Providers
- Subscriber Services
NetOps Unify DNS, DHCP and IPAM and simplify complex networking
DevOps Use automation and advanced integrations to streamline operations
SecOps Leverage automation and multi-source intelligence to stop threats faster
CIO/CISO Optimize your workforce productivity with a SaaS-enabled enterprise

Support Overview
Customer Support Portal
Technical Account Manager
COVID-19 Support Update
Customer Success
Customer Success Management
Professional Services
Education Services
Cloud Services
Cloud Services Portal (CSP)
Cloud Services Status
Developer Portal
Analyst Reports
Customer Case Studies
Deployment Guides
Evaluations
Live Events & Webinars
Infographics
Solution Notes
On-demand Webinars
Whitepapers

About Infoblox
Diversity & Inclusion
Environmental, Social, and Governance Policy
About Infoblox Partners
Technology Alliance Partners
- Infoblox for Microsoft
- Infoblox for AWS
Managed Services Partners
News and Events
Company Blog
In the News
Press Releases
Home / IPv6 CoE / IPv6 Prefix Allocation Methods – Part One (of Two)
IPv6 Prefix Allocation Methods – Part One (of Two)
December 6, 2019
Introduction
So, let’s suppose that you’ve been allocated a block of IPv6 addresses. If it’s your primary allocation, I’m hopeful that you’ve both encountered and taken to heart one critical address planning principle. This principle recommends that your primary allocation be sufficiently large enough to meet your addressing needs for the next several decades – say, 20-50 years. And chances are, that timeframe exceeds the likely lifespan of the Internet Protocol. (If you haven’t yet obtained an IPv6 allocation you can learn more about how to do so from ARIN’s website .)
This blog deals with the most familiar methods available for assigning subsets of address space from that primary allocation. And of course the same methods will continue to work when assigning space from within those subsets of assigned space as well (wheels within wheels!). These methods will work for any IPv6 allocation size (though as we will see as we explore the different allocation methods, some of them make more sense to use with larger allocations and some with smaller).
You’re likely already familiar with this process of assigning address blocks from your work with IPv4. But chances are due to the natural constraints on the availability of IPv4 address space, you may not be as familiar with a couple of the more commonly used address assignment methods the abundance of IPv6 address space allows for.
Four Common IPv6 Assignment Methods
Let’s begin with defining four common IPv6 prefix assignment methods. They are:
- Next available
To demonstrate how each of these methods works, I’m going to pick different allocation sizes. These sizes range from a /64 up to and including our primary allocation (the one we would get from a Regional Internet Registry or ISP to meet all of the IPv6 addressing needs for our entire network). If we’ve been paying attention to proper IPv6 address planning principles, we might hope that our overall primary allocation has a couple of beneficial characteristics. I’ve already mentioned that our primary allocation needs to be sufficiently large to accommodate the growth of our network more or less indefinitely.
Another beneficial characteristic would be that our primary allocation falls on a nibble boundary . It should probably also go without saying that such an allocation won’t be smaller than the smallest legally assignable prefix in IPv6 of a /64 nor larger than the largest allocation we’re likely to receive from a Regional Internet Registry. This largest size might vary but from personal experience wouldn’t likely be greater than an IPv6 /24.
Somewhere in between these largest and smallest allocations lies the /48, which we should recognize as significant for being both the recommended baseline size for a particular site within our network as well as for being the smallest Internet-routable prefix size . In my book, IPv6 Address Planning , I make a distinction between something I rather blandly referred to as inter-site vs. intra-site planning and this, in the briefest of nutshells, is the distinction between handing out address blocks from our primary allocation (something larger than a /48 if our network has more than one site – and nearly all networks requiring the architecture, engineering, and administration that keep us employed typically do) and handing out address blocks from within a single /48.
While any of our address allocation methods would theoretically work for either intra-site or inter-site planning, we’ll soon see which particular methods are more commonly used for each type of planning.
With all that in mind, let’s return to defining the first of our most common IPv6 address assignment methods.
Next Available
This method is alternatively referred to as sequential or monotonic. It’s best demonstrated by beginning with an allocation that is subsequently divided into smaller prefixes of identical size. For the purposes of making our example practical, we’ll start with the smallest nibble-boundary-aligned prefix that doesn’t directly go on an interface – which would be (and here we pause for an exercise briefly left to the reader)…
….that’s right, a /60! Hopefully, you’ve gotten familiar enough with your nibble math at this point that you recognize that a /60 provides you with…
…again correct, 16 /64s for interface assignment!
