Manual Network Configuration in Linux and How to Set a Static IP Address
Last updated: March 18, 2024
- Administration

1. Introduction
Many Linux distributions come with a network manager. In theory, it should help during the networking setup. Yet, we might not always want to install or use managers when setting up an interface. Moreover, a network manager is often just a convenient abstraction or interface to the configuration files of a Linux distribution.
In this tutorial, we look at standard low-level files and tools to configure our IP address settings . We start off by briefly discussing dynamic and static addresses. After picking static IP network configuration as an example, we look at a universal way to perform it under Linux. Next, we explore network managers in detail. Finally, we show our main example in action on multiple Linux distributions.
For brevity, we only use IPv4 instead of IPv6 and static instead of dynamic addresses, but most concepts apply to all variants.
We tested the code in this tutorial on Debian 12 (Bookworm), CentOS Stream 9, Slackware 15.0, Gentoo 2.8, and ArchLinux Rolling (2022.10.01). It should work in most POSIX-compliant environments.
2. Dynamic and Static IP Address
When using a static IP, the operating system (OS) knows that we have two requirements for a given interface:
- a specific IP address
- full control over the address assignment
Since the Dynamic Host Configuration Protocol (DHCP) can take the Media Access Control (MAC) address into account when assigning the network-layer address, we might still automatically receive the same IP on each connection with that protocol. Moreover, the client can usually specify a preference.
However, whether we get the same IP address with DHCP might depend on many factors, some of which are external :
- DHCP server IP reservation
- same DHCP server
- unchanged DHCP server configuration
- same network interface card (NIC) or MAC address
Thus, we give up control of our network-layer address, which may become inconvenient when it’s our sole means to identify a system. For example, switching environments can lead to a new IP. If we don’t have remotely-resolvable hostnames or domain names, we’d need this new IP when using access protocols like SSH. Further, a name (type) on one network could be unrecognizable on another.
On the other hand, a static IP ensures we always assign the same address . Of course, this comes with its own problems:
- manual settings might not comply with a given environment
- might have to change configuration depending on the network
- can lead to IP address conflicts, especially on smaller networks
Still, for stationary machines and the proper administration, a static address is usually more of a convenience than a burden . So, we use that as our example configuration.
3. Static IP on Linux
While there are many managers, graphical user interface (GUI) front-ends, and command-line interface (CLI) utilities for network settings, many boil down to the ip command, which supersedes ifconfig .
Let’s use ip to acquire and set our NIC configuration.
3.1. Current Settings
First, we check our current setup:
Here, we have an IPv4 ( inet ) address of 192.168.6.2 with its associated 192.168.6.255 broadcast and several specifiers. Of the latter, dynamic means the system uses DHCP to set up the connection . Let’s confirm this:
Above, we use grep to case-insensitively filter for dhcp in the system log from the last boot as returned by journalctl . Consequently, we see the setup of our eth1 interface with the address 192.168.6.2 .
3.2. Consider DHCP
In most recent Linux distributions, disabling DHCP comes down to controlling a daemon for the server ( dhcpd ) or client ( dhcpcd ):
However, there are several pitfalls:
- we might not need to disable DHCP at all if it’s properly configured
- the daemon name and control mechanisms can vary
- on older systems, DHCP client calls can instead be in other services
- custom solutions can provide and force DHCP depending on the Linux distribution
Because of this, how and whether we turn DHCP off depends on the system and our needs.
3.3. Temporary Static IP via ip
Now, let’s use ip to set a static IP on eth1 :
After flushing all addresses and routes from eth1 , we add a new static address and gateway. Next, we verify the settings by confirming that dynamic is no longer present in the interface characteristics. However, a system reboot now would wipe our network setup and restore the IP to what DHCP provides .
3.4. Permanent Static IP via ip
To make the settings we applied remain the same between reboots, we can run a script on startup, which includes the ip lines above, along with any other related commands. Naturally, the exact way depends on the Linux distribution.
4. Network Managers
Using a manager can be critical for complex setups. Yet, even a one-interface machine can benefit from the features network managers provide:
- seamlessly detect networks
- automatically configure connections
- maintain and switch between configuration profiles
- support multiple protocols, wireless and wired
Critically, network managers are feature-rich abstractions to the network configuration files of a given system . While there are many Linux network managers like Connman , netctl , and wicd , three are ubiquitous:
- System V (SysV) network(ing) services
- systemd ‘s systemd-networkd
- NetworkManager
Since most Linux distributions migrated to systemd , the first of these is now mostly deprecated, although still widely supported. Importantly, SysV network(ing) service configuration files provide the original framework commonly used by other network management solutions .
4.1. Identify Network Managers
Before doing any network configuration on a Linux system, we should identify and disable unused network managers. Thus, it’s usually a good idea to start by checking for any related services:
In this case, we use grep to search for the keyword network in the list of services. While not foolproof, this is a good first step. Consequently, we see NetworkManager is active and running .
4.2. Control Network Managers
We can simply use systemctl to detect and toggle most service-based network managers. For example, we can easily replace one manager with another where available:
Notably, the *-wait-online and other secondary daemons that each solution offers are also part of the packages. While the enable and disable lines are optional, running conflicting services or configurations of any kind is considered bad practice and can lead to severe issues and system instability , especially regarding networking.
Of course, with services of this kind, any setup should be easier to configure and maintain. Adding to that, most managers have a GUI, terminal user interface (TUI), or at least a flexible CLI. Unlike ip , settings from network management tools can persist between reboots.
Now, we move to the most persistent, albeit in part, distribution-specific solutions.
5. Static IP on Debian Distributions
Let’s check the default structure of networking configuration files in Debian derivatives such as Kali , Knoppix , Ubuntu , Raspberry Pi OS , and Tails :
Here, the tree command shows the /etc/network/*.d directories for scripts that run before ( pre ), after ( post ), or while an interface ( if ) goes up or down . Next to them, the /etc/network/interfaces file contains the main network interface configuration, sourcing any files in the /etc/network/interfaces.d .
5.1. Add Interface Configuration
By default, to set a static IP on eth1 under Debian-based systems, we add a block to /etc/network/interfaces and remove any other configuration related to eth1 :
Let’s break down the meaning of this block:
- auto eth1 enables automatic configuration for this interface during boot
- iface eth1 inet static sets eth1 as an IPv4 interface with a static address
- address , netmask , and gateway assign the respective addresses and network
- dns-nameservers , while not strictly necessary, sets the DNS servers to use
Of course, we can add more options like pre-up /etc/network/if-pre-up.d/secure.sh , which utilizes a script in the if-pre-up.d directory from earlier. Now, we’re ready to apply our configuration.
5.2. Restart Networking or Interface
At this point, we just need to restart networking via SysV with /etc/init.d/networking (deprecated, not recommended), systemd , our network management tool, or directly for changes to take effect , depending on the system version:
Basically, the last command uses the legacy ifupdown package to only toggle the particular interface.
However, NetworkManager can also handle the native Debian network setup files . Importantly, the method of choice depends more on the version of the system and less on our preferences.
5.3. Confirm Setup
Finally, we can verify the new settings:
Here, we see our changes are in effect via ip .
6. Static IP in RedHat and Other RPM Distributions
Again, we start by briefly looking at the network setup files in RedHat , SUSE , openSUSE , Fedora , CentOS , Oracle Linux , and other RPM-based Linux versions:
By utilizing the -P flag of tree , we can filter only network-related items in the /etc/sysconfig directory. In particular, /etc/sysconfig/network contains global options for all interfaces, while /etc/sysconfig/network-scripts/ifcfg-IFNAME files are responsible for configuring interface IFNAME .
However, since version 9 of RHEL, CentOS, Fedora, and other RPM-based distributions, ifcfg configuration files have been deprecated in favor of so-called keyfiles . This is also indicated by /etc/sysconfig/network-scripts-readme-ifcfg-rh.txt file:
Notably, keyfiles require the NetworkManager to function correctly.
6.1. network-scripts and NetworkManager
The SysV-based network-scripts package contains tools and scripts for different functions:
- /etc/init.d/network script to stop, start, and restart network components
- ifup* , ifdown* , and other /etc/sysconfig/network-scripts directory scripts
- ifup and ifdown native tools for interface state toggling
- usernetctl native command for general network configuration
In the case of RedHat and other related distributions, their newer versions have deprecated network-scripts in favor of NetworkManager .
To that end, some tools and scripts are either not available or have become wrappers for nmcli command lines. Consequently, for recent versions of RPM-based distributions, it’s usually best to leave NetworkManager installed, enabled, and started .
As an alternative, we might still be able to install the network-scripts package in its place, but that’s not recommended . If we do go that route, we must stop and disable NetworkManager via systemctl stop NetworkManager NetworkManager-wait-online, and systemctl disable NetworkManager NetworkManager-wait-online .
All of the above means that, while the interface settings files have mostly remained unchanged, their default processing has.
6.2. Create Interface Configuration File
After considering the network setup mechanisms, to configure eth1 with a static IP on RPM distributions, we can simply add the necessary options in a deprecated /etc/sysconfig/network-scripts/ifcfg-eth1 file :
As before, let’s check what the options mean:
- DEVICE=eth1 ensures we have the correct interface name
- BOOTPROTO is dhcp for DHCP, but our static configuration doesn’t require any protocol, so we use none
- ONBOOT=yes , similar to Debian’s auto , indicates the interface should be activated on boot
- IPADDR , NETMASK , GATEWAY , and BROADCAST are all set to their respective values for our static address
- DNS1 and DNS2 optionally set DNS servers
- USERCTL=no prevents non-superusers to control the interface
- NM_CONTROLLED=no stops NetworkManager from managing the interface
Of course, there are many other settings .
Alternatively, we can use the NetworkManager keyfiles instead . Let’s see an equivalent of the above in the new format:
Further, as indicated in /etc/sysconfig/network-scripts-readme-ifcfg-rh.txt , we can migrate all connections from the deprecated ifcfg format to the new keyfile format:
Notably, many keyfiles fields are the same in ifcfg files, while others are similar.
In addition, having to use NetworkManager for keyfiles means nmcli can perform our configuration directly :
This provides the added benefit of syntax checking.
6.3. Restart Networking or Interface
Naturally, the changes are applied once we restart the networking .
There are two main options for that:
- with systemd
- directly via network-scripts with /etc/rc.d/init.d/network (deprecated, not recommended)
By default, we’d use nmcli or the NetworkManager service:
Alternatively, we can employ nmcli and keyfiles to just manage the specific interface:
If we have them disabled, we can use basic tooling:
Once again, the last command only restarts eth1 . Also, the method of choice depends on the version of the system and our needs.
6.4. Confirm Setup
Now, we can confirm eth1 has the correct settings:
Here, we see that our interface has a static IP address.
7. Static IP in Slackware Distributions
In Slackware and its related distributions like Slax and Absolute Linux , the system startup goes through the original /etc/rc.d network file framework:
- /etc/rc.d/rc.inet1
- /etc/rc.d/rc.inet1.conf
- /etc/rc.d/rc.inet2
Of these, /etc/rc.d/rc.inet1 ensures we have a network, while /etc/rc.d/rc.inet1.conf sets the properties of our interfaces .
7.1. Disable Network Managers
Indeed, recent Slackware versions often come with NetworkManager by default . Still, external network management solutions can interfere with our manual settings or add more on top of them. Because of this, we stop and disable NetworkManager and any other similar services:
At this point, we can move on with the internal network setup mechanism.
7.2. Modify Interface Configuration
Basically, to configure a static IP address for eth1 on Slackware-based distributions, we can simply replace or add options for that interface in /etc/rc.d/rc.inet1.conf :
Notably, the matching numbers ( 0 ) within square brackets indicate settings for the same interface . Also, unlike other methods, there are no options for DNS servers, as Slackware uses only /etc/resolv.conf by default. Of course, we don’t set values for DHCP options.
7.3. Restart Networking
In Slackware-based Linux versions, the built-in networking restart mechanism is the /etc/rc.d/rc.inet1 script:
Now, we can confirm our new settings:
Conveniently, Slackware-based distributions also include the netconfig tool . It provides an interactive way to configure most network settings.
8. Static IP in Gentoo Distributions
Because Gentoo and its family are commonly source-based and highly flexible, we can perform their initialization process with many init systems.
By default, it’s the OpenRC init system, very similar to Slackware’s. Further, Gentoo uses Netifrc as its default integrated network configuration framework :
- /etc/conf.d/net for general interface setup (usually created by an administrator)
- /etc/init.d/net.lo and /etc/init.d/net.* scripts to control interfaces
Because of this, interface setup means editing /etc/conf.d/net and creating the related service script for that interface . Of course, keeping with the general philosophy of Gentoo, we can remove or ignore the netifrc package in favor of external managers.
8.1. Add Interface Configuration
By default, to set a static IP on eth1 on Gentoo-based systems, we modify /etc/conf.d/net with our settings :
Here, options refer to the interface name with a suffix. The configuration is similar to the options of ip .
Next, to control the interface, we have to create a respectively-named script by making a symbolic link with ln to /etc/init.d/net.lo :
In case /etc/init.d/net.lo is missing, we can acquire it via emerge :
Thus, we restored /etc/init.d/net.lo .
8.2. Restart the Interface
At this point, we are ready to start or restart our interface service net.eth1 with the new configuration:
Usually, the warning can safely be ignored.
To apply the settings on each restart, we add the script via OpenRC’s rc-update :
Further, we can do the same via systemctl where available:
Similar to Slackware’s netconfig , Gentoo includes the net-setup script for interactive network configuration.
9. Static IP in ArchLinux Distributions
Since ArchLinux is built from scratch, its family, including Manjaro and others , usually doesn’t provide its own network configuration framework. Instead, they integrate and leverage the framework of systemd-networkd by default:
This is more or less in contrast with Gentoo. Essentially, we can set a static IP in ArchLinux via systemd-networkd by creating a /etc/systemd/network/eth1.network file :
Now, we just disable DHCP and restart systemd-networkd :
At this point, we should have the correct static IP on eth1 .
10. Summary
In this article, we looked at network configuration under many different Linux distributions, with the main example of setting a static IP address.
In conclusion, while the way we configure our network setup can vary widely between Linux versions, there are also universal ways to perform it.

- RecentChanges
- HelpContents
NetworkConfiguration
- Attachments
: To get the most from this article, understand the following concepts before reading: basic unix command line tools, text editors, DNS, TCP/IP, DHCP, netmask, gateway |
3 ways to configure the network
Starting and stopping interfaces, reinitialize new network setup, network interface names, using dhcp to automatically configure the interface, configuring the interface manually, setting the speed and duplex, bringing up an interface without an ip address, the resolv.conf configuration file, the resolvconf program, dns configuration for networkmanager, using systemd-resolved for dns resolution, dhcp client configuration, bridging without switching, manual config, network init script config, bridges and vlans, caveats when using bridging and vlan, network config, bonding with active backup, /etc/network/interfaces, how to set the mtu (max transfer unit / packet size) with vlans over a bonded interface, legacy method, iproute2 method.
- The interfaces configuration file at /etc/network/interfaces (this page): for basic or simple configurations (e.g. workstation)
Setting up an Ethernet Interface
Upgrading and network interface names.
- Identify the interface in question (it will often be eth0). Adjust the remainder of these instructions accordingly.
- Reboot the machine to make sure it comes up correctly, and be prepared to intervene manually (e.g. Ctrl-Alt-Del and then boot into single-user mode from GRUB or LILO) if things don't work.
Defining the (DNS) Nameservers
- DHCP clients
- Choose a connection (from the Wired or Wireless tab) and click Edit.
- Click on the IPv4 Settings tab
- Choose 'Automatic (DHCP) addresses only' instead of just 'Automatic (DHCP)'.
- Enter the DNS servers in the “DNS servers” field, separated by spaces (e.g. 208.67.222.222 for OpenDNS).
- Click “Apply.”
Enabling systemd-resolved
Checking the status and flushing the cache in systemd-resolved, managing systemd-resolved settings, setting additional dns servers, setting additional search domains, howto use vlan (dot1q, 802.1q, trunk) (etch, lenny), howto create fault tolerant bonding with vlan (etch - stretch).

Multiple IP addresses on one Interface
NetworkConfiguration ( last modified 2023-07-18 11:37:31 )
- Debian privacy policy , Wiki team , bugs and config .
- Powered by MoinMoin and Python , with hosting provided by Metropolitan Area Network Darmstadt .
You are using an outdated browser. Please upgrade your browser or activate Google Chrome Frame to improve your experience.
Begin typing your search above and press return to search. Press Esc to cancel.
Linux Genie

How to Set Static IP Address on Debian 12?
A static IP address is an IP address that does not change/modify with time. It is useful for setting up servers, remote access, or other network services that require a fixed IP address (need to be reachable at a fixed location). By default, Debian 12 uses a dynamic IP address that is allocated by a DHCP server. However, you can configure your Debian 12 system to use a static IP address by editing the network configuration files.
This guide will explain all possible methods to set up a static IP address on Debian 12 along with the step-by-step instructions.
Prerequisite: Create a Backup File
Before network configuration, it is good practice to create a backup of the existing network settings via the “ cp ” command:
How to Set Up a Static IP Address on Debian 12?
There are different methods to set up a static IP address on Debian 12, depending on the network interface you are using. You can use either the command line or graphical interface to configure your network settings.
To set up a static IP address on Debian 12, follow these:
- Method 1: Editing the /etc/network/interfaces File
- Method 2: Using the nmcli (Command-line Tool)
- Method 3: Using the nmtui (Text-based Interface)
- Method 4: Using NetworkManager (Graphical-based Interface)
Let’s begin with the first method.
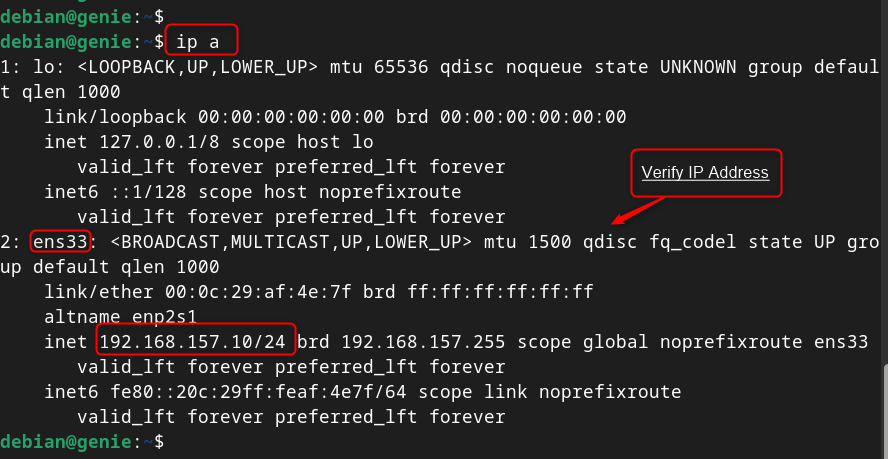
Method 1: Set Up a Static IP Address on Debian 12 Editing the /etc/network/interfaces File
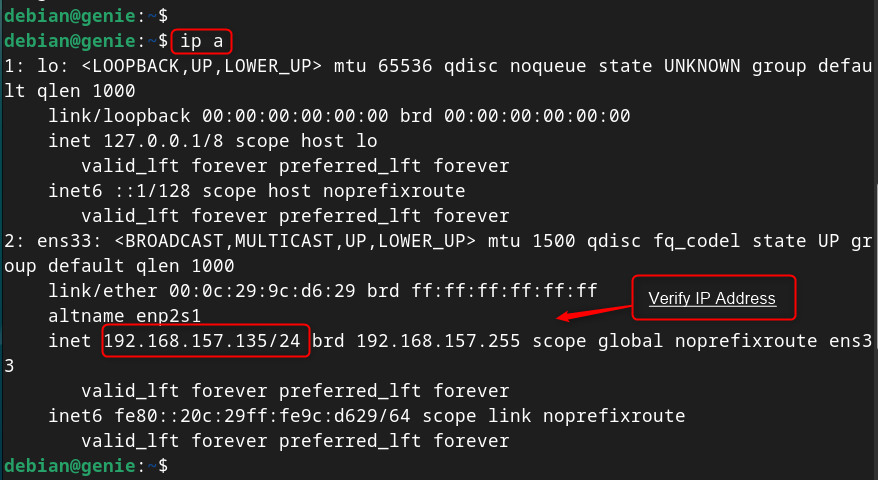
The “ /etc/network/interfaces ” file is a configuration file that defines how the network interfaces are configured on the system. To change an interface’s IP address, first check its current IP address:
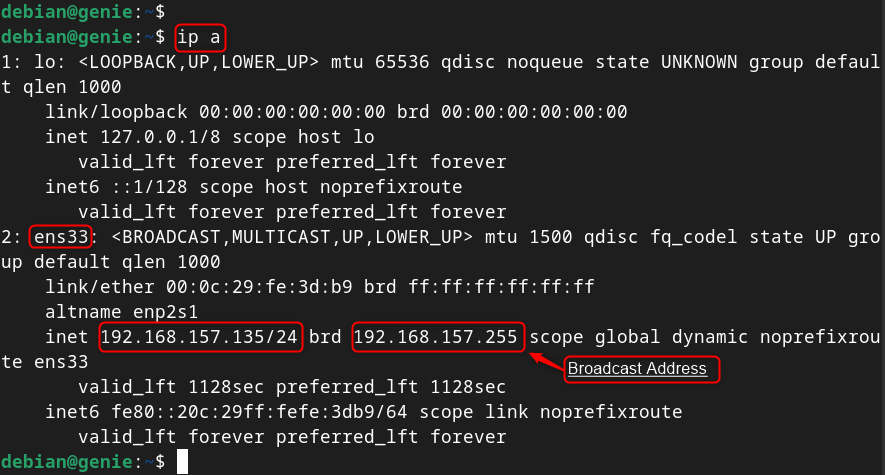
Here, the network interface “ ens33 ” has the IP address “ 192.168.157.135 ”. The last IP address on the network is “ 192.168.157.255 ”, which is the broadcast address. The IP address must be in the range of “ 192.168.157.135 ” to “ 192.168.157.255 ”.
To set up a static IP address on Debian 12, edit the “/ etc/network/interfaces ” file and add the desired IP address, netmask, gateway, and DNS server for your interface. After saving the file, restart the network service to take effect as follow:
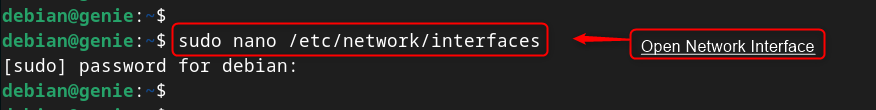
Step 1: Open /etc/network/interfaces File
First, access the /etc/network/interfaces file to edit the desired networking file via nano (editor):
Step 2: Configure Network Interface
Find the line that starts with “ iface ” and match to the network interface for configuration. For instance, to configure the ethernet interface “ ens33 ”, add the following lines (address, netmask, gateway, and dns-nameservers):
Users can replace the values with your own:

Save and close the file by pressing Ctrl+O and then Ctrl+X.
Note : Users can find the network interface using the “ nmcli connection show ” command by following the “ Device Name ” column.
IMPORTANT : Users ensure the default gateway is the same as the assigned IP address (for NAT or Bridged Network). Otherwise, look for “ iface ens33 inet dhcp ” and change the word “ dhcp ” to “ static ” by following the above configuration.
Step 3: Restart Networking Service
Finally, restart the networking service using the “ systemctl ” command or reboot the system for the changes to take effect:

Step 4: Verify Set up IP Address
To check the static IP address on the running system, use the “ ip ” command with “ a ” utility:

Finally, the static IP address has been set up using the “/ etc/network/interfaces ” file on Debian 12.
Note : Each method has independent settings/configurations to set up a static IP address on the Debian system.
Method 2: Set Up a Static IP Address on Debian 12 Using the nmcli
The nmcli is a part of the “ NetworkManager ” package that allows users to manage network connections from the terminal. This tool specifies the IP address, prefix, gateway, and DNS server associated with the device.
To set up a static IP address on Debian 12 using nmcli, follow these steps:
Step 1: List Network Connections
To list all the available network connections on the system, use “ nmcli ” command with “ connection show ”. It prints the network connections along with the connection name, UUID, connection type and device name:
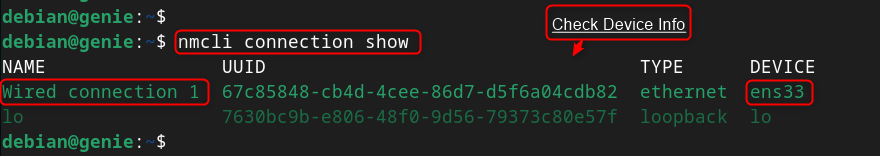
Step 2: Configure Network Connection
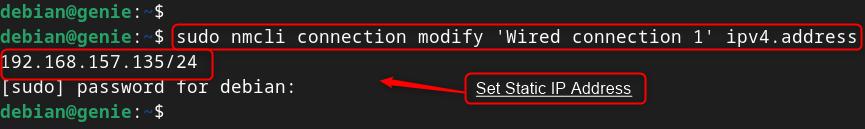
To configure the ethernet connection “ ens33 ”, use the “ Wired connection 1 ” in the below instructions:
Now, configure/modify connection settings. Such as IP address
- Assign/Set Static IP Address
- Set Default Gateway

- Modify Configuration from Automatic to Static

- Set the DNS IP (Google DNS Server)