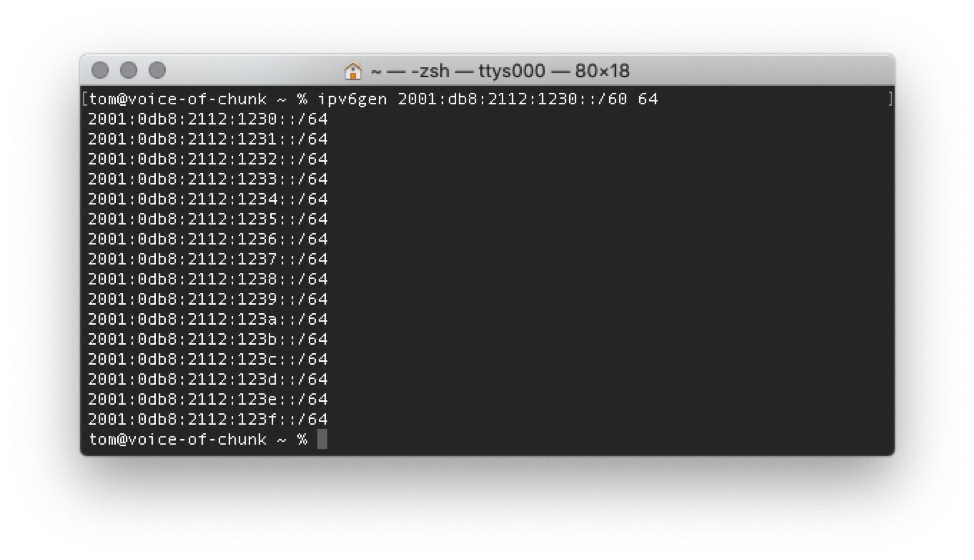
You may have noticed from the example above; this method doesn’t presume any particular order or organization of the elements needing a prefix assignment. It simply dictates that whatever element needs a prefix of a particular size (in this case, a /64) from a particular larger allocation (in this case, a /60) gets the next available prefix from the list of available prefixes.
Note that if I were actually numbering VLANs, I might wish to use a scheme that aligns the VLAN number to the prefix being assigned. If my network configuration uses extended VLANs at least 4094 unique /64 prefixes I would be need to map them all to specific VLANs. This would require at least a /52, which in turn would provide 4096 /64s.
Obviously, with this method it helps if you can easily convert hexadecimal to decimal, something which may pose challenges to your operations teams. Alternatively, by using a /48, no hexadecimal to decimal conversion would be necessary. For example:
A caveat with this approach is that one is consuming only 6% of the /48 for that particular application. Of course, we could use the remaining prefixes in an ad-hoc fashion (especially where IPAM can help keep track of them). Even if we don’t assign any prefixes beyond the 6% for extended VLANs, there is no requirement to avoid this method to conserve IPv6 address space.
For this example, I picked on one of the smallest prefixes allowing for subsequent, more granular subnet assignments (i.e., /60 -> /64), but of course this method works just as well with larger prefix allocations. For example, a RIR might assign a /44 to a small enterprise with 12 or fewer sites.