- Activate/Enable the Connection
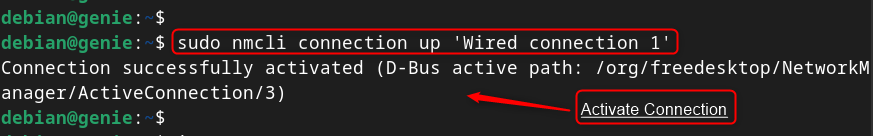
Note : To deactivate the connection, replace the “ down ” utility with the “ up ” utility in the above command.
Verify Static IP Address
Tip: Add or Delete Network Connection
Restart the NetworkManager service by typing sudo systemctl restart NetworkManager or reboot your system for the changes to take effect:
Finally, the static IP address has been set up on Debian 12 using nmcli command line tool.
Method 3: Set Up a Static IP Address on Debian 12 Using the nmtui
The nmtui is another part of the “ NetworkManager ” package that allows you to manage the network connections from a text-based user interface (TUI).
To set up a static IP address on Debian 12 using nmtui, follow these steps:
Step 1: Launch nmtui Interface
First, type “ nmtui ” command to launch the interface, use the arrow keys, and Enter key to navigate through the menus and options
Step 2: Edit a Connection
Select “ Edit a connection ” option and press Enter:
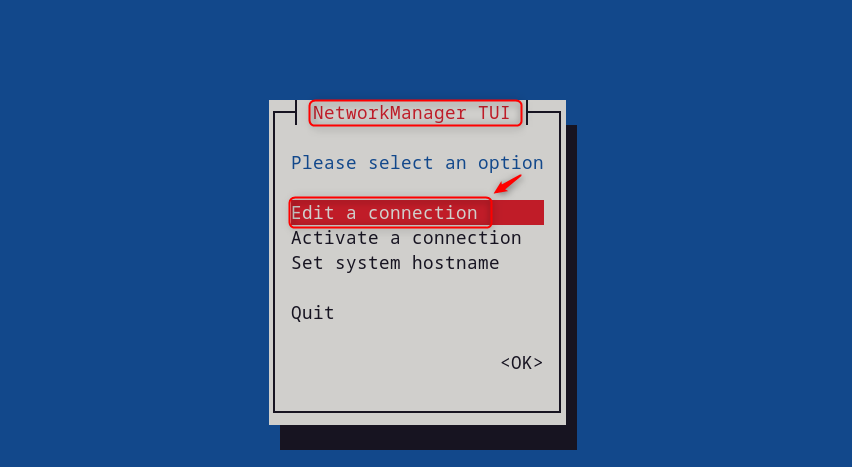
Select the connection (e.g., “ Wired connection 1 ”) that users want to configure and press Enter:

It navigates to the “ Edit a connection ” interface. At there,
- Select “ IPv4 CONFIGURATION ” and press Enter. Pick “ Manual ” from the list and hit the “ Enter ” button.
- Select “ Show ” to add or edit the IPv4 addresses of the connection.
- Enter the static IP address (192.168.157.10), gateway(192.168.157.2) and DNS servers (8.8.8.8 8.8.4.4) of the connection that users want to assign to the connection.
Scroll down, and hit the “ OK ” button to save the address and return to the previous menu:
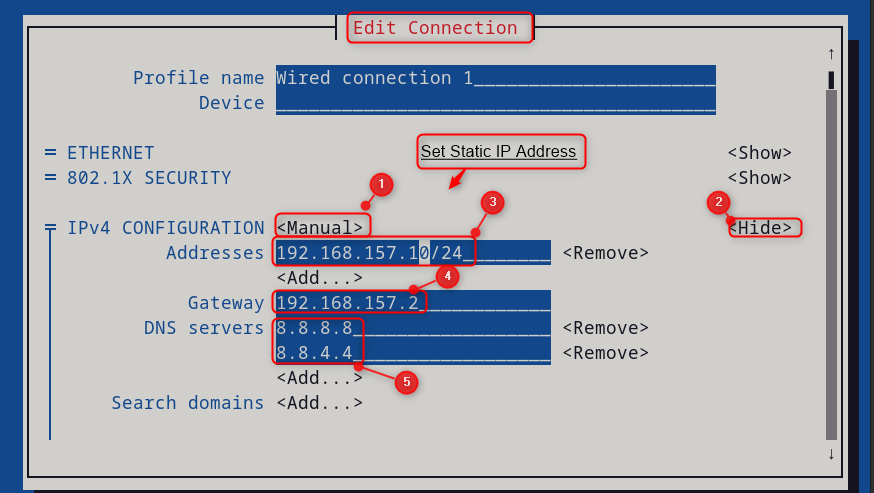
Step 3: Restart the NetworkManager Services

Then, press the “ Activate/Deactivate ” for the changes to take effect. Finally, back, and then “ Quit ” to exit the interface:
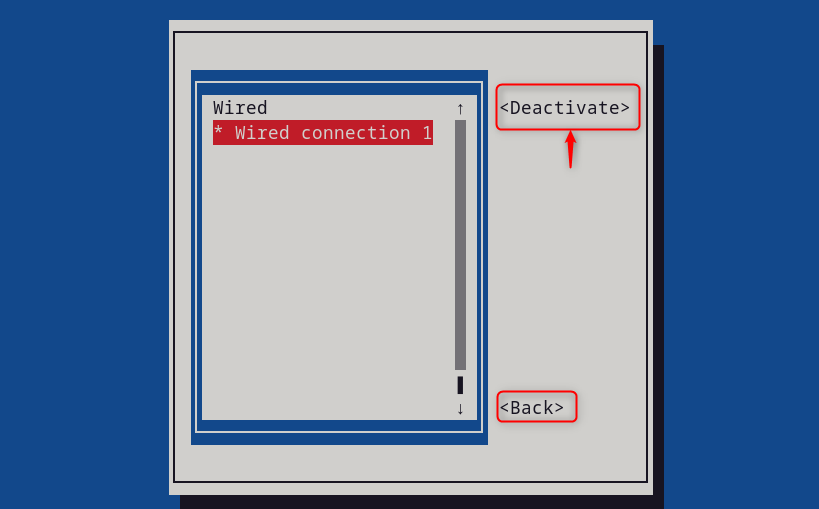
Step 4: Verify Static IP Address
Now, users can verify the Static IP address using the “ ip ” command with the “ a ” utility:
This section has set up/configured the static IP address on Debian 12 using nmtui tool.
Method 4: Set Up a Static IP Address on Debian 12 Using NetworkManager
The GUI method is an easy-to-implement method for static IP address configuration. To set up a static IP address using the graphical interface. Here are the steps:
Step 1: Click on the Network Icon
Click on the network icon on the top right corner of the screen and select “Wired Settings

Step 2: Access the Network Interface
In the “ Wired ” tab, hit the gear icon under the network interface for configuration:

Step 3: Edit Network Information
In the “ IPv4 ” tab, switch the method from “ Automatic (DHCP) ” to “ Manual ”. After that, enter the IP address (192.168.157.135), subnet mask (255.255.255.0), gateway (192.168.157.135) and DNS servers (8.8.4.4, 8.8.8.8). Finally, click on “ Apply ” to save the changes:

Note : If a user found any issue, check the Gateway that remains the same as in the previous configuration located in the “ Details ” tab.
Step 4: Restart Network Interface
Now, restart the network interface via toggle button for the changes to take effect:
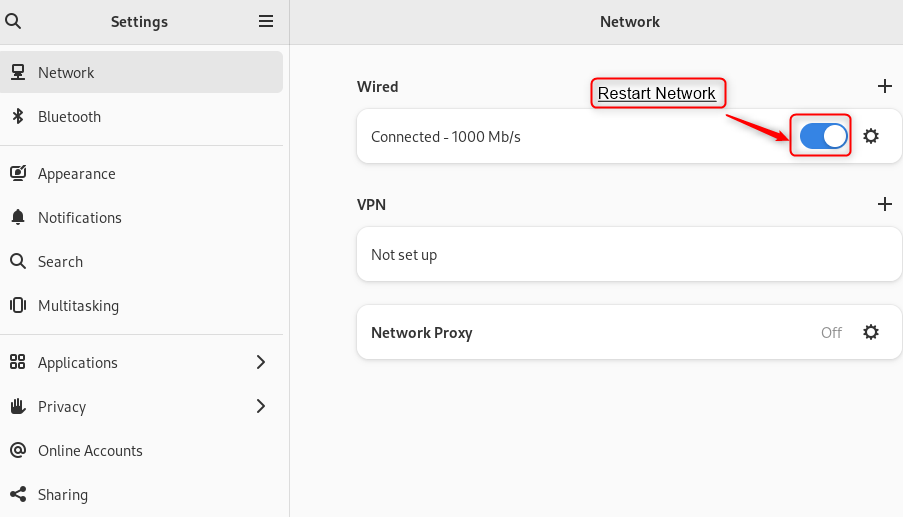
Step 5: Verification
User can verify the static ip address on settings by navigating to the “ Detail ” tab:
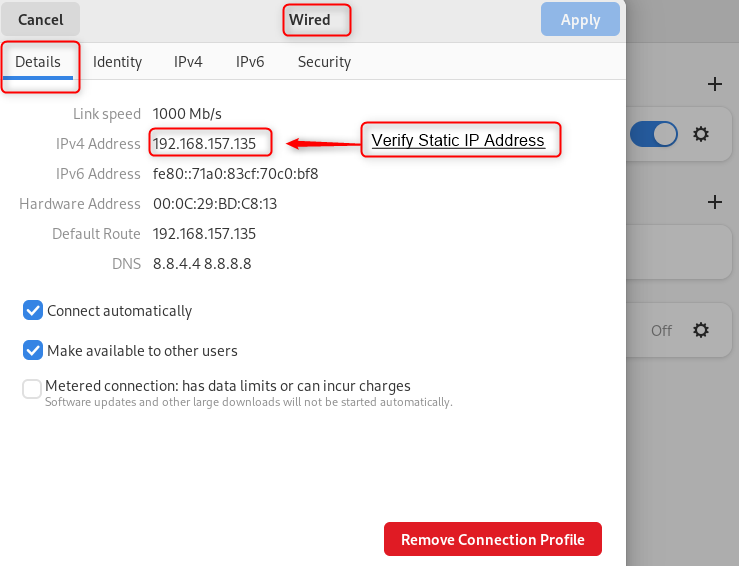
In this way, a static IP address has been set up on Debian 12 using the GUI.
Setting up a static IP address on Debian 12 is a simple and useful task that can improve your network security and stability. To set up a static IP address on Debian 12, use the “ /etc/network/interfaces ” file, the “ nmcli ” tool, and the “ nmtui ” interface.
Alternatively, use the “ NetworkManager ” graphical tool and configure the IPv4 settings for your connection. The easiest method is to use the “ NetworkManager ” tool to static IP addresses on Debian 12.
This guide has explained all possible ways to set up a static IP address on Debian 12.


- The Debian Administrator's Handbook
8.2. Configuring the Network
BACK TO BASICS Essential network concepts (Ethernet, IP address, subnet, broadcast)
NOTE NetworkManager
8.2.1. Ethernet Interface
Example 8.1. DHCP configuration
IN PRACTICE Names of network interfaces
Example 8.2. Static configuration
NOTE Multiple addresses
8.2.2. Wireless Interface
8.2.2.1. installing the required firmwares, 8.2.2.2. wireless specific entries in /etc/network/interfaces.
Example 8.3. DHCP configuration for a wireless interface
HISTORY WEP encryption
8.2.3. Connecting with PPP through a PSTN Modem
8.2.4. connecting through an adsl modem, 8.2.4.1. modems supporting pppoe.
TIP Starting ppp at boot
8.2.4.2. Modems Supporting PPTP
8.2.4.3. modems supporting dhcp.
BACK TO BASICS Crossover cable for a direct Ethernet connection