Another way to visualize this and other allocation methods is by using a pie chart:
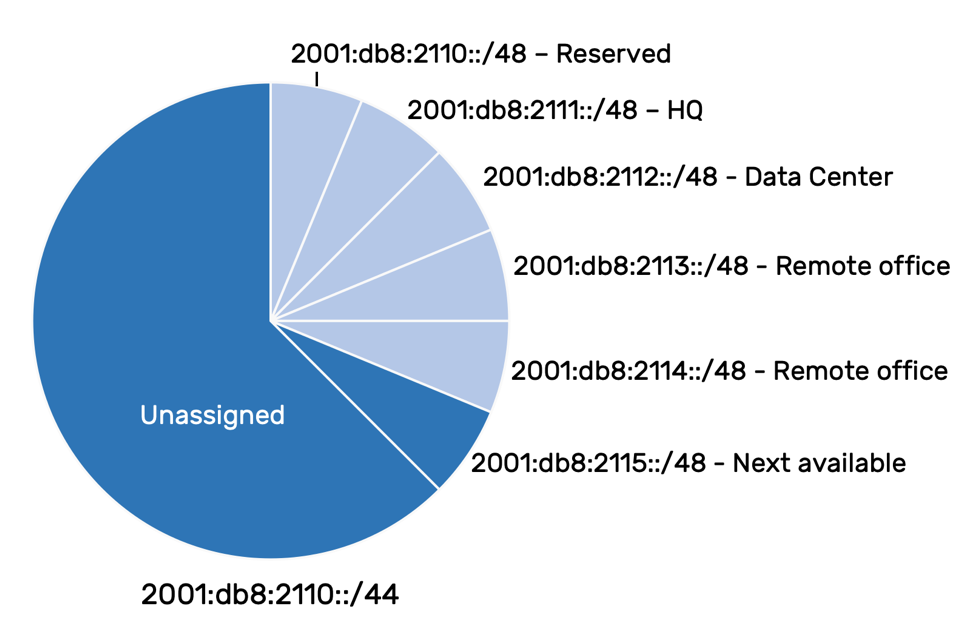
Reserving Zero Prefixes
Incidentally, you probably noticed that in the above allocation examples, I didn’t use the first available prefix for an actual assignment but instead marked it as reserved . There are two beneficial reasons for this. The first is that it avoids potential confusion between two prefixes that share the exact same label but differ in size. For example, in standard zero compressed format:
Without referencing the CIDR notation, I can’t immediately determine whether I’m looking at the entire block (i.e., 2001:db8:2110::/44) or merely the second available prefix from it (i.e., 2001:db8:2110::/48). We network engineering types naturally pride ourselves on our precision and accuracy. But we’ve also likely got the operational battle scars from middle-of-the-night outages. Those outages where, in spite of our best precision-and-accuracy intentions, we misread one prefix for another. By not using the first subnet from each larger block, we can entirely avoid any such confusion.
The second beneficial reason to reserve the first available prefix is a bit more direct. When labeling things, it’s convention to start enumerating them from “1”. By not using the first available prefix from the larger allocation (which will always end in “0”), we’ll always start assigning prefixes beginning with “1”.
That’s it for part one! Next time we’ll cover the remaining IPv6 prefix allocation methods sparse , best fit , and random .
Thanks for reading!
Tom Coffeen (@ipv6tom) is a co-founder of HexaBuild , an IPv6 consulting and IPv6 training company. Tom is the author of IPv6 Address Planning on O’Reilly Media. You can follow HexaBuild on Twitter and LinkedIn .
- IPv6 address planning

Tom Coffeen
Co-founder of hexabuild.io.
Tom Coffeen is a network engineer, architect, and author with over twenty years of internetwork design, deployment, administration, and management experience. Tom co-founded HexaBuild, an IT consultancy specializing in the advancement of cloud, IoT, and security deployment best practices through IPv6 adoption. Prior to co-founding HexaBuild, Tom was an IPv6 Evangelist and a Distinguished Architect at Infoblox. Before that Tom was the VP of network architecture at the global CDN Limelight Networks where he led their deployment of IPv6. He is also the author of O’Reilly Media’s IPv6 Address Planning.
You might also be interested in

The IPv6 Prefix Information Option or Fun with the L Flag
By Ed Horley

The Odd History of Provisioning an IPv6 Address on a Host

Back to Basics – The IPv6 Address Types – part 3
Back to Basics – The IPv6 Address Types – part 2
Back to Basics – The IPv6 Address Types

IPv6 Prefix Allocation Methods - Part Two
By Tom Coffeen

IPv6 Projects and “The Human Element”
By Steve Rogers

Call us today
1.800.856.5960, exploring ip address blocks by country: a comprehensive guide.
- No Comments

- Your Address
Database Dump
You can download individual csv files or the entire database. These downloads are huge, please be patient. The smallest file is the JSON download because it only contains the bare minimum.
IP Version 4
Ip version 6.
We do provide full lists in different formats
This is a structured list in JSON format for easy processing in most programming languages.
This list is formatted in a way that most peer to peer applications want.
Red Hat OpenShift 101 for OpenStack admins: Configuration

In the previous post , we oversaw the required Red Hat OpenShift Container Platform operators , their roles, and the format used to create the Red Hat OpenStack Services on OpenShift (RHOSO) control plane. In this article, let’s review the deployment process.
We’ll base our observations on the Development Preview 3 code from https://github.com/rh-osp-demo/dp-demo/ .
Let’s begin with the OpenStack Operator.
The OpenStack Operator
The OpenStack Operator consists of three parts (a CatalogSource , an OperatorGroup , and a Subscription ), each defining a different resource for managing Operators within an OpenShift/ Kubernetes cluster using the Operator Lifecycle Manager (OLM). The resources aim to set up an Operator for OpenStack, likely for managing OpenStack services within the cluster, are as follows:
These resources collectively set up an environment where the OpenStack Operator is available to be installed in the openstack-operators namespace. The CatalogSource provides the metadata about available operators, including the OpenStack Operator, sourced from a specified image. The OperatorGroup defines the scope within which the Operator can operate, and the Subscription triggers the installation and management of the OpenStack Operator according to the specified channel and source catalog.
Let’s focus on the CatalogSource part:
- name: openstack-operator-index - The name of the CatalogSource .
- namespace: openstack-operators - The namespace where the CatalogSource is created.
- sourceType: grpc - Indicates that the catalog source uses gRPC to serve the index of available operators.
- secrets: A list of secrets, in this case, osp-operators-secret , that might be used by the catalog source, potentially for accessing private repositories.
- gprcPodConfig : Contains configuration specific to the pod serving the gRPC requests.
- securityContextConfig: legacy - Specifies a security context configuration for the pod. The exact meaning of "legacy" can depend on the cluster configuration.
- image : The container image URL for the operator index image, which should be adjusted to match the environment. This image hosts metadata about the operators available for installation, including the OpenStack operator.
Network isolation
Now that the operator is installed, let’s prepare the networking for the control plane, then the data plane.
First, we’ll work with the NNCP file used to configure the data plane network, which will configure the topology for each data plane network. It looks like the following ( source file ):
This YAML file defines a NodeNetworkConfigurationPolicy for use with the NMState Operator in an OpenShift or Kubernetes environment. The policy specifies desired network configurations for nodes that match the defined nodeSelector. Here's a breakdown of the key components:
- apiVersion : Specifies the version of the NMState API used.
- kind : Identifies the resource type as NodeNetworkConfigurationPolicy , indicating that it's a policy for configuring network interfaces on nodes.
- name : The name of the policy, osp-enp1s0-worker-ocp4-worker1 , uniquely identifies it within the namespace.
- The first three are VLAN interfaces (type: vlan ) with the names enp1s0.20 , enp1s0.21 , and enp1s0.22 . Each interface is configured with a static IPv4 address ( 172.17.0.10/24 , 172.18.0.10/24 , 172.19.0.10/24 , respectively) and specifies that IPv6 is disabled. DHCP is also disabled for IPv4, and each interface is brought to the up state. They are all based on the parent interface enp1s0 and have VLAN IDs 20, 21, and 22, respectively.
- The fourth interface configuration applies to enp1s0 itself, setting it as an Ethernet interface (type: ethernet ) with a static IPv4 address 172.22.0.10/24 , DHCP disabled, and IPv6 disabled. The interface is also set to the up state with an MTU of 1500.
- nodeSelector : Specifies a node's criteria for the policy to be applied. In this case, it selects a node with the hostname ocp4-worker1.aio.example.com with a worker role.
This policy aims to configure multiple VLANs on a specific worker node's enp1s0 interface in an OpenShift or Kubernetes cluster, assigning static IPv4 addresses to each VLAN and the parent interface. It effectively segregates network traffic into different VLANs for purposes such as separating internal API traffic, storage traffic, and tenant traffic, while also configuring the parent interface for another network segment. The policy targets a specific node identified by its hostname and role, ensuring that these configurations are only applied to the intended node.
NetworkAttachDefinition (NAD) file
This YAML snippet defines a NetworkAttachmentDefinition object, part of the Kubernetes Network Custom Resource Definition (CRD) framework enabled by the Multus CNI plugin. This CRD is used to create multiple network interfaces in a Kubernetes pod. We will configure a NAD resource for each isolated network to attach a service pod to the network:
Let’s look at it:
- apiVersion: k8s.cni.cncf.io/v1 : Specifies the API version for the CRD. The k8s.cni.cncf.io/v1 indicates it's related to the CNI (Container Network Interface) plug-ins managed under the CNCF (Cloud Native Computing Foundation).