8.2.5. Automatic Network Configuration for Roaming Users
- Prev Chapter 8. Basic Configuration: Network, Accounts...
- Next 8.3. Setting the Hostname and Configuring the Nam...
How to Configure Static IP Address on Ubuntu 20.04
Published on Sep 15, 2020
This article explains how to set up a static IP address on Ubuntu 20.04.
Typically, in most network configurations, the IP address is assigned dynamically by the router DHCP server. Setting a static IP address may be required in different situations, such as configuring port forwarding or running a media server .
Configuring Static IP address using DHCP #
The easiest and recommended way to assign a static IP address to a device on your LAN is to configure a Static DHCP on your router. Static DHCP or DHCP reservation is a feature found on most routers which makes the DHCP server to automatically assign the same IP address to a specific network device, each time the device requests an address from the DHCP server. This works by assigning a static IP to the device’s unique MAC address.
The steps for configuring a DHCP reservation vary from router to router. Consult the vendor’s documentation for more information.
Ubuntu 17.10 and later uses Netplan as the default network management tool. The previous Ubuntu versions were using ifconfig and its configuration file /etc/network/interfaces to configure the network.
Netplan configuration files are written in YAML syntax with a .yaml file extension. To configure a network interface with Netplan, you need to create a YAML description for the interface, and Netplan will generate the required configuration files for the chosen renderer tool.
Netplan supports two renderers, NetworkManager and Systemd-networkd. NetworkManager is mostly used on Desktop machines, while the Systemd-networkd is used on servers without a GUI.
Configuring Static IP address on Ubuntu Server #
On Ubuntu 20.04, the system identifies network interfaces using ‘predictable network interface names’.
The first step toward setting up a static IP address is identifying the name of the ethernet interface you want to configure. To do so, use the ip link command, as shown below:
The command prints a list of all the available network interfaces. In this example, the name of the interface is ens3 :
Netplan configuration files are stored in the /etc/netplan directory. You’ll probably find one or more YAML files in this directory. The name of the file may differ from setup to setup. Usually, the file is named either 01-netcfg.yaml , 50-cloud-init.yaml , or NN_interfaceName.yaml , but in your system it may be different.
If your Ubuntu cloud instance is provisioned with cloud-init, you’ll need to disable it. To do so create the following file:
To assign a static IP address on the network interface, open the YAML configuration file with your text editor :
Before changing the configuration, let’s explain the code in a short.
Each Netplan Yaml file starts with the network key that has at least two required elements. The first required element is the version of the network configuration format, and the second one is the device type. The device type can be ethernets , bonds , bridges , or vlans .
The configuration above also has a line that shows the renderer type. Out of the box, if you installed Ubuntu in server mode, the renderer is configured to use networkd as the back end.
Under the device’s type ( ethernets ), you can specify one or more network interfaces. In this example, we have only one interface ens3 that is configured to obtain IP addressing from a DHCP server dhcp4: yes .
To assign a static IP address to ens3 interface, edit the file as follows:
- Set DHCP to dhcp4: no .
- Specify the static IP address. Under addresses: you can add one or more IPv4 or IPv6 IP addresses that will be assigned to the network interface.
- Specify the gateway.
- Under nameservers , set the IP addresses of the nameservers.
When editing Yaml files, make sure you follow the YAML code indent standards. If the syntax is not correct, the changes will not be applied.
Once done, save the file and apply the changes by running the following command:
Verify the changes by typing:
That’s it! You have assigned a static IP to your Ubuntu server.
Configuring Static IP address on Ubuntu Desktop #
Setting up a static IP address on Ubuntu Desktop computers requires no technical knowledge.
In the Activities screen, search for “settings” and click on the icon. This will open the GNOME settings window. Depending on the interface you want to modify, click either on the Network or Wi-Fi tab. To open the interface settings, click on the cog icon next to the interface name.
In “IPV4” Method" tab, select “Manual” and enter your static IP address, Netmask and Gateway. Once done, click on the “Apply” button.
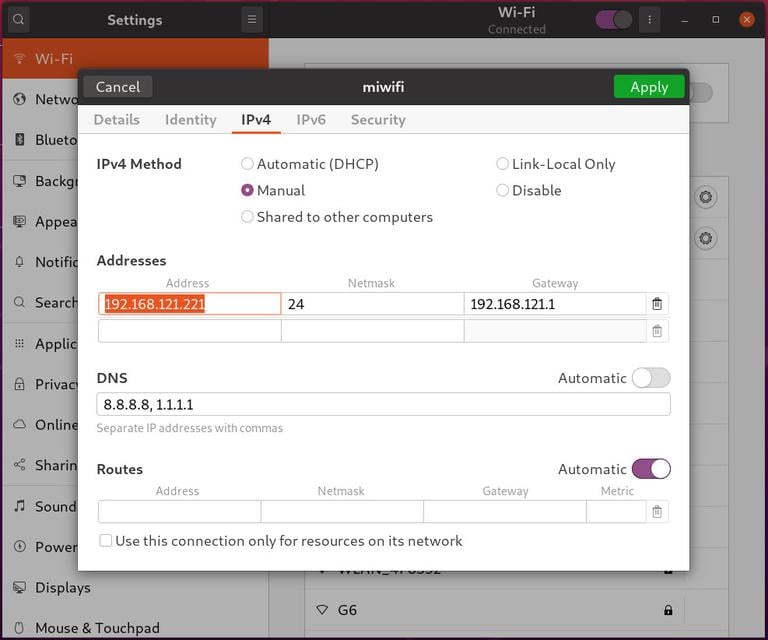
To verify the changes, open your terminal either by using the Ctrl+Alt+T keyboard shortcut or by clicking on the terminal icon and run:
The output will show the interface IP address:
Conclusion #
We’ve shown you how to configure a static IP address on Ubuntu 20.04.
If you have any questions, please leave a comment below.
Related Tutorials
How to Configure Static IP Address on Ubuntu 18.04
How to install php 8 on ubuntu 20.04, how to install flask on ubuntu 20.04.
- How to Install Python 3.9 on Ubuntu 20.04
- How to Install Nvidia Drivers on Ubuntu 20.04
- How to Set Up WireGuard VPN on Ubuntu 20.04
- How to Install and Configure Squid Proxy on Ubuntu 20.04
If you like our content, please consider buying us a coffee. Thank you for your support!
Sign up to our newsletter and get our latest tutorials and news straight to your mailbox.
We’ll never share your email address or spam you.
Related Articles
Mar 9, 2020

Dec 5, 2020
Nov 21, 2020


How to Set Static IP Address and Configure Network in Linux
If you are a Linux system administrator, time will come when you will need to configure networking on your system. Unlike desktop machines where you can use dynamic IP addresses, on a server infrastructure, you will need to setup a static IP address (at least in most cases).
Read Also: How to Set or Change System Hostname in Linux </p
This article is meant to show you how to configure static IP address on most frequently used Linux distributions.
For the purpose of this tutorial, we will use the following Internet Protocol version 4 (IPv4) details:
Configure Static IP Address in RHEL/CentOS/Fedora:
To configure static IP address in RHEL / CentOS / Fedora , you will need to edit:
Where in the above "ifcfg-eth0" answers to your network interface eth0 . If your interface is named “ eth1" then the file that you will need to edit is "ifcfg-eth1" .
Let’s start with the first file:
Open that file and set:
Note : Make sure to open the file corresponding to your network interface. You can find your network interface name with ifconfig -a command .
In that file make the following changes:
You will only need to edit the settings for:
- DNS1 and DNS2
Other settings should have already been predefined.
Next edit resolve.conf file by opening it with a text editor such as nano or vi :
Once you have made your changes restart the networking with:
Set Static IP Address in Debian / Ubuntu
To setup static IP address in Debian / Ubuntu , open the following file:
You may see a line looking like this:
Change it so it looks like this:
Save the file and then edit /etc/resolv.conf like this:
Restart the networking on your system with:
Your static IP address has been configured.
Conclusion:
You now know how to configure a static IP address on a Linux distro. If you have any questions or comments, please do not hesitate to submit them in the comment section below.
Hey TecMint readers ,
Exciting news! Every month, our top blog commenters will have the chance to win fantastic rewards, like free Linux eBooks such as RHCE , RHCSA , LFCS , Learn Linux , and Awk , each worth $20 !
Learn more about the contest and stand a chance to win by sharing your thoughts below !

Previous article:
Next article:
Each tutorial at TecMint is created by a team of experienced Linux system administrators so that it meets our high-quality standards.
Related Posts

How to Remove Systemd Services on Linux
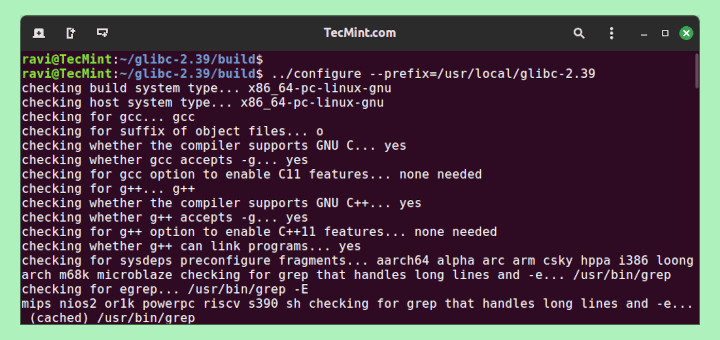
How to Install and Run Multiple glibc Libraries in Linux
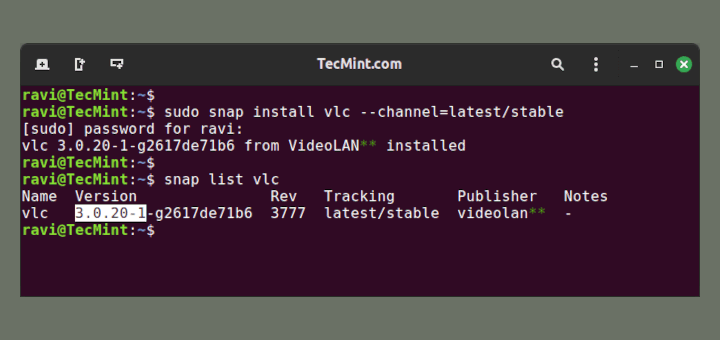
How to Install Particular Versions of Packages with Snap

Rename – A Command Line Tool For Renaming Multiple Files in Linux
chkconfig vs. systemctl: Manage Linux Services Efficiently