- kind: NetworkAttachmentDefinition : This tells Kubernetes that the defined resource is a NetworkAttachmentDefinition , which Multus uses to understand how to attach secondary networks to pods.
- name: ctlplane : The name of the NetworkAttachmentDefinition , which will be referenced by pods that want to use this network configuration.
- namespace: openstack : Specifies the namespace where this NetworkAttachmentDefinition is created, indicating it's intended for use by pods running in the openstack namespace.
- cniVersion : The version of the CNI specification to use.
- name : A name for this specific network configuration.
- type : Specifies the CNI plug-in to use, in this case, macvlan, which allows a Kubernetes pod to have a unique MAC address via a parent host interface.
- master : The master interface on the host that the macvlan interface will be created on top of. Here, it's ens224.4 , indicating a VLAN interface.
- type : The type of IPAM plugin to use, here whereabouts, which supports assigning IP addresses across multiple host nodes, avoiding IP address conflicts.
- range : The CIDR range from which IP addresses will be allocated.
- range_start , range_end: Define the start and end of the IP allocation pool within the specified range.
NMState resources
As described earlier, we must define IP address pools and L2 advertisements for the NMstate Operator. We must create an IPAddressPool resource to specify the range of IP addresses MetalLB can assign to services. Let’s have a look at our osp-ng-metal-lb-ip-address-pool . It contains several entries, one per IP address pool we define. Let’s just pick one to detail, the ctlplane one:
What do we have:
- apiVersion: metallb.io/v1beta1 : Specifies the API version of MetalLB being used.
- kind: IPAddressPool : Denotes the kind of Kubernetes resource. Here, IPAddressPool is a resource type provided by MetalLB for defining a pool of IP addresses.
- namespace: metallb-system : Specifies the namespace where the resource is located. MetalLB's resources typically reside in a dedicated namespace, metallb-system , isolated from other workloads.
- name: ctlplane : The name of the IPAddressPool resource. This name is used to identify the pool within the MetalLB configuration.
- addresses : Lists the IP address ranges that MetalLB can allocate to LoadBalancer services.
- - 172.22.0.80-172.22.0.90 : Defines a specific range of IP addresses (from 172.22.0.80 to 172.22.0.90 ) that MetalLB is allowed to assign. This range should be within the network subnet accessible by the cluster and not used by other devices or services to avoid IP conflicts.
As we are using MetalLB in Layer 2 mode, define an L2Advertisement resource. This tells MetalLB to advertise the IP addresses from your network's specified pool(s).
Let’s have a look at our osp-ng-metal-lb-l2-advertisement YAML file. It contains several entries, let’s just pick the one relevant to ctlplane :
Here's a succinct explanation of its contents:
- apiVersion: metallb.io/v1beta1 : Specifies the version of the MetalLB API being used.
- kind: L2Advertisement : Indicates the resource type, an L2Advertisement . This type controls how MetalLB advertises IP addresses to the local network.
- name: ctlplane : The name of the L2Advertisement resource.
- namespace: metallb-system : The namespace where the resource is deployed, typically MetalLB's dedicated namespace.
- ipAddressPools : Lists the names of the IP address pools that MetalLB should advertise. In this case, it references the IPAddressPool ctlplane , which we defined earlier.
- interfaces : Specifies which network interfaces MetalLB should use to advertise IP addresses. Here, it's configured to use the interface named enp1s0 .
This file tells MetalLB to advertise IP addresses from the ctlplane IP address pool over the enp1s0 network interface, making these IP addresses reachable on the local network through standard L2 networking mechanisms (ARP for IPv4, NDP for IPv6).
Let’s regroup what we have seen so far before we keep deploying our OpenStack Control Plane. When deploying MetalLB, you first apply the MetalLB resource to install MetalLB itself. Then, you define one or more IPAddressPool resources to specify the range of IPs MetalLB can manage. Finally, you use L2Advertisement resources to control the advertisement of these IPs on your network in Layer 2 mode.
MetalLB and NAD ( NetworkAttachmentDefinition ) serve different purposes. MetalLB is used to expose Kubernetes services of type LoadBalancer externally, allowing them to be accessible from outside the Kubernetes cluster. It's particularly useful in bare-metal environments where you don't have a cloud provider to provision external load balancers automatically.
NAD with Multus allows for attaching additional network interfaces to pods. This is useful in scenarios where pods need to communicate over different networks or require specific network configurations that the default Kubernetes network doesn't provide.
In essence, MetalLB simplifies external access to services, while Multus and NAD enhance pod networking capabilities within the cluster.
Data plane network configuration
The data plane network configuration file will configure the topology for each data plane network. Its YAML file contains a NetConfig header and then various network sub-sections, each defining a network to expose to the data plane network.
Here is an extract of this sample configuration file:
The YAML snippet defines a custom resource named NetConfig under the API group network.openstack.org/v1beta1 . This is not a standard Kubernetes API group, which implies it's part of a specific operator that extends OpenShift functionality related to integrating OpenStack networking capabilities with Kubernetes.
Here's a breakdown of what this YAML does:
- apiVersion: network.openstack.org/v1beta1 : Specifies the version of the API that the resource definition is compatible with. This is a custom resource definition (CRD) related to OpenStack networking under the v1beta1 version.
- kind: NetConfig : This indicates the type of the resource. The resource is used to configure how networking should be set up within for OpenStack-managed resources within Kubernetes.
- name: openstacknetconfig : The name of the NetConfig resource.
- namespace: openstack : This resource is in the openstack namespace.
- name: ctlPlane : Specifies the name of the network. It refers to a control plane network used for management and orchestration traffic in OpenStack.
- dnsDomain: ctlplane.aio.example.com : Defines the DNS domain used for the network.
- name: subnet1 : The name of the subnet.
- From 172.22.0.100 to 172.22.0.120
- From 172.22.0.150 to 172.22.0.200
- cidr: 172.22.0.0/24 : Typically, the CIDR should match the network of the allocation ranges and the gateway.
- gateway: 172.22.0.1 : Specifies the gateway for the subnet, which is the IP address used as the default route for traffic leaving the subnet.
From the internalaip section, we also see we can define VLAN IDs and exclusion ranges:
- excludeAddresses: IP range that the data plane should not use (these are the IP addresses used by the OCP cluster compute nodes (check the NNCP section above).
- vlan: VLAN ID used by the internalapi network. The lack of this entry in the ctlplane section denotes using a flat network.
OpenStack Control Plane deployment
Now that we have all of our networking defined, and provided we have our storage configured (the sample file we use relies on NFS, but we did not discuss it here), we can deploy the control plane.
The control plane deployment YAML defines the different OpenStack services that should be instantiated, and for each service its configuration. The file is quite long, so copying it here is difficult, but you can check a sample file here .
Here is, from the above sample, the list of defined Services and Key Configurations (note that some services are disabled):
- Utilizes MetalLB for LoadBalancer with an IP of 172.22.0.89.
- Configured to use an external DNS server at 192.168.123.100.
- Database instance named openstack , using a secret osp-secret .
- Cinder API exposed via MetalLB with an IP of 172.17.0.80.
- NFS backend for Cinder Volumes with specific NFS configurations.
- Storage backend set to use Cinder with specific Glance and Cinder configurations.
- Glance API exposed via MetalLB with an IP of 172.17.0.80.
- Uses NFS for storage with a request of 10G.
- Exposed via MetalLB with an IP of 172.17.0.80.
- Uses a database instance named openstack and a secret osp-secret .
- Enabled with storage requests set for the database and cell instances.
- Uses a secret osp-secret .
- Deployed with a single replica.
- Deployed with a single replica, using a secret osp-secret .
- API and Metadata services exposed via MetalLB with an IP of 172.17.0.80.
- API exposed via MetalLB with an IP of 172.17.0.80.
- Configuration for northbound and southbound DBs, as well as the OVN Controller.
- Exposed via MetalLB with specific IPs for RabbitMQ services.
- API and Engine exposed via MetalLB with an IP of 172.17.0.80.
- Disabled in this configuration.
- Ceilometer enabled, with configurations for autoscaling and metric storage.