Mutt – A Command Line Email Client to Send Mails from Terminal
34 Comments
There isn’t an “eth0” on my server because it is connected by WIFI only.
@Thuemaychuaonet,
If your server is connected only via WiFi, the network interface will likely have a different name, such as ` wlan0 ` or something similar, depending on your system and its configuration.
The steps to set a static IP address and configure the network are similar, but you’ll need to use the correct interface name for your WiFi connection.
You can find the name of your WiFi interface by running the ` ip a` command in the terminal. Once you have the correct interface name, you can follow the same process to configure your network settings.
The time will come when you will need to configure networking on your system. Unlike desktop machines where you can use dynamic IP addresses, on a server infrastructure, you will need to set up a static IP address (at least in most cases).
Terrible – and my ‘ linux distro ‘ isn’t the same as yours, there’s no ‘ /etc/sysconfig/ ‘ folder.
In Ubuntu 20.04 there is no interfaces file they switch to netplan . If you can update this article to include the new change it will help a lot.
thanks Raouf
Well, this isn’t correct. Just trashed my Linux mint distro
Is it public Static IP? or can I use to access data from other networks?
Failed to restart network.service: Unit network.service not found.
I’m asking a question on a fairly old thread, but just in case, is it possible to do this on a WIFI network?
For example, when using the first command (# nano /etc/network/interfaces ) in Ubuntu, the result I see is:
There isn’t an “ eth0 ” on my server because it is connected by WIFI only. Will it still work using another option?
Yes it will work I think so, just change the settings in the interfaces file as explained in this article.
I set the static IP in ifcfg-eth0, added HWADDR and UUID, but on reboot system does not associate the IP to eth0.
This is VM. Any idea why its happening and steps to troubleshoot.
I think you need to make sure that you select “ manual ” and the correct IP address, subnet mask, and gateway and save the configuration as explained in the article. Also, I personally would select a new and different IP address, so that you can really check if it has been saved by opening the terminal and typing:
after a restart.
If i set ip address as static am not able to ping google.com why and also packages are not installed.
Please give me reply as soon as possible.
@Rajeshkar,
Please add the DNS Name servers in your /etc/resolv.conf file..
@Ravi Saive thanks for your reply , yes i did /etc.resolv.conf also but getting the same problem
@Rajesekar,
The file is /etc/resolv.conf , in this file add your DNS name servers for example.
When I enter the /etc/resolv.conf file, what is it supposed to look like? And when you say “edit” do you mean delete what’s there and write what you’ve provided, or just add new lines?
Hello Marin, Thank you very much for this article. It was a major help in my class project. This is my first time using a vm and it is an awesome learning experience. I’m really glad I ran into this article, it was well written and easy to follow.
Just wanted to say a million thank you’s for this well-written, comprehensive and easily-understood article! Awesome stuff! A real lifesaver too, as I had to quickly configure a static IP for myself to get access to remote computing. Thank you! :-D
A question from a linux newbie. Does this instruction apply for both ubuntu running on my desktop PC as well as debian linux on an embedded board?
Yes, the instructions will works on any Debian/Ubuntu based distribution without any issues..have you tried on your embedded board? does these instructions worked? let us know.
Hi Ravi, thanks for your reply.
Default the folder /etc/sysconfig does not exist on my embedded system. Of Course i could create it as well as the files mentioned, but it would be out of the context of this instructions.
Thanks, Rob
I found here very good stuff! You are doing an excellent job and I like your site! Thanks!
Thanks for finding this site very useful and thanks for appreciating our work, Keep visiting for more such useful articles…
Great job, I was I actually looking for an article like this one. So thank you so very much. Keep up the good work.
Thanks for appreciating and finding this article useful, keep connected to Tecmint for such wonderful articles…:)
What if I have 2 NICs on my server one for LAN & one for WAN and I want to set one of them (WAN) as default gateway? How to configure this server as gateway and as a router.
The easiest way to add default gateway using route command as shown:
Don’t forget to replace the gateway IP address and interface-name in the above command.
One can also use following command to setup static IP on eth0 interface for example. # ifconfig eth0 192.168.1.1 netmask 255.255.255.0 up # route add default gw 192.168.0.1 # service network restart
Thanks for the tip, but I think setting IP address directly from the commandline using ifconfig and route will only allow you to set temporarily, once you reboot, these settings disappears. So, the best option to set static IP address permanently in network configuration files only….
wipe on reboot, so that best option is to set permannetly
Hello Ravi, What is difference between the service “NetworkManager” and “network”
@Augustine,
This article will help you to understand the difference between and NetworkManager and Network: http://askubuntu.com/questions/1786/what-is-the-difference-between-network-manager-and-ifconfig-ifup-etc
Why do we need to specify DNS in both ifcfg-eth0 and resolvlf.conf?
Hello Augustine,
Actually if you have added the DNS servers in the ifcfig-eth0 file the DNS servers will be automatically added to /etc/resolv.conf. You can skip defining the DNS servers in the ifcfig-eth0 file, but then you will need to have them set in /etc/resolv.conf manually. It’s a good practice to make sure that the DNS servers are specified correctly in both files, this is why the article says to set them in both files.
Got Something to Say? Join the Discussion... Cancel reply
Thank you for taking the time to share your thoughts with us. We appreciate your decision to leave a comment and value your contribution to the discussion. It's important to note that we moderate all comments in accordance with our comment policy to ensure a respectful and constructive conversation.
Rest assured that your email address will remain private and will not be published or shared with anyone. We prioritize the privacy and security of our users.
Save my name, email, and website in this browser for the next time I comment.
Stack Exchange Network
Stack Exchange network consists of 183 Q&A communities including Stack Overflow , the largest, most trusted online community for developers to learn, share their knowledge, and build their careers.
Q&A for work
Connect and share knowledge within a single location that is structured and easy to search.
Good detailed explanation of /etc/network/interfaces syntax?
I understood the very basic concept of how to use /etc/network/interfaces , but all I find online are examples, example after example, which I can copy-paste from. What I miss is an explanation of the syntax, an explanation of the meaning of the commands and which order the commands require. I want to understand, because most of the time copy-paste is not enough, because I'm not working on a fresh machine, so I can't just overwrite existing configurations because it would break a lot of stuff. man interfaces was not very helpful since it is written very complicated.
Example questions I have: what does inet in an iface line mean exactly (I could not even find it in the manpage), what does manual in an iface line mean exactly (many examples use it, but according to manpage it needs an extra config file then, which the examples don't present), when do I use or need them? When not? When I create a bridge, what exactly happens to the interfaces?
- 7 The man page says what comes after the interface name is the address family that the interface uses. "inet" is the name for IPv4, inet6 for ipv6. There's also ipx, x25, appletalk..., though ifupdown only deal with inet/inet6/ipx as the man page explains. manual means that ifupdown don't do anything about them, you have to do it yourself manually. – Stéphane Chazelas Commented May 8, 2014 at 10:25
4 Answers 4
Well, let’s separate it into pieces, to make it easier to understand /etc/network/interfaces :
Link layer +interface type options (generally the first of each interface stanza and called address family + method by interfaces(5) manpages):
auto interface – Start the interface(s) at boot. That’s why the lo interface uses this kind of linking configuration.
allow-auto interface – Same as auto
allow-hotplug interface – Start the interface when a "hotplug" event is detected. In the real world, this is used in the same situations as auto but the difference is that it will wait for an event like "being detected by udev hotplug api" or "cable linked". See " Related Stuff(hotplug) " for additional info.
These options are pretty much "layer 2" options, setting up link states on interfaces, and are not related with "layer 3" (routing and addressing). As an example you could have a link aggregation where the bond0 interface needs to be up whatever the link state is, and its members could be up after a link state event:
So, this way I create a link aggregation and the interfaces will be added to it and removed on cable link states.
Most common interface types:
All options below are a suffix to a defined interface ( iface <Interface_family> ). Basically the iface eth0 creates a stanza called eth0 on an Ethernet device. iface ppp0 should create a point-to-point interface, and it could have different ways to acquire addresses like inet wvdial that will forward the configuration of this interface to wvdialconf script. The tuple inet / inet6 + option will define the version of the IP protocol that will be used and the way this address will be configured ( static , dhcp , scripts ...). The online Debian manuals will give you more details about this.
Options on Ethernet interfaces:
inet static – Defines a static IP address.
inet manual – Does not define an IP address for an interface. Generally used by interfaces that are bridge or aggregation members, interfaces that need to operate in promiscuous mode ( e.g. port mirroring or network TAPs ), or have a VLAN device configured on them. It's a way to keep the interface up without an IP address.
inet dhcp – Acquire IP address through DHCP protocol.
inet6 static – Defines a static IPv6 address.
This example will bring eth0 up, and create a VLAN interface called vlan10 that will process the tag number 10 on an Ethernet frame.
Common options inside an interface stanza(layer 2 and 3):
address – IP address for a static IP configured interface
netmask – Network mask. Can be omitted if you use cidr address. Example:
gateway – The default gateway of a server. Be careful to use only one of this guy.
vlan-raw-device – On a VLAN interface, defines its "father".
bridge_ports – On a bridge interface, define its members.
down – Use the following command to down the interface instead of ifdown .
post-down – Actions taken right after the interface is down.
pre-up – Actions before the interface is up.
up – Use the following command to up the interface instead of ifup . It is up to your imagination to use any option available on iputils . As an example we could use up ip link set $IFACE up mtu 9000 to enable jumbo frames during the up operation(instead of using the mtu option itself). You can also call any other software like up sleep 5; mii-tool -F 100baseTx-FD $IFACE to force 100Mbps Full duplex 5 seconds after the interface is up.
hwaddress ether 00:00:00:00:00:00 - Change the mac address of the interface instead of using the one that is hardcoded into rom, or generated by algorithms. You can use the keyword random to get a randomized mac address.
dns-nameservers – IP addresses of nameservers. Requires the resolvconf package. It’s a way to concentrate all the information in /etc/network/interfaces instead of using /etc/resolv.conf for DNS-related configurations. Do not edit the resolv.conf configuration file manually as it will be dynamically changed by programs in the system.
dns-search example.net – Append example.net as domain to queries of host, creating the FQDN. Option domain of /etc/resolv.conf
wpa-ssid – Wireless: Set a wireless WPA SSID.
mtu - MTU size. mtu 9000 = Jumbo Frame. Useful if your Linux box is connected with switches that support larger MTU sizes. Can break some protocols(I had bad experiences with snmp and jumbo frames).
wpa-psk – Wireless: Set a hexadecimal encoded PSK for your SSID.
ip_rp_filter 1 - Reverse path filter enabled. Useful in situations where you have 2 routes to a host, and this will force the packet to come back from where it came(same interface, using its routes). Example: You are connected on your lan( 192.168.1.1/24 ) and you have a dlna server with one interface on your lan( 192.168.1.10/24 ) and other interface on dmz to execute administrative tasks( 172.16.1.1/24 ). During a ssh session from your computer to dlna dmz ip, the information needs to come back to you, but will hang forever because your dlna server will try to deliver the response directly through it's lan interface. With rp_filter enabled, it will ensure that the connection will come back from where it came from. More information here .
Some of those options are not optional. Debian will warn you if you put an IP address on an interface without a netmask, for example.
You can find more good examples of network configuration here .
Related Stuff :
Links that have information related to /etc/network/interfaces network configuration file:
- HOWTO: Wireless Security - WPA1, WPA2, LEAP, etc .
- How can I bridge two interfaces with ip/iproute2? .
- What is a hotplug event from the interface?
- Thanks, this helps much. Does inet has anything to do with "internet"? I read somehwere that it just means "IPv4" and inet6 means "IPv6", but the term "inet" is really confusing when you see it and confuse it with short for "internet". And the names one uses, like eth0 , are these defined or can I chose them myself? If I have more than one LAN adapter, how do I tell which eth belongs to which LAN adapter? – Foo Bar Commented May 9, 2014 at 12:48
- 2 Both. Together they define method of ip address aquisition(dhcp, static, ppp scripts, no address) and version of ip protocol( inet = v4 and inet6 = v6). The interface names pretty much depends on the distribution you are using, and the way udev is configured. Debian uses eth* and wlan* to cable and wireless interfaces. Fedora uses the biosdevname scheme where em0 is the first built-in ethernet interface on your motherboard, and p<slot>p<eth port> the name for a PCI nic. You can fix network names at /etc/udev/rules.d/70-persistent-net.rules or create alias on interfaces . – user34720 Commented May 9, 2014 at 13:05
- 3 Regarding "gateway - the default gateway of a server. be carefull to use only one of this guy." Is that one per stanza or one gateway interface among all stanzas? – ctbrown Commented Dec 12, 2014 at 14:17
- 2 Should be one gateway among all stanzas, or, you will have trouble with your default route. To work with multi gateway / multi link, some thinkering with iptables + package marking + ip rules will be needed. – user34720 Commented Jan 20, 2015 at 11:26
- 2 allow-hotplug does not wait in the background for "cable linked" events on Ethernet ports, and it has never done so. unix.stackexchange.com/a/520633/29483 – sourcejedi Commented May 23, 2019 at 14:22
I would also add that:
- interfaces is for ifup/ifdown services.
- When u use allow-hotplug it will not start with ifup/ifdown, bcos u need to use flag --allow=hotplug.
U may track what is happening with ifup by using --verbose flag.
Im not 100% shure of this, but it seems that basically when ifup is called u will execute all from /etc/network/interfaces with up ... if not stated otherwise.
Im not shure how it relates to : service networking ...
Would be nice if someone would point whats happening after call:
in relation to ifup/ifdown.
If you need to add options when using the resolvconf package, i.e. on Ubuntu you put that configuration in /etc/resolvconf/resolv.conf.d/base :
Important thing for attribute names is:
There are no any file with standard description. This mean that this file is implementation defined
It can be lower, upper or mixed case
It does not matter '-' or '_'
It can not contain spaces and tabs
As far as ifupdown sources says
Except some common names like "pre-up" "down" and etc, that can not be written with another way
- This does not add anything of value to @user34720 response. – number9 Commented Mar 24, 2021 at 19:11
You must log in to answer this question.
Not the answer you're looking for browse other questions tagged networking bridge interface ..
- The Overflow Blog
- Community Products Roadmap Update, July 2024
- Featured on Meta
- We spent a sprint addressing your requests — here’s how it went
- Upcoming initiatives on Stack Overflow and across the Stack Exchange network...
Hot Network Questions
- When do people say "Toiletten" in the plural?
- Are there alternative statistics to a p-value in NHST?
- Is it possible for some p-values to be impossible? (because statistic generated by parametric bootstrap is mostly the same value.)
- Changing equation into elliptic curve
- Is there a way to change a cantrip spell type to Necromancy in order to fulfil the requirement of the Death Domain Reaper ability for Clerics?
- Could two moons orbit each other around a planet?
- Reversing vowels in a string
- Job talk Q&A: handling the room vs. being respectful
- The meaning of "奪耳" in 《說文解字》
- What does "that" in "No one ever meant that, Drax" refer to?
- A manifold whose tangent space of a sum of line bundles and higher rank vector bundles
- Why did the main wire to my apartment burn before the breaker tripped?
- Why does the length of an antenna matter when electromagnetic waves propagate perpendicular to the antenna?
- Was I wrongfully denied boarding for a flight where the airliner lands to a gate that doesn't directly connect to the international part the airport?
- What spells can I cast while swallowed?
- How to write a module that provides an 'unpublish comment' shortcut link on each comment
- What is the difference, if any, between "en bas de casse" and "en minuscules"?
- Question about NMAP HTTP Verb Tampering
- How do I drill a 60cm hole in a tree stump, 4.4 cm wide?
- I'm not sure what I damaged in crash. Derailleur? gears?
- Why do Electric Aircraft Seem to Eschew Photovoltaics?
- Can the differential be unitless while the variable have an unit in integration?
- Improve spacing around equality = and other math relation symbols
- Book about a boy who becomes a sorcerer
Stack Exchange Network
Stack Exchange network consists of 183 Q&A communities including Stack Overflow , the largest, most trusted online community for developers to learn, share their knowledge, and build their careers.
Q&A for work
Connect and share knowledge within a single location that is structured and easy to search.
The network setting for /etc/network/interfaces for static IP of a supernet address
I want to change my Ubuntu to static IP. My current IP setting is:
what should I put as the network in /etc/network/interfaces (note the network mask of 255.255.240.0 )?