In summary, MetalLB is extensively used to expose various OpenStack services externally via LoadBalancer type services, with annotations specifying address pools and IPs. Storage utilizes both Cinder (block storage) and NFS, with specific service configurations detailed for different services.
Each service utilizes a specific database instance and secrets for configuration and credentials management. Replicas and scaling define the number of replicas for certain services, indicating considerations for availability and scaling. And, finally, several services specify network attachments, indicating integration with specific network configurations for service communication.
We’ll complete the deployment process in the final part of this series: Red Hat OpenShift 101 for OpenStack admins: Data plane deployment
- Red Hat Enterprise Linux
- Red Hat OpenShift
- Red Hat Ansible Automation Platform
- See all products
- See all technologies
- Developer Sandbox
- Developer Tools
- Interactive Tutorials
- API Catalog
- Operators Marketplace
- Learning Resources
- Cheat Sheets
Communicate
- Contact sales
- Find a partner
Report a website issue
- Site Status Dashboard
- Report a security problem
RED HAT DEVELOPER
Build here. Go anywhere.
We serve the builders. The problem solvers who create careers with code.
Join us if you’re a developer, software engineer, web designer, front-end designer, UX designer, computer scientist, architect, tester, product manager, project manager or team lead.
Red Hat legal and privacy links
- About Red Hat
- Contact Red Hat
- Red Hat Blog
- Diversity, equity, and inclusion
- Cool Stuff Store
- Red Hat Summit
- Privacy statement
- Terms of use
- All policies and guidelines
- Digital accessibility

IMAGES
VIDEO
COMMENTS
APNIC IPv6 Allocations Allocations of IPv6 address space are made to regional Internet registries according to their needs, based on allocation rates they publish. Specifically, RIRs are eligible for further allocations if their available space of existing allocations is less than 50% of a /12 address block, or less than their necessary space ...
Find a complete list of IP addresses by country with IP Geolocation Statistics. This page shows statistical analyses done on all IP addresses in use today. You are in the right place if you want to know how IPs are distributed across countries, Internet service providers (ISPs), and geographical locations. 17,394,455 248 216,855 2,961 41,007 ...
IPv6 Capable Rate by country (%) Click here for a zoomable map Remember current choice for 7 days. 30 day average (17/04/2024 - 16/05/2024) Plot Type: Date: Window (Days) Colour Range (max value - "Auto" is auto scaling) IPv6 Capable Rate by country (%) Click here for a zoomable map ...
Table 16 — IPv6 address allocation volumes by RIR. Dividing addresses by allocations gives the average IPv6 allocation size in each region (Table 17). Overall, the average IPv6 allocation size is a /28, with the RIPE NCC and ARIN averaging larger individual IPv6 allocations than the other RIRs.
The IANA performs the first allocation, distributing IP addresses to Regional Internet Registries (RIRs) in five broad regions (which roughly correspond to the continents. ... The % column indicates the percentage of the total global number of IPv4 addresses each country has been allocated. IPv6 addresses are allocated in ""/32"" blocks which ...
IPv6 Allocation Excluding Reserved Addresses. Finally, to put things into size perspective, all the IPv4 address space is 2^32 = 4,294,967,296 IP addresses. Every IPv6 RIR has been assigned more than a /12. A single /12 has 2^52 = 4,503,599,627,370,496 /64s! Each /64 contains 2^64 IP addresses. Comparing 2^32 and 2^52 visual is meaningless, the ...
Even if we use only the country code (CC) entry in the RIR's registry records, then we get a variety of meanings. ... Table 19 — IPv6 address allocation volumes by year, by economy (/32s). We can also look at the allocated address pools for the 25 economies with the largest allocated address pools in IPv6, and the current picture is shown ...
The IPv6Matrix is a tool to gather and visualise data on IPv6 (Internet Protocol v6) deployment and accessibility from the top one million domain names around the world, since 2010. More about the IPv6Matrix » The globe displays every countries' overall IPv6 adoption over time. - Drag the globe to rotate. - Drag the red slider to control the date.
NOTE: This data is generated by using the ISO 3166 economy code information provided in the allocation and assignment statistics reports as generated by the Regional Internet Registries.This code reflects the economy in which the entity to whom the allocation or assignment was made is located, but does not necessarily reflect the scope of use of deployment of the associated resource.