- What exactly do you have trouble with? I don't see any network statements in interfaces(5) . You might consider rephrasing your question and add some details. – Andreas Wiese Commented Mar 31, 2014 at 19:56
- 1 Stop using ifconfig , use ip addr instead. This is what ifupdown (the software that parses /etc/network/interfaces ) uses under the hood anyway, so you will definitely want to get used to it. – BatchyX Commented Mar 31, 2014 at 20:06
- @BatchyX, I use ip addr for other things but not this one, because it'd be worse that ifconfig -- ifconfig at least gives me address, broadcast & netmask, but ip addr doesn't give me netmask, at least my version doesn't. – xpt Commented Apr 1, 2014 at 2:40
- @xpt: ip addr gives you the modern CIDR prefix length just next to the IP address. It also accept old-style netmask on input (i.e. 192.168.31.254/255.255.240.0 ) – BatchyX Commented Apr 2, 2014 at 17:52
If I'm understanding your question, to set a static IP, your network runs from 191.168.16.1 - 191.168.31.254, with the identity address at 192.168.16.0 and the broadcast at 192.168.31.255. I've never had to use the Network keyword, but I've never used a supernet address on a host. I've only seen them used for route aggregation.
- My IP is not a good example for network for this case. I guess if my IP is 192.168.18.159 , my network value is still 192.168.16.0 , correct? BTW, are you saying that is network optional for /etc/network/interfaces ? I'm following guylabs.ch/2013/07/25/configure-a-static-ip-in-ubuntu-13-04 , and there is a network there. – xpt Commented Apr 1, 2014 at 2:29
- it depends on your network mask. for the Class C network 192.168.X.Y, a subnetted network would have >24 bits of mask (255.255.255.0-252), a supernetted net would have < 24 bits mask (255.0-255.0-252.0), and a normal (class natural) Class C would be 255.255.255.0. which one it is defines the "shape" of your IP address layout. – Frank Thomas Commented Apr 1, 2014 at 11:27
- 1 yep. now that said, there is the possibility that subnetworks are defined under this address space, so make sure when configuring systems in this way that they all have a 255.255.240.0 mask. if you see any more confining masks (more than 20 bits) you will need to recalculate the network range, ID, and broadcast when configuring systems on that network. I use this calculator: subnet-calculator.com – Frank Thomas Commented Apr 1, 2014 at 14:16
- 2 network is totally ignored by ifupdown, the system can figure it by itself anyway. Your broadcast is useless here: the system will pick the same in your case. Your gateway is not part of your subnet, so ifupdown will fail at that point. – BatchyX Commented Apr 2, 2014 at 18:00
- 1 And nobody told you that classful addressing has been deprecated and dead for 20 years now ? All the Internet uses Classless interdomain routing now (CIDR for short, see RFC 4632), so there is no concept of "classes" or "supernetting" anymore. You may even specify a prefix length in netmask (like netmask 20 ) instead of a netmask. – BatchyX Commented Apr 2, 2014 at 18:08
You must log in to answer this question.
Not the answer you're looking for browse other questions tagged linux ubuntu networking ..
- The Overflow Blog
- Community Products Roadmap Update, July 2024
- Featured on Meta
- We spent a sprint addressing your requests — here’s how it went
- Upcoming initiatives on Stack Overflow and across the Stack Exchange network...
Hot Network Questions
- Why did the general choose this as the exact time of attack?
- Are there rules for gender of durations?
- Where is the pentagon in the Fibonacci sequence?
- How to write a module that provides an 'unpublish comment' shortcut link on each comment
- It was the second, but we were told it was the fifth
- Can player build dungeons in D&D? I thought that was just a job for the DM
- Why did the main wire to my apartment burn before the breaker tripped?
- Improve spacing around equality = and other math relation symbols
- What does "that" in "No one ever meant that, Drax" refer to?
- If I Trace "Pickup", will I pickup?
- Weather on a Flat, Infinite Sea
- Dual citizenship with USA & South Africa and exited South Africa on wrong passport (USA). What passport do I use to reenter SA?
- Why is there not a test for diagonalizability of a matrix
- Struggling w/ Jesus and Jewish law
- Do you always experience the gravitational influence of other mass as you see them in your frame?
- PowerShell manipulation of `for` results
- Question about NMAP HTTP Verb Tampering
- Using 50 Ω coax cable instead of passive probe
- Can you be charged with breaking and entering if the door was open, and the owner of the property is deceased?
- What makes Python better suited to quant finance than Matlab / Octave, Julia, R and others?
- How does a country without exit immigration check know you have overstayed?
- How to solve the intersection truncation problem of multiple \draw[thick, color=xxx] commands by color?
- Setting Stack Pointer on Bare Metal Rust
- I'm not sure what I damaged in crash. Derailleur? gears?
SinjinSmith.Net
Random things that i have learned . . ., setting a static ip address in metasploitable.
This should also work for command line IP address changes to Linux:
edit the file /etc/network/interfaces
auto eth0 iface eth0 inet dhcp
auto eth0 iface eth0 inet static address 172.16.40.10 netmask 255.255.0.0 network 172.16.0.0 broadcast 172.16.255.255 gateway 172.16.2.47 dns-nameservers 172.16.2.4 172.16.2.15
Restart neworking
sudo /etc/init.d/networking restart
- Search for:
Recent Posts
- PowerShell TBA
- Install OpenVAS on Kali Linux 2017.1
- Updated Cable Modem Baseline
- Cable Modem Baseline Stats
- WPA2 Dictionary Attack
Recent Comments
- October 2017
- October 2016
- January 2016
- February 2015
- January 2015
- December 2014
- November 2014
- October 2014
- September 2013
- Microsoft Windows
- Random Thoughts
- Raspberry Pi
- Rubber Ducky
- Uncategorized
- Entries feed
- Comments feed
- WordPress.org
- Stack Overflow for Teams Where developers & technologists share private knowledge with coworkers
- Advertising & Talent Reach devs & technologists worldwide about your product, service or employer brand
- OverflowAI GenAI features for Teams
- OverflowAPI Train & fine-tune LLMs
- Labs The future of collective knowledge sharing
- About the company Visit the blog
Collectives™ on Stack Overflow
Find centralized, trusted content and collaborate around the technologies you use most.
Q&A for work
Connect and share knowledge within a single location that is structured and easy to search.
Get early access and see previews of new features.
Static IP address set in /etc/network/interface not getting updated after rmmod and insmod
I have configured static IP address in /etc/network/interfaces file as below
But, when i try to do rmmod of the driver e1000 and then insmod again. the eth0 network interface would be loaded but, the ip address is not assigned until i explicitly do ifconfig eth0 or ifup eth0 .
I have tried adding a script in /etc/network/if-up.d/loadeth.sh which has
but, no luck the IP address is getting assigned.
My aim is that whenever i insmod the ethernet device driver i want to get the network interface( eth0 ) assigned with static IP address i have assigned in the interfaces file
Could anybody let me know what am i missing here
- linux-kernel
- network-interface
- Does adding the line allow-hotplug eth0 help? – Ian Abbott Commented Feb 17, 2021 at 16:54
- I tried allow-hotplug eth0 but, It didn't work – Sunil Kumar Commented Feb 23, 2021 at 11:02
2 Answers 2
what am i missing here
The files in /etc/network/ are parsed when when ifup or ifdown commands are executed. (I think also when ifplugd picks them up).
insmod loads a module into the running kernel.
You are missing the knowledge, that there is just no connection between insmod -ing a kernel driver and reading any files from /etc/network directory.
My aim is that whenever i insmod the ethernet device driver i want to get the network interface(eth0) assigned with static IP address i have assigned in the interfaces file
You may setup udev rule to run a custom script upon insmod -ing a kernel driver or when interface comes up.
- Could you please let me know how to setup udev rules. i tried adding rules like "SUBSYSTEM=="net", ACTION=="add", KERNELS=="0000:00:03.0", NAME=="eth0" and placed it in the /etc/udev/rules.d and /lib/udev/rules.d/ but, nothing worked – Sunil Kumar Commented Feb 23, 2021 at 11:12
- I followed the procedure mentioned in this link packetpushers.net/udev – Sunil Kumar Commented Feb 23, 2021 at 11:15
- 1 First, listen on udef events with I think udevadm monitor . Then insmod/rmmod your module and check for events. Then write a rule that will match with some debugging output to logger . Then refresh udev rules with some command. Watch journal to see if the rule is really executing. I'm am really bad at udev, it's always pain for me - once it works, it works. – KamilCuk Commented Feb 23, 2021 at 11:20
After going through man page of udev i understood how to create udev rules and with a dummy test specified in this link https://www.tecmint.com/udev-for-device-detection-management-in-linux/ i was able to invoke the udev rules when insmod -ing and rmmod -ing a driver.
So, Here's what i did to automatically set the ip address for the ethernet network interface once driver is loaded or insmod ed
I create a udev rules file named 80-net_auto_up.rules in the ethernet pcie driver recipe (it is an out of tree kernel module. Hence, custom recipe)
i added SUBSYSTEM=="net", ACTION=="add", RUN+="/sbin/ifup eth0"
and edited ethernet pcie driver recipe .bb file and added below lines
and now it works. when i reset the ethernet device manually. The device is getting detected and Static IP address configured in the /etc/network/interfaces is set
Your Answer
Reminder: Answers generated by artificial intelligence tools are not allowed on Stack Overflow. Learn more
Sign up or log in
Post as a guest.
Required, but never shown
By clicking “Post Your Answer”, you agree to our terms of service and acknowledge you have read our privacy policy .
Not the answer you're looking for? Browse other questions tagged networking linux-kernel ethernet network-interface or ask your own question .
- The Overflow Blog
- Community Products Roadmap Update, July 2024
- Featured on Meta
- We spent a sprint addressing your requests — here’s how it went
- Upcoming initiatives on Stack Overflow and across the Stack Exchange network...
- What makes a homepage useful for logged-in users
- The [lib] tag is being burninated
Hot Network Questions
- When selling a machine with proprietary software that links against an LGPLv3 library, do I need to give the customer root access?
- A manifold whose tangent space of a sum of line bundles and higher rank vector bundles
- Struggling w/ Jesus and Jewish law
- How close would a quasar have to be to be seen with the naked eye?
- Transferring at JFK: How is passport checked if flights arrive at/depart from adjacent gates?
- I'm not sure what I damaged in crash. Derailleur? gears?
- Tikz: specific tool for exploded-view drawings?
- PowerShell manipulation of `for` results
- Can you be charged with breaking and entering if the door was open, and the owner of the property is deceased?
- Simulate slow disks in KVM to see effect of LVM cache in test setup
- Decorate equations with arrows using TikZ
- How to optimize performance with DeleteDuplicates?
- Are there dedicated research facilities in the USA?
- Book about a boy who becomes a sorcerer
- firefox returns odd results for file:/// or file:///tmp
- Do you always experience the gravitational influence of other mass as you see them in your frame?
- Equivalence of inverse transformations under distributional equivalence
- 2024 UK election: Which demographic factors explain the geography?
- Why was this a draw? What move I supposed to play to win?
- The meaning of "奪耳" in 《說文解字》
- When do people say "Toiletten" in the plural?
- What is the reason for using decibels to measure sound?
- Dual citizenship with USA & South Africa and exited South Africa on wrong passport (USA). What passport do I use to reenter SA?
- Do thermodynamic cycles occur only in human-made machines?
Stack Exchange Network
Stack Exchange network consists of 183 Q&A communities including Stack Overflow , the largest, most trusted online community for developers to learn, share their knowledge, and build their careers.
Q&A for work
Connect and share knowledge within a single location that is structured and easy to search.
/etc/network/interfaces is not changing my static IP
I'm using xubuntu and I have set my /etc/network/interfaces file like this:
When I reboot the system and run ifconfig command, everything is ok:
But, when I update the /etc/network/interfaces file changing the IP to 192.168.1.20 and do this:
The ifconfig command show me the same IP (192.168.1.10) as before. Moreover, I can do a ping to both addresses and they answer.
I can't see the expected IP (192.168.1.20) until I reboot the system. Even a sudo /etc/init.d/networking restart execution can't solve that...
What am I doing wrong?
PS: I have disabled the GUI Network Manager to avoid conflicts.
EDIT : I have used sudo ifdown enp0s3 && sudo ifup -v enp0s3 and this is the result:
Every time I edit the /etc/network/interfaces , change the static IP address and restart the network, it's like if I were adding new IPs to my machine. I can ping to each one I write!!
- 1 try systemctl restart ifup@enp0s3 – pLumo Commented Jan 11, 2019 at 13:03
- 1 Which version of Ubuntu are you using? Is the result any better if you: sudo ifdown enp0s3 && sudo ifup -v enp0s3 ? – chili555 Commented Jan 11, 2019 at 16:10
- @chili555: xubuntu 18.04 LTS. I have done what you said and I have got the results you can see at my edited post (didn't work). Thanks! – Ommadawn Commented Jan 11, 2019 at 16:19
- 1 In the absence of Network Manager, in 18.04, networking is handled by netplan, not /etc/network/interfaces . Please see: askubuntu.com/questions/976464/… – chili555 Commented Jan 11, 2019 at 17:19
- 1 Not to be too blunt, but it appears that the answer is incorrect. You can use interfaces, but it takes much more than ifup/down. askubuntu.com/questions/1031709/… Be sure to read all the following comments. Isn't it just much simpler to adapt to netplan? – chili555 Commented Jan 11, 2019 at 17:37
- Check the IP with ping ;
- Then check IP, it will assign dynamically into LAN or not, If IP assign to another machine in your LAN then it will come 'IP conflict';
- If not, add static IP ( 192.168.1.20 ) in /etc/network/interfaces ;
- Then restart networking with the command service networking restart ;
- then run command ifdown enp0s3 && ifup enp0s3 if you don't want to restart.
- 1) Both addresses answer to ping. 2) No conflict, it's an isolated virtual machine with its on LAN. 3) Added. 4) I have run the command and nothing have changed. If I restart the computer, it works, but I don't want to restart! :( THanks for your help! – Ommadawn Commented Jan 11, 2019 at 15:30
You must log in to answer this question.
Not the answer you're looking for browse other questions tagged networking static-ip ..
- The Overflow Blog
- Community Products Roadmap Update, July 2024
- Featured on Meta
- We spent a sprint addressing your requests — here’s how it went
- Upcoming initiatives on Stack Overflow and across the Stack Exchange network...
Hot Network Questions
- Was I wrongfully denied boarding for a flight where the airliner lands to a gate that doesn't directly connect to the international part the airport?
- How much does a factory reset help in hiding a device's identification details?
- Using particle-hole symmetry of the Hubbard model to study the model at different densities
- Lengths of generators of surface group
- Any alternative to lockdown browser?
- Would this telescope be capable to detect Middle Ages Civilization?
- pdfgrep How to locate the pages that contain multiple strings and print the page numbers?
- How can I power both sides of breaker box with two 120 volt battery backups?
- Are there dedicated research facilities in the USA?
- Are there rules for gender of durations?
- 130 TIF DEM file (total size 3 GB) become 7.4 GB TIF file after merging. Why?
- Minimum number of select-all/copy/paste steps for a string containing n copies of the original
- Can the US president legally kill at will?
- Vacuum region in SIESTA
- What is the reason for using decibels to measure sound?
- Manga/manhua/manhwa where the female lead is a princess who is reincarnated by the guard who loved her
- Is the text of a LLM determined by a random seed?
- I'm not sure what I damaged in crash. Derailleur? gears?
- How to write a module that provides an 'unpublish comment' shortcut link on each comment
- Why does the length of an antenna matter when electromagnetic waves propagate perpendicular to the antenna?
- How to see what statement (memory address) my program is currently running: the program counter register, through Linux commands?
- Where am I wrong in my derivation of RC charging circuit equation?
- Weather on a Flat, Infinite Sea
- 11 trees in 6 rows with 4 trees in each row
How to Change Server IP Addresses for a Cluster (Multi-Node)
Article id: 291367, updated on:, issue/introduction, environment.
- EDR Server: All Versions
- Open the WebUI, then navigate to Administration > Sensors and select Edit Settings.
- Support's recommendation is to keep the default sensor communication port, 443. There are additional configuration changes that need to be made in /etc/cb/cb.conf and /etc/cb/nginx/conf.d/ in order for the sensors to communicate on a custom port.
- Repeat the step above for each sensor group if they exist.
Stop Cluster Services :
Change the server IP using normal OS commands for configuring the network interface
- Update the IP address of the master node in Postgres: (NOTE: This should also be repeated for each Minion in the Cluster IE: Minion 1 is node_id=1)
- In product versions 7.4.0 to 7.5.0:
- In product versions prior to 7.4.0:
- Update /etc/cb/ cluster.conf to match new IPs for all relevant nodes
Update /etc/sysconfig/ iptables to accept traffic from new minion IPs if applicable
- Update /etc/ hosts to redirect to match new IPs for all relevant nodes
- Change the server IP using normal OS commands for configuring the network interface if applicable
- Update psql DatabaseURL value
- Update Redis RedisHost value
- Update /etc/cb/ cluster.conf to match new IPs for new master IP (and minions if applicable)
- If CB managed firewall run the following command on master and minions /usr/share/cb/cbcheck firewall -a
- Update /etc/ hosts to match new IPs for new master IP (and minions if applicable)
- Start EDR Cluster :
- Verify that ~/.ssh/ known_hosts has been updated
- For Windows this is located at HKLM\SOFTWARE\CarbonBlack\config\SensorBackendServer
- For MacOs and Linux, this value is stored in /var/lib/cb/sensorsettings.ini
Additional Information
- There will be a delay after changing this setting as all endpoints would need to check in first to pull down the new server IP / FQDN.
- Any offline endpoints that don't check in will either need to have sensor reinstalled or registry edited to point to the new server.
- If using custom certificates, the hosts files on sensors will be updated once registry changes have been made (either via sync with new Sensor Group settings or manually changed on the sensor). If this does not take effect, a restart of sensor services should generate a new hosts file and allow connection to the server's new IP address.


How to Reset a Network Interface in Linux
In this tutorial, we will explore how to reset a network interface in Linux. Resetting a network interface can help resolve network issues, apply new settings, or refresh the network connection. This process involves bringing the interface down and back up, reloading drivers, and flushing configurations if necessary.
In this tutorial you will learn:
- How to restart a network interface
- How to reset a network interface by reloading drivers and flushing configurations

| Category | Requirements, Conventions or Software Version Used |
|---|---|
| System | Any Linux distribution |
| Software | None specific |
| Other | Access to the terminal and root privileges |
| Conventions | – requires given to be executed with root privileges either directly as a root user or by use of command – requires given to be executed as a regular non-privileged user |
Resetting a Network Interface in Linux
Resetting a network interface in Linux can involve different steps depending on the extent of the reset needed. Below, we will go through restarting the interface, reloading the network driver, and flushing IP addresses and routes.

Identify the driver associated with your interface, then unload and reload it:
Resetting a network interface in Linux can help resolve a variety of network-related issues and apply new settings. Whether you are restarting the interface, reloading drivers, or flushing configurations, the steps outlined in this tutorial provide a comprehensive guide to managing network interfaces in Linux.
Related Linux Tutorials:
- An Introduction to Linux Automation, Tools and Techniques
- Can Linux Get Viruses? Exploring the Vulnerability…
- Linux Configuration files: Top 30 most important
- Things to do after installing Ubuntu 22.04 Jammy…
- Mastering Bash Script Loops
- Things to install on Ubuntu 22.04
- MX Linux vs Ubuntu
- Advanced Logging and Auditing on Linux
- FTP client list and installation on Ubuntu 22.04…
- Linux GUI network managers
Select Product
Machine Translated
NetScaler secure deployment guide
Best practices for NetScaler MPX, VPX, and SDX security
Deployment guidelines
Configuration guidelines
Network security
Securing the pass-through traffic on NetScaler
Administration and management
System and user accounts
Logging and monitoring
LOM configuration
Applications and services
DNSSEC security recommendations
Legacy configuration
Configure NDCPP compliance certificate check
NetScaler cryptographic recommendations
Other features
Best practices for NetScaler Console security
This content has been machine translated dynamically.
Dieser Inhalt ist eine maschinelle Übersetzung, die dynamisch erstellt wurde. (Haftungsausschluss)
Cet article a été traduit automatiquement de manière dynamique. (Clause de non responsabilité)
Este artículo lo ha traducido una máquina de forma dinámica. (Aviso legal)
此内容已经过机器动态翻译。 放弃
このコンテンツは動的に機械翻訳されています。 免責事項
이 콘텐츠는 동적으로 기계 번역되었습니다. 책임 부인
Este texto foi traduzido automaticamente. (Aviso legal)
Questo contenuto è stato tradotto dinamicamente con traduzione automatica. (Esclusione di responsabilità))
This article has been machine translated.
Dieser Artikel wurde maschinell übersetzt. (Haftungsausschluss)
Ce article a été traduit automatiquement. (Clause de non responsabilité)
Este artículo ha sido traducido automáticamente. (Aviso legal)
この記事は機械翻訳されています. 免責事項
이 기사는 기계 번역되었습니다. 책임 부인
Este artigo foi traduzido automaticamente. (Aviso legal)
这篇文章已经过机器翻译. 放弃
Questo articolo è stato tradotto automaticamente. (Esclusione di responsabilità))
Translation failed!
When deploying NetScaler in a production environment, we recommend that the following key configuration changes are made:
- Do not expose the NetScaler administrator interface (NSIP) to the Internet.
- The NetScaler default SSL certificate must be replaced.
- HTTPS (HTTP over TLS) must be used when accessing the GUI and the default HTTP interface disabled.
The following section provides more information on these key considerations, in addition to the further changes that are recommended.
- Key network security considerations
Do not expose the NSIP and Management Service IP address to the Internet:
We recommend that the NetScaler Management IP (NSIP) address and Management Service IP address of SDX is not exposed to the public Internet and is deployed behind an appropriate stateful Packet Inspection (SPI) firewall.
Replace the NetScaler default TLS certificate:
During the initial configuration of NetScaler, the default TLS certificates are created. These certificates are not intended for use in production deployments and must be replaced.
We recommend that customers configure NetScaler to use certificates either from a reputable Certificate Authority (CA) or appropriate certificates from your enterprise Certificate Authority.
When bound to a public-facing virtual server, a valid TLS certificate from a reputable CA simplifies the user experience for internet-facing web applications; user web browsers require no user interaction when initiating secure communication with the web server. To replace the default NetScaler certificate with a trusted CA certificate, see Knowledge Center article CTX122521: “ How to replace the default certificate of a NetScaler appliance with a trusted CA certificate that matches the host name of the appliance .”
Alternatively, it is possible to create and use custom TLS certificates and private keys. While this action can provide an equivalent level of transport layer security, it requires the TLS certificates to be distributed to users and requires a user interaction when initiating connections to the web server. For more information on how to create custom certificates, see Knowledge Center article CTX121617: How to Create and Install Self-Signed Certificates on NetScaler Appliance .
More information on TLS certificate management and configuration can be found in the “NetScaler TLS Recommendations” section of this guide.
Disable HTTP access to the administrator interface:
To protect traffic to the NetScaler administrative interface and GUI, NetScaler must be configured to use HTTPS. Perform the following steps:
Create a 2048-bit or greater RSA private and public key pair and use the keys for HTTPS and SSH to access the NetScaler IP address, replacing the factory provisioned 512-bit RSA private and public key pair.
Configure NetScaler to use only strong cipher suites and change the ‘DEFAULT’ set of cipher suites to strong cipher suites on NetScaler. We recommend that you use the list of approved TLS Cipher suites in section 3.3 of NIST Special Publication 800-52 (Revision 1). This document can be found on the NIST website at the following address: https://www.nist.gov/publications/guidelines-selection-configuration-and-use-transport-layer-security-tls-implementations?pub_id=915295
Configure NetScaler to use SSH public key authentication to access the administrator interface. Do not use the NetScaler default keys. Create and use your own 2048-bit RSA private and public key pair. For more information, see Knowledge Center article CTX109011: How to Secure SSH Access to the NetScaler Appliance with Public Key Authentication and the NetScaler product documentation: SSH key-based authentication for local system users
Once the NetScaler has been configured to use these new certificates, HTTP access to the GUI management interface can be disabled with the following command:
For more information on how to configure secure access to the Administration GUI, see the Knowledge Center article CTX111531: How to Enable Secure Access to NetScaler GUI Using the SNIP/MIP Address of the Appliance .
- Other network security considerations
Limit VPX shell access of VPX administrators who are not trusted to manage the SDX:
In situations where it is desirable to have a different person administer a VPX to that of the Management Service, the Management Service administrator must create a VPX admin user which has limited shell access on the VPX and only provide the restricted admin user account to the VPX administrator.
Some operations might require shell access (such as administering SSL certificates). However, only individuals who are trusted to administer the SVM must be granted access to the VPX instance shell. RBAC level commands, listed later in this section, can be assigned to those accounts. These recommendations are applicable for all SVM-IP/VPX-NSIP (L2/L3) management workflows and must be followed for secure access auditing purposes.
The following steps can be used to remove shell access from a VPX admin.
Securing an existing VPX instance:
Log in to the VPX CLI as nsroot or superuser.
We recommend not to use the nsroot account and instead create a superuser account. When using the nsroot account, ensure that the passwords are strong with special characters. For details on strong passwords, see Administration and management .
- Create a user and an RBAC policy in a VPX instance on NetScaler SDX.
- Bind that user to the policy.
Note: In this example, the system cmdpolicy (ex: cmdpolicy name: shell) is created to deny shell access. This policy is bound to the user userabc with priority high. Default superuser cmdpolicy is also bound as lower priority to the system user. With this configuration, the new system user has superuser RBAC policies but shell access is denied.
- Verify that the current user has applied the RBAC policies.
- Run any commands that the user is authorized to. (for example, show system cmdpolicy )
- Run the shell command to verify that shell access is restricted.
login as: userabc
Pre-authentication banner message from server:
In the console of that VPX, log in as that user and make sure that the shell access is not allowed for this user:
Log in as regular admin user ( nsroot ) and make sure that shell access is allowed:
Securing a new VPX instance:
When a new VPX instance is created from the Management Service GUI, create an INSTANCE ADMIN user, and clear the Shell/SFTP/SCP Access checkbox. On disabling shell access, svm_access_policy (action DENY) is bound explicitly to the specified instance admin user.
Provide this user information to the VPX admin. The SDX admin must retain this nsroot admin password and must not share it with the VPX admin.
- To change the nsroot password, log on to Management Service, select the instance, and change the password. Never change the nsroot password from the VPX CLI.
- For details about RBAC users, see User, user groups, and command policies .
- For modifying the password of NetScaler from SVM, see Modify a NetScaler instance .
- For provisioning NetScaler with instance administration, see Add a NetScaler instance .
Disable SSH port forwarding:
SSH port forwarding is not required by NetScaler. If you do not want to use this functionality, then we recommend that you disable it by using the following steps:
Edit the /etc/sshd_config file by adding the following line:
AllowTcpForwarding no
Save the file and copy it to the /nsconfig directory to ensure that the changes are persistent in case you reboot during the tests.
Restart the sshd process by using the following command:
Configure NetScaler with high availability:
In deployments where continuous operation is required, NetScaler can be deployed in a high availability setup. Such a setup provides continued operation if one of the NetScaler stops functioning or requires an offline upgrade.
For information on how to configure a high availability setup, see Configuring high availability .
Set up secure communication between peer appliances:
If you have configured your NetScaler in a high availability, cluster, or GSLB setup, secure the communication between NetScaler appliances.
To secure communication, we recommend that you change the internal user account or RPC node password, and enable the Secure option. RPC nodes are internal system entities used for system-to-system communication of configuration and session information.
NetScaler features can also use an SSH key-based authentication for internal communication when the internal user account is disabled. In such cases, the key name must be set as “ns_comm_key”. For more information, see Access a NetScaler appliance by using SSH keys and no password .
Change the default passwords:
For enhanced security, we recommend that you change the administrator, and internal user account or RPC node passwords for both on-premises and cloud deployments. Frequently changing the passwords is advisable.
- Administrator password: See Change administrator password .
Note We also recommend that you disable the internal user account and instead use the key-based authentication.
Configure network security domains and VLANs:
We recommend that network traffic to NetScaler management interface is separated, either physically or logically, from normal network traffic. The recommended best practice is to have three VLANs:
- Outside Internet VLAN
- Management VLAN
- Inside server VLAN
We recommend configuring the network to make the LOM port part of the management VLAN.
When deploying NetScaler in two-arm mode, dedicate a specific port to a specific network. If VLAN tagging and binding two networks to one port is required, you must ensure that the two networks have the same, or similar, security levels.
If the two networks have different security levels, VLAN tagging must not be used. Instead, consider dedicating a port for each specific network and use independent VLANs distributed over the ports on NetScaler.
Consider using NetScaler Web App Firewall: A Premium edition licensed NetScaler provides a built-in NetScaler Web App Firewall that uses a positive security model and automatically learns the proper application behavior for protection against threats such as command injection, SQL injection, and Cross Site Scripting.
When you use NetScaler Web App Firewall, users can add extra security to the web application without code changes and with minimal change in configuration. For more information, see Introduction to NetScaler Web Application Firewall .
Restrict non-management applications access : Run the following command to restrict the ability of non-management applications to access NetScaler.
Secure cluster deployment: If NetScaler cluster nodes are distributed outside the data center, we recommend that you use secure RPC for Node to Node Messaging (NNM), AppNNM, and a high availability setup.
To enable the Secure RPC feature for all NetScaler IP addresses in a NetScaler Cluster and a high availability setup, run the following command:
Note : Other configurations might be required. For more information, see the Clustering topics on the Product Documentation .
When deployed in an L3 cluster deployment, packets between NetScaler nodes are exchanged over an unencrypted GRE tunnel that uses the NSIP addresses of the source and destination nodes for routing. When the exchange occurs over the internet, in the absence of an IPsec tunnel, the NSIPs are exposed on the internet, which is not recommended as it doesn’t comply with the security best practices for NetScaler.
̇We recommend that customers establish their own IPsec solution to use the cluster over the L3 feature.
If the IP forwarding feature is not in use, use the following command to disable L3 mode:
Use secure MEP for global server load balancing (GSLB): To encrypt the MEP between NetScaler for GSLB, run the following command from the NSCLI:
Secure the load balancing persistence cookie:
We recommend encrypting the load balancing persistence cookie in addition to the SSL/TLS channel. For more information, see HTTP cookie persistence .
Helloverifyrequest parameter to mitigate the DTLS DDoS amplification attack:
Starting from NetScaler release 12.1 build 62.x and release 13.0 build 79.x, the helloverifyrequest parameter is enabled by default. Enabling the helloverifyrequest parameter on the DTLS profile helps mitigate the risk of an attacker or bots overwhelming the network throughput, potentially leading to outbound bandwidth exhaustion. That is, it helps mitigate the DTLS DDoS amplification attack.
To view the helloverifyrequest parameter status, at the CLI prompt, type:
In this article
This Preview product documentation is Cloud Software Group Confidential.
You agree to hold this documentation confidential pursuant to the terms of your Cloud Software Group Beta/Tech Preview Agreement.
The development, release and timing of any features or functionality described in the Preview documentation remains at our sole discretion and are subject to change without notice or consultation.
The documentation is for informational purposes only and is not a commitment, promise or legal obligation to deliver any material, code or functionality and should not be relied upon in making Cloud Software Group product purchase decisions.
If you do not agree, select I DO NOT AGREE to exit.
Machine Translation Feedback Form
Do you want to switch to the website in your browser preferred language?
Edit Article