There are 249 countries listed below, and each link will bring you to a new page containing the respective IP address ranges. If you are interested to learn more about the ranking of IP addresses allocated for each country, please visit IP Address Reports for details. Afghanistan. Aland Islands. Albania.
IP Address Allocation by Country. ... For information on the sources behind the data, please see the project repository on github. IPv4. Rank Country IP Addresses % Population IP Addresses Per Capita; Total World Allocation: 3685851960: 100: 7614975601: ... IPv6. Rank Country IP Addresses % Population; Total World Allocation:
IPv6 addresses are assigned to organizations in much larger blocks as compared to IPv4 address assignments—the recommended allocation is a / 48 block which contains 2 80 addresses, being 2 48 or about 2.8 × 10 14 times larger than the entire IPv4 address space of 2 32 addresses and about 7.2 × 10 16 times larger than the / 8 blocks of IPv4 ...
This document describes policies for the allocation and assignment of globally unique Internet Protocol version 6 (IPv6) address space. [ RFC 4291] designates 2000::/3 to be global unicast address space that the Internet Assigned Numbers Authority (IANA) may allocate to the RIRs. In accordance with [ RFC 4291 ], IANA allocated initial ranges of ...
IPv6 Adoption Evolving Global IP Allocation. Upgrading networks to IPv6 evolves IP allocation dynamics. IPv6's enhanced capacities allow larger address assignments to adopting countries. The projected 5 billion new internet users coming online, mostly via IPv6, may disrupt the global balance as developing world IP ranges grow.
1 Introduction. IP address planning is certainly among the critical functions required within the overall process of planning and executing an IPv6 deployment project. After all, one needs IPv6 address space in order to implement IPv6 and current IPv4 space must be managed in conjunction with the addition of IPv6 space.
IPv6 Prefix Allocation Methods - Part One (of Two) December 6, 2019. Introduction. So, let's suppose that you've been allocated a block of IPv6 addresses. If it's your primary allocation, I'm hopeful that you've both encountered and taken to heart one critical address planning principle. This principle recommends that your primary ...
The length of an IPv6 prefix may be any number from zero to 128, although subnets using stateless address autoconfiguration (SLAAC) for address allocation conventionally use a /64 prefix. Hardware and software implementations of routing and forwarding should therefore impose no rules on prefix length, but implement longest-match-first on ...
IP address allocation to countries is managed by regional internet registries (RIRs), which oversee the distribution of IP address blocks within their respective regions. ... Additionally, emerging technologies such as IPv6 adoption and the Internet of Things (IoT) will introduce new challenges and opportunities in IP address management and ...
The deployment of IPv6, the latest version of the Internet Protocol (IP), has been in progress since the mid-2000s. IPv6 was designed as the successor protocol for IPv4 with an expanded addressing space. IPv4, which has been in use since 1982, is in the final stages of exhausting its unallocated address space, but still carries most Internet traffic.. By 2011, all major operating systems in ...
Even if we use only the country code entry in the RIR's registry records, then we get a variety of meanings. ... Table 19 — IPv6 address allocation volumes by year and economy (/32s). We can also look at the allocated address pools for the 25 national economies with the largest allocated address pools in IPv6, and the current picture is ...
Internet Protocol version 6 (IPv6) is the most recent version of the Internet Protocol (IP), the communications protocol that provides an identification and location system for computers on networks and routes traffic across the Internet.IPv6 was developed by the Internet Engineering Task Force (IETF) to deal with the long-anticipated problem of IPv4 address exhaustion, and was intended to ...
Country IP Database. List of IPv4 Addresses by Country. 250006 ranges available in 244 countries. Last update: 2024-04-07 11:39:34 GMT IPv6 is available in the "Database Dump" tab
On a Windows system, type the following: ping -6 <IPv6-address>. To check the network path to a remote system on Linux and macOS, type either of the following: $ traceroute6 <IPv6-address>. $ traceroute -6 <IPv6-address>. Windows administrators can use the tracert command to trace IPv6 address routes, as seen here:
allocationRanges: Specifies ranges within the subnet from which IP addresses can be allocated. Lists two ranges of IP addresses for allocation: From 172.22..100 to 172.22..120; From 172.22..150 to 172.22..200; cidr: 172.22../24: Typically, the CIDR should match the network of the allocation ranges and the gateway.