IMAGES
VIDEO
COMMENTS
WRITE FOR US. LinuxConfig is looking for a technical writer(s) geared towards GNU/Linux and FLOSS technologies. Your articles will feature various GNU/Linux configuration tutorials and FLOSS technologies used in combination with GNU/Linux operating system.
address 192.168.1.5. netmask 255.255.255.. gateway 192.168.1.254. Setup interface to dhcp. To setup eth0 to dhcp, enter: auto eth0. iface eth0 inet dhcp. If you're new to Ubuntu, or Linux in general, I recommend you bookmark that site. He has a lot of great articles and tutorials that will help you out.
Physical interface names should follow the word "auto" on the same line. There can be multiple "auto" stanzas. ifup brings the named inter faces up in the order listed. For example following example setup eth0 (first network interface card) with 192.168.1.5 IP address and gateway (router) to 192.168.1.254: iface eth0 inet static.
a specific IP address; full control over the address assignment; Since the Dynamic Host Configuration Protocol (DHCP) can take the Media Access Control (MAC) address into account when assigning the network-layer address, we might still automatically receive the same IP on each connection with that protocol.
Save and close the file when using vim/vi text editor.. Restart networking service on Debian Linux to switch from DHCP to static IP config. Warning: Do not run the following over ssh based session as you will disconnect.. Use the systemctl command as follows: $ sudo systemctl restart networking.service Make sure service restarted without any errors. Hence, type the following command: $ sudo ...
3 ways to configure the network. Setting up an Ethernet Interface. Starting and Stopping Interfaces. Reinitialize new network setup. Network Interface Names. Using DHCP to automatically configure the interface. Configuring the interface manually. Setting the speed and duplex. Bringing up an interface without an IP address.
Change them to instead be: (example IP addresses) auto eth0 #iface eth0 inet dhcp iface eth0 inet static address 192.168..130 netmask 255.255.255. network 192.168.. broadcast 192.168..255 gateway 192.168..1 dns-nameservers 192.168..1 Then re-start your server. It should now be using: 192.168..130
To set up a static IP address on Debian 12 using nmtui, follow these steps: Step 1: Launch nmtui Interface. First, type " nmtui " command to launch the interface, use the arrow keys, and Enter key to navigate through the menus and options. Step 2: Edit a Connection. Select " Edit a connection " option and press Enter:
There are many cases in which we may want to set a static IP for a network interface. In RHEL 8 / CentOS 8, the network connections are managed by the NetworkManager daemon, so in this tutorial we see how we can perform such task by editing an interface file directly, by using a command line utility, nmcli, or via a text user interface, nmtui.. In this tutorial you will learn:
Identify Your Network Interface: To set a static IP address, you first need to know which network interface you're configuring. $ nmcli d Identify Your Network Interface. This command lists all network interfaces on your system. Note the interface name you plan to configure, such as 'enp0s3'.
An IP address is a number used to identify a network interface on a computer on a local network or the Internet. In the currently most widespread version of IP (IPv4), this number is encoded in 32 bits, and is usually represented as 4 numbers separated by periods (e.g. 192.168..1), each number being between 0 and 255 (inclusive, which corresponds to 8 bits of data).
sudo systemctl restart networking. and then check the IP address to verify that your new settings have applied: ip a. The output should look similar to this: If we check the eth0@if2 interface again, notice that the address is now the static IP I've specified and it is no longer showing as being dynamic.
Depending on the interface you want to modify, click either on the Network or Wi-Fi tab. To open the interface settings, click on the cog icon next to the interface name. In "IPV4" Method" tab, select "Manual" and enter your static IP address, Netmask and Gateway. Once done, click on the "Apply" button.
@Thuemaychuaonet, If your server is connected only via WiFi, the network interface will likely have a different name, such as `wlan0` or something similar, depending on your system and its configuration. The steps to set a static IP address and configure the network are similar, but you'll need to use the correct interface name for your WiFi connection.
address - IP address for a static IP configured interface. netmask - Network mask. Can be omitted if you use cidr address. Example: iface eth1 inet static address 192.168.1.2/24 gateway 192.168.1.1 gateway - The default gateway of a server. Be careful to use only one of this guy.
You should be able to add a static ip address in the interfaces file, e.g. : auto lo iface lo inet loopback auto enp0s31f6 iface enp0s31f6 inet static address 192.168.1.100 gateway 192.168.1.1 netmask 255.255.255. dns-nameservers 12.34.56.78 12.34.56.79
To configure a default gateway, you can use the ip command in the following manner. Modify the default gateway address to match your network requirements. sudo ip route add default via 10.102.66.1. You can also use the ip command to verify your default gateway configuration, as follows: ip route show.
If I'm understanding your question, to set a static IP, your network runs from 191.168.16.1 - 191.168.31.254, with the identity address at 192.168.16. and the broadcast at 192.168.31.255. I've never had to use the Network keyword, but I've never used a supernet address on a host. I've only seen them used for route aggregation.
For more information, see interfaces(5). # The loopback network interface auto lo iface lo inet loopback # The primary network interface auto eth0 #iface eth0 inet dhcp iface eth0 inet static address 192.168.1.121 netmask 255.255.255. gateway 192.168.1.1 and restart eth0 interface $ sudo ifconfig eth0 down $ sudo ifconfig eth0 up but the eth0 ...
This should also work for command line IP address changes to Linux: edit the file /etc/network/interfaces. Change: auto eth0 iface eth0 inet dhcp. To:
You are missing the knowledge, that there is just no connection between insmod-ing a kernel driver and reading any files from /etc/network directory. My aim is that whenever i insmod the ethernet device driver i want to get the network interface(eth0) assigned with static IP address i have assigned in the interfaces file
Stack Exchange Network. Stack Exchange network consists of 183 Q&A communities including Stack Overflow, the largest, most trusted online community for developers to learn, share their knowledge, and build their careers.. Visit Stack Exchange
Update /etc/hosts to redirect to match new IPs for all relevant nodes; 4. Run these commands after all online sensors have checked in: Update Minions from the Command Line: Change the server IP using normal OS commands for configuring the network interface if applicable; Update /etc/cb/cb.conf to match new master IP Update psql DatabaseURL value
Replace <interface_name> with the name of your network interface (e.g., eth0, wlan0). This command will bring the interface down and then back up, effectively restarting it. Using the ip command: Another method to restart the network interface using the ip command. # ip link set down <interface_name> # ip link set up <interface_name>
HTTPS (HTTP over TLS) must be used when accessing the GUI and the default HTTP interface disabled. The following section provides more information on these key considerations, in addition to the further changes that are recommended. Key network security considerations. Do not expose the NSIP and Management Service IP address to the Internet